Welcome back my fellow hackers! Today we’re going to be introducing a new tool for hacking web browsers. Often times, we will need to exploit a variety of vulnerabilities associated with web browsers. For this sort of exploitation, we can use a popular tool named BeEF (Browser e Exploitation Framework).
How BeEF works is actually fairly easy to understand. There is a JavaScript file provided by BeEF, simply named hook.js. Our job as the attacker is to find a way to run this JavaScript on the victim’s browser. Once it’s been run, we will have control over their browser in various aspects. There are multiple ways we can execute this script. For example, we could set up a phishing page with the hook inside of the HTML code, or we could inject it into their traffic using a Man in the Middle attack. But today we’re just going to be using the demo page provided by BeEF.
What’s really frightening about these attacks is that they aren’t encumbered by network security in the same way that other attacks, such as viruses and malware, are restricted. For instance, consider that all an XSS attack needs to succeed is an exploitable web browser and HTTP. HTTP is open on just about every network, since shutting it down means that connected users wouldn’t be able to browse the Internet.
As such, XSS attacks aren’t nearly as restricted by firewall rules and similar security policies. BeEF can penetrate one or more browsers, and then command those browsers to launch ancillary code designed to carry out further attacks.
BeEF isn’t so much of a security tool as it is a complete framework for exploiting flaws in web browsers. In this sense, it’s much like Metasploit, which is also a framework of code modules that allow people to develop their own code to exploit the latest and greatest vulnerabilities. So, let’s get started!
Step 1: Start up and Login to BeEF
If we’re going to use BeEF, we need to start it! If you’re using Kali 2, you can find BeEF on the dock. If you are aren’t using Kali 2, you can launch BeEF by enter the following command:
service beef-xss start
Now that we’ve started BeEF, we need to login. If we point our web browser at the localhost on port 3000 with the /ui/authentication URI, we will see the BeEF login page (In short: 127.0.0.1:3000/ui/authentication). When we see this page, we need to enter the default credentials in order to use BeEF. The default username and password are both “beef.” Let’s go ahead and log in now:
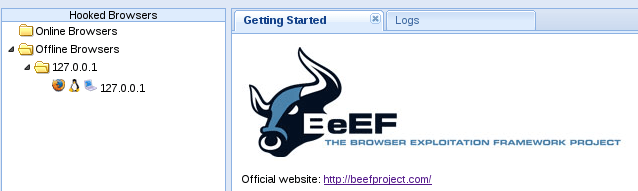
Alright, now that we’ve entered our credentials and logged in, we can see the first page. Let’s take a look at this page and then we’ll break it down:
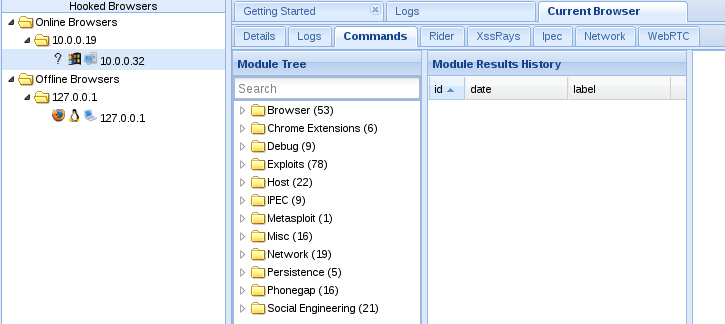
Now, to our immediate left we can see a section named “hooked browsers.” This is where BeEF will list all the browsers we currently have under our control. There is only one victim here at the moment, which is ourselves. Now that we’ve logged in and seen the start page, let’s move on to hooking our victim.
Step 2: Hook the Victim
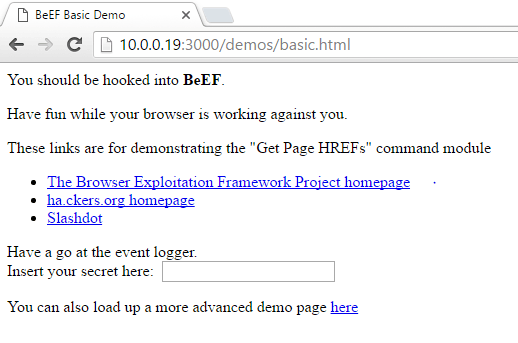
Now that we have BeEF up and running, we need to hook the victim so that we can control their browser. We will be using the BeEF demo page to run the hook. Now we need to move the victim and navigate to the demo page. The demo page can be accessed in the browser by entering the address of the attacking system on port 3000 under /demos/basic.html. So, for our demonstration today, we need to enter 10.0.0.19:3000/demos/basic.html on our victims browser, let’s do that now:
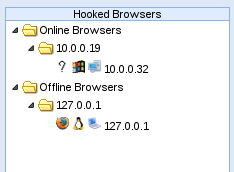
Now that we’ve navigated our victim to the demo page containing the BeEF hook, we should see them appear under the “hooked browsers” section we saw earlier:
There we go! We’ve successfully hooked our victims browser. Now that we have some basic control over it, we can do many things that will aid us in compromising this victim.
