Mobile Hacking Tricks for Penetration Testing: During Penetration tests, we often need to conduct social engineering attacks on a user’s mobile phone. Any attack in a penetration test begins with social engineering. This post is about how mobile tricks can be used for conducting penetration tests.
Mobile Hacking Tricks:
Mobile Hacking Tricks 1: Call Forging
To call someone from their own number or any number.
1. Go to http://www.mobivox.com and register there for an account.

Mobile Hacking Tricks – Call Forging
2. During registration, remember to insert the victim’s mobile number in the “phone number” field.
3. Complete registration and confirm your email id and then log in to your account.
Click on “Direct WebCall.”
4. You will arrive at page shown below. In the “Enter a number” box, select your country
and also any mobile number (you can enter your own). Now, simply select the “Call Now”
button to call your friend with his own number.
5. That’s it. Your friend will be shocked to see his own number calling him. I have
spent last two days playing this cool mobile hack prank.
Mobile Hacking Tricks 2:
Trace Mobile Location:
Click On The Below Link To Trace Unknown Number ->
Trace Mobile Location
This can be very useful when you need to identify the geographic area of the victim. This can give you an idea about the location of the victim and you can enact even more targeted attacks on the victim in a penetration test.
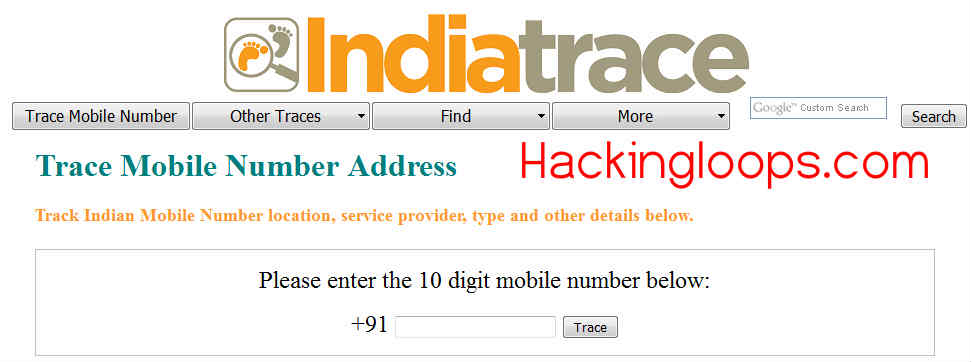
On the contrary, feel free to use the added features on this website:

Mobile Hacking Tricks 3:
Spoof Tooph 0.5: To Automate Cloning of Bluetooth devices
SpoofTooph is designed to automate spoofing or cloning a Bluetooth device’s Name, Class, and Address. Cloning this information effectively allows Bluetooth devices to hide in plain site. Bluetooth scanning software will only list one of the devices if more than one device in range shares the same device information when the devices are in Discoverable Mode (specifically the same Address)
Change Log v0.5:
– Fixed segmentation fault in manual assigning of Device Name and Class of Device
– Modified flags
– Depreciated
-r: Assign random NAME, CLASS, and ADDR
-l : Load SpoofTooph CSV logfile
-d: Dump scan into SpoofTooph CSV logfile
– New
-w: Write to CSV file
-r: Read from CSV file
-R: Assign random NAME, CLASS, and ADDR
-m: Specify multiple interfaces during selection
-u: USB delay. Interactive delay for reinitializing interfaces
Download Link: Click Here to download from Sourceforge
Here is a list of what you can do when you have hacked the other phone!
- Read Messages.
- Read Contacts.
- Change Profile
- Play Ringtone even if the phone is silent
- Play songs from the hacked phone in the same phone.
- Restart the phone
- Switch off the phone
- Restore Factory Settings
- Change Ringing Volume
#Use only for legit Purposes.

Dev says
Hello sir,
which school/institute is best for ceh course in india. pls help me sir.