A2SV is an open-source Python tool that automatically scans SSL vulnerabilities including CCS injection, HeartBleed, FREAK, Logjam, CRIME, Anonymous Cipher, SSL v2 Drown, and SSL v3 POODLE. CCS is a short form of ChangeCipherSpec messages exchanged during SSL connection. CCS messages indicate that the communication between two nodes (machines) is encrypted now. CCS is however vulnerable to eavesdropping, allowing the attacker to enforce weak SSL keys. The attacker, later on, can decrypt theses weak keys. HeartBleed is an OpenSSL cryptographic software library vulnerability that makes it easier to steal the protected information. POODE is Padding Oracle On Downgraded Legacy Encryption attack that takes advantage of SSL v3 vulnerabilities. FREAK is Factoring Attack on RSA-EXPORT Keys CVE-2015-0204. Logjam is a Diffie-Hellman key exchange vulnerability that tricks user into using weak encryption. CRIME is Compression Ratio Info-leak Made Easy attack capable of session hijacking over secure (HTTPS) connections. Anonymous cipher is cipher suites with no authentication keys. Anonymous cipher are vulnerable to man in the middle attack. DROWN is a short form of Decrypting RSA using Obsolete and Weakened Encryption. It takes advantage of SSL v2 vulnerabilities to attack servers that support modern SSL/TLS versions. A2SV tool can automatically assess the possibility of these vulnerabilities in a target website, server, or application that supports SSL prototol.
How to Install A2SV?
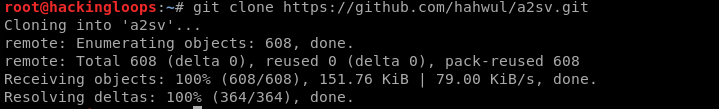
A2SV source code can be downloaded from Github repository using the following command.
git clone https://github.com/hahwul/a2sv.git
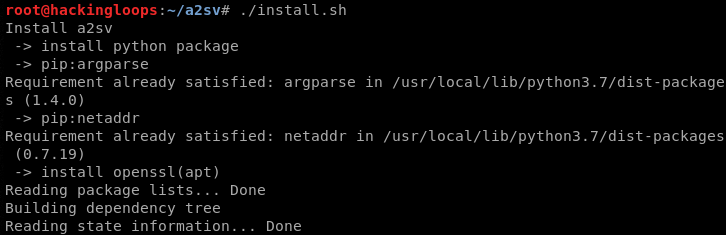
We can either install A2SV by executing the install.sh file from the source code package or run the tool directly using the main Python file (a2sv.py). The following command installs the tool along with its prerequisites.
./install.sh
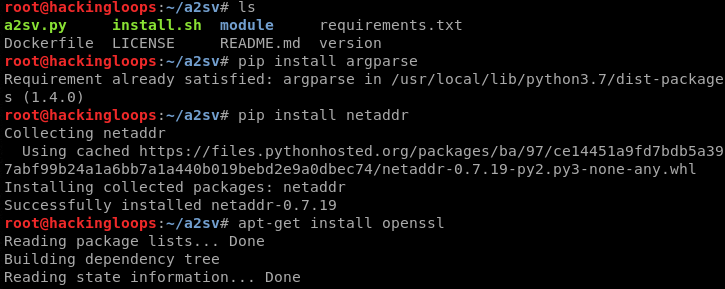
We can ignore the installation and manually install the following dependencies.
pip install argparse pip install netaddr apt-get install openssl
How A2SV Works?
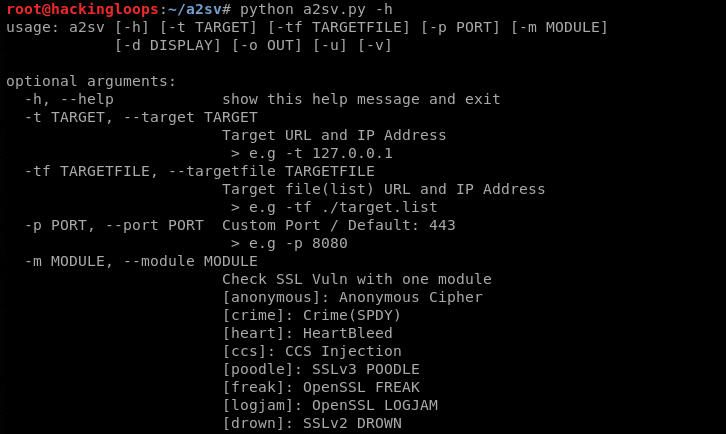
A2SV is packed with different modules to perform the aforementioned scanning tasks. These modules and usage options can be explored using the help command.
python a2sv.py -h
We can simply use the following syntax to perform tests.
