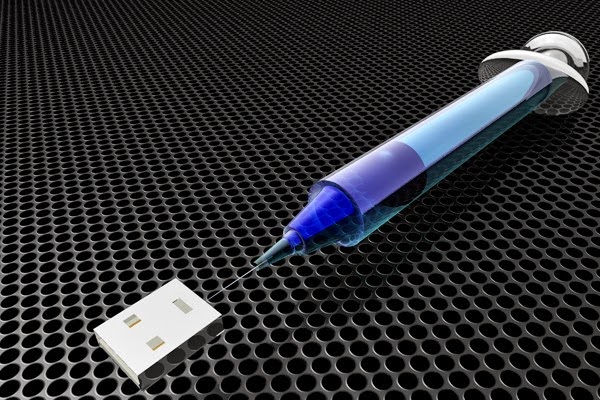
Injection attacks are the most popular attacks among hackers, topping OWASP’s Top 10 Vulnerability list every year. Injection is an entire class of attacks that rely on injecting data into a web application in order to facilitate the execution or interpretation of malicious data in an unexpected manner. So friends, let’s learn about injection attacks from the very beginning.
Injection attacks are popular because of its 4 basic things:
1. Easy to exploit
2. Hard to secure (i.e. compromise on dynamic query usage).
3. Coder’s negligence ( i.e. deciding character set, stored procedures usage issues, handling escape sequences etc.).
4. Unawareness of secure coding practices among developers.
 |
| Injection Attacks |
So its not wrong to say:
” Security does not suffer because of Hackers, it actually suffers due to lack of secure coding awareness among Coders”.
In this Injection Attacks Tutorial, I will share different types of the most common injection attacks that are quite common among Hackers. In the future, I will share in detail about these injection techniques and how to prevent these attacks.
What is Injection?
Injection, as the word implies, is injecting something extra into the code. Injection attacks allow an attacker to inject code into a program or query or inject malware onto a computer to execute remote commands that can read or modify a database, or change data on a web application or website. Injection attacks are dangerous because they are an open windows for hackers to enter in your system through your web interface and do whatever they like i.e. delete tables, modify databases, exposing your users information, or even get hold of your corporate network.
When does an injection attack occurs? Where does it usually occur? What is its impact?
Injection attacks occurs when an application sends untrusted data ( i.e. data which is not intended to behave as it should or simply we can say data which the system is not expecting) to an interpreter or compiler. Injection flaws are usually found in SQL, LDAP, Xpath, OS commands(i.e. shell command Injection), XML parsers, SMTP Headers, program arguments, etc. Injection can result in data loss or corruption, lack of accountability, or denial of access. Injection can sometimes lead to complete host takeover. If your web application uses any of these, then there are chances of SQL Injection.
Different Type of Injection Attacks:
1. SQL Injection ( Blind SQL Injection and SQL Injection)
2. Code Injection (or Remote file Inclusion)
3. Log Injection
4. Directory Traversal (or Path Traversal)
5. XML or xPath Injection
6. SOAP Injection
7. Command Injection
8. LDAP Injection
9. SSI Injection (Server Side Inclusion)
10. Buffer Overflow
11. String Format Attack
We will discuss all above topics in detail in later articles. So keep connected and enjoy learning.

Leave a Reply