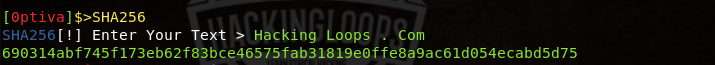
Optiva framework is a web application penetration testing tool used for information gathering and vulnerabilities analysis. Optiva framework can gather open ports information, WHOIS record, reverse IP data, HTTP header information, and geo location of the target web applications. The framework can detect SQL injections, cross site scripting (reflected and JSONP attacks), and Remote Code Execution (RCE) attacks. The tool also searches for admin panel links through bruteforce attack. Dorking feature is also available in the tool to search for web applications that are vulnerable to SQL injection. Apart from these utilities, Optiva framework can also create message digests of desired text. Optiva framework supports MD5, SHA256, SHA384, and SHA512 hash functions.
Optiva Framework Installation
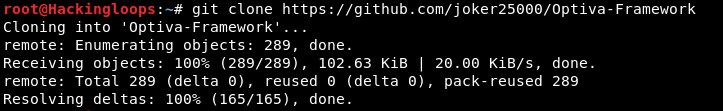
To install Optiva framework, first clone the framework’s directory from github repository using the following command.
git clone https://github.com/joker25000/Optiva-Framework
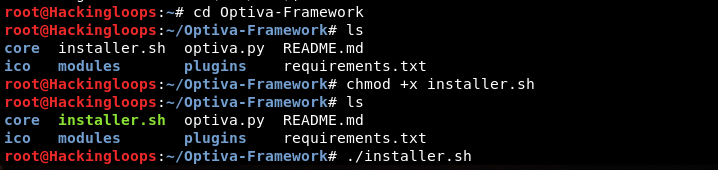
In the next step, navigate to the Optiva-Framework directory and change permission rules for the installer.sh file.
cd Optiva-Framework chmod +x installer.sh
Run the installer.sh file and follow the instructions to complete the installation process.
How Optiva Framework Works
Optiva framework can be initialized using the following command.
python optiva.py
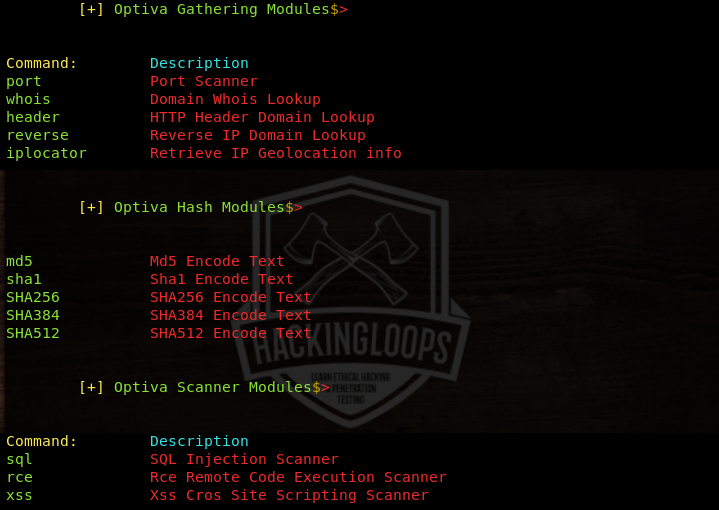
To perform the aforementioned penetration testing tasks, Optiva framework uses modules divided into three categories namely information gathering, scanner, and hash modules. The following command lists all the modules available in Optiva framework.
show modules
Each module can be set into action by typing the command mentioned against each module. The following screenshot shows the commands required to run each module.
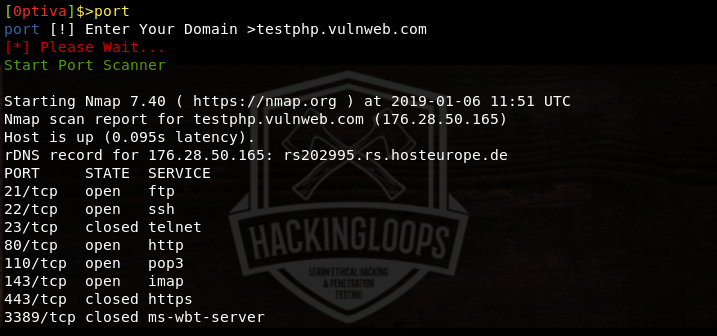
For example, to run the port scanning module, we use the following command.
port
Optiva asks for the target domain to scan the open ports and running services. Provide the target web application and press the return key to initiate the port scanning process. The results are displayed in the following format.
The same approach can be applied to the rest of the modules. For instance, HTTP header domain lookup module can be initialized using the following header command.
header
The module fetches the domain header information shown in the following screenshot.
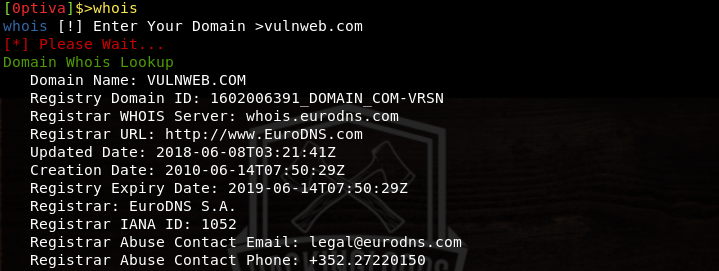
The WHOIS lookup domain module gathers information, such as domain registration data, registrar information, domain creation and expiry date, and nameservers information.
The IP locator module gathers useful geo location information about the target web application including IP address, ISP, region, country, city, map coordinates, zip code, and time zone information.
Besides information gathering modules, we can run the scanner modules to find out the web application vulnerabilities including SQL, XSS, and RCE bugs. In order to find out the SQL vulnerabilities, select the SQL scanner using the following command.
sql
The SQL scanner has a number of payloads to test the web applications security. Optiva runs all the available sql payloads to find out the injection points in the target web application. If target web application is vulnerable to SQL injection, Optiva shows all the payloads that can be successfully injected in the target web application.
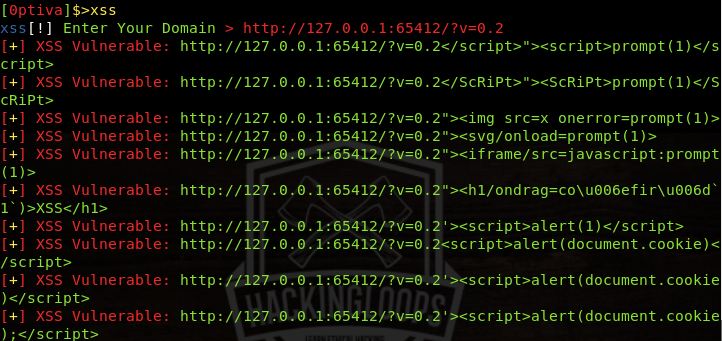
Optiva framework can detect reflected and JSONP types cross site scripting vulnerabilities. To run the cross site scripting module, run the following command.
xss
The following screenshot shows results of reflected XSS vulnerability analysis for a test website.
Besides information gathering and vulnerabilities assessment, Optiva framework can perform some other useful tasks, such as Dorking and hash generation.
Conclusion
Opitva framework produces detailed results using information gathering modules. The scanner modules not only detect vulnerabilities but also show the payloads that can exploit the target web applications successfully.