python a2sv -t <target url or IP> -m <module name>
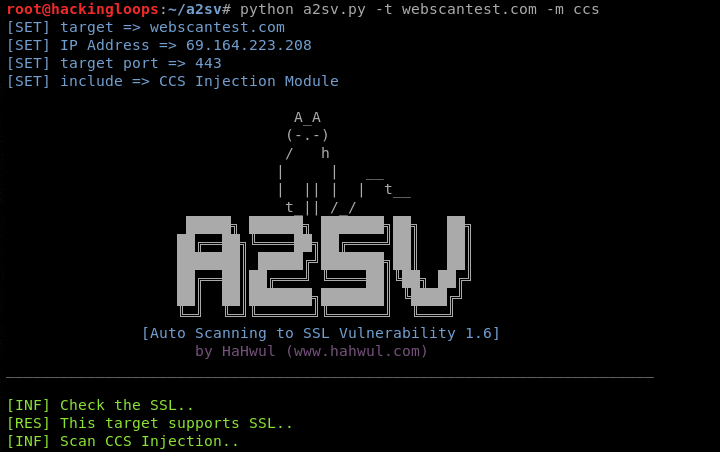
For instance, we can assess the possibility of CCS injection in target website using the following command.
python a2sv.py -t webscantest.com -m ccs
A2SV maps the url to its IP address to perform the scanning. The tool first confirms that the target IP address supports SSL protocol. If the target does not support SSL, the scanning process halts with an error.
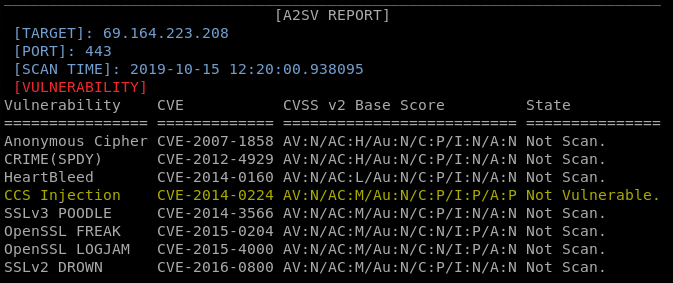
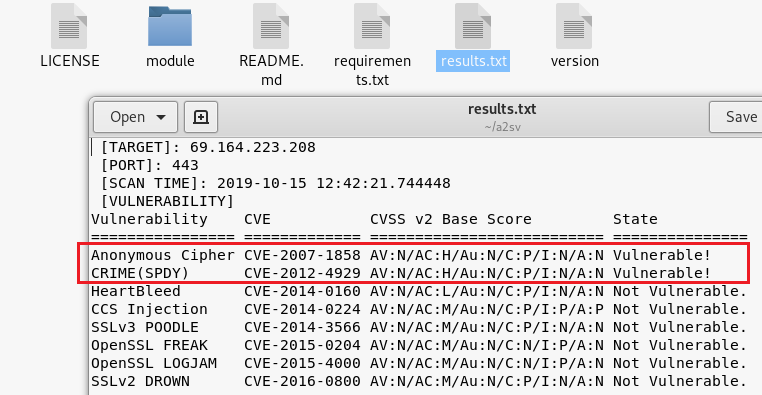
The scanning result is displayed on the screen in the following format.
The default port used to interact with target is 443. We can change the port using the -p option.
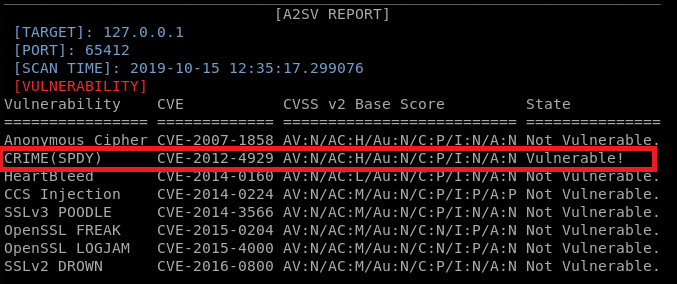
python a2sv.py -t 127.0.0.1 -p 65412 -m CRIME
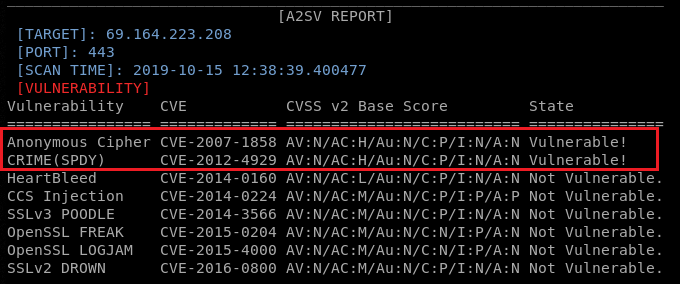
The following syntax is used to run all the modules automatically to perform the scanning process.
python a2sv.py -t <target url or IP>
The above command runs all the modules supported by A2SV to find the associated SSL/TLS vulnerabilities.
Instead of displaying results on the screen, we can instruct the tool to save results in a text file using the following command.
python a2sv.py -t <target url or IP> -o <filename.txt>
The output file is generated in the working directory containing the same results/information as displayed on the interface screen.
Summary
A2SV is a smart SSL vulnerability scanner that can analyze the often-neglected but serious SSL vulnerabilities with in no time.