Leviathan is a network auditing toolkit that can perform a number of penetration testing tasks, such as discovering network machines, identifying vulnerable hosts, finding compromised machines, enumerating the services (protocols) running on the network machines, and discovering the possibility of network attacks through attacks simulation. The services (network protocols) that can be identified with Leviathan include FTP, Telnet, SSH, RDP, and MYSQL. The attacks include bruteforce, custom exploits, and remote command execution attacks. The bruteforce is applied against the mentioned services (FTP, Telnet, SSH, RDP, MYSQL). The custom exploit utility allows running custom exploit against pre discovered target machines. Similarly, the remote command execution allows executing commands remotely on the vulnerable machines discovered in the network. Apart from these tasks, Leviathan can also check SQL vulnerabilities on pre-discovered urls.
Leviathan Installation
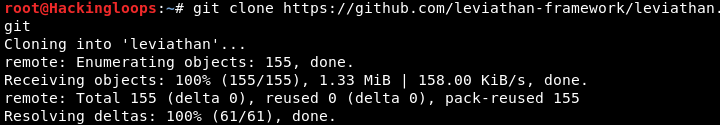
Leviathan can be cloned from Github using the following command.
git clone https://github.com/leviathan-framework/leviathan.git
Leviathan requires the following packages to operate.
Paramiko
lxmlgoogle-api-python-client
Shodan
bs4
requests