For further context the term for successfully exploiting a web browser is called “hooking” it. Naturally, since you’re a law abiding citizen with strong ethics and a moral conscience, you’re not going to try to hook other people’s web browsers. However, if you have access to a server to be used for testing purposes (such as one on your home network), you can attempt to hook browsers across the local LAN.
In order for a web browser to be “hooked,” you need that client to visit a web application that is vulnerable. Once the script is downloaded and run within their browser, you can do a lot of nasty things to further attack the system. BeEF comes with a file called hook.js. If you can get another system on your local network to execute this JavaScript file, you’ll be able to see the new browser appear in the left hand pane.
The key to success with BeEF is to “hook” a browser. This basically means that we need the victim to visit a vulnerable web app. This injected code in the “hooked” browser then responds to commands from the BeEF server. From there, we can do a number of malicious things on the victim’s computer.
Step 3: Wreak Havoc
After a browser is hooked (from running the hook.js file) and appears in the left pane, you can click on that browser and then click on the “commands” tab in the main pain. There are a smattering of different commands you can execute that facilitate the following objectives:
- stealing a list of visited websites
- stealing private browser data and history data
- access the webcam
- steal all the cookies in the browser
- steal contact information from Google contacts
- many, many other attacks
Now that we can control our victims browser, we’re going to demonstrate the kind of things we can do. We’re simply going to use some JavaScript to find out what plugins are installed on the browser. First, we need to select our victim and navigate to the “commands” tab of BeEF’s GUI. Let’s see what this looks like now:
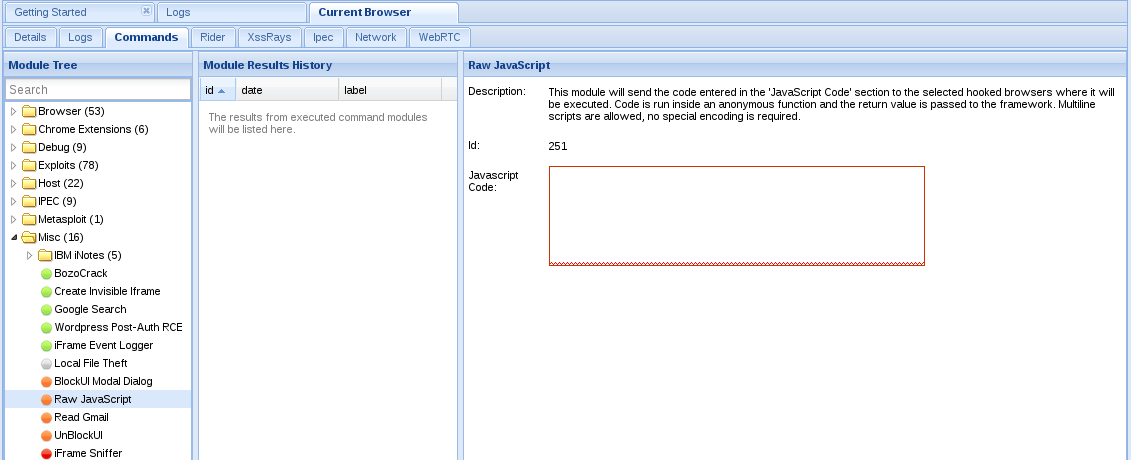
Now that we’ve navigated to our commands tab, we can look through all of the possible commands we can execute on the victim’s browser. Please note that not all of these will work as some of them are circumstance specific. The one we’re after in this instance is the raw javascript module. We can find this module under the “Misc” folder in the commands tab. Let’s select this module now:
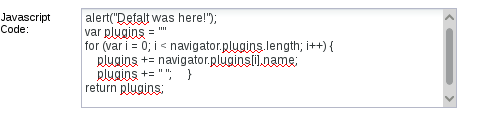
We can see that in this module we have a box to enter some JavaScript. In order to see the plugins that the victim has, we’re going to return some information out the the “navigator” object using our code. We’re also going to make an alert box appear in the victim’s browser, just for fun. Let’s take a look at this code now:
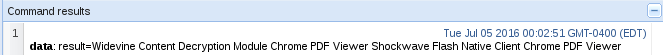
Now that we have entered our code to execute, we simply need to press the “execute” button on the bottom right of the BeEF page. Once we do this, we should see the JavaScript return an array containing the currently installed plugins. Let’s execute our code and see the results now:
Here can see a list of all the plugins that the victim has installed on their browser! We could look deeper and see if there any exploitable vulnerabilities in these plugins, but that’s best discussed later. Now that we have our results, let’s move back to the victim and take a look at our alert box!
There we have it! We were not only able to successfully hijack our victim’s browser, but we were able to extract information from it that could open a future avenue for attack! As we’ve demonstrated here today, browser hijacking can be extremely useful to any hacker looking for a way into a system. Not only is it good for finding the vulnerabilities, but in some cases we can use it to exploit them as well.
I hope this sheds some light on how big of a threat XSS attacks are. Unless you’re running some Internet security software on your computer, it’s likely that you have already been the victim of an XSS attack. With sophisticated tools like BeEF, it’s a pretty simple matter to hack into other machines. Of course, last but no least, make sure to only perform these attacks on your own home lab or have authorization from the party you are conducting the penetration test for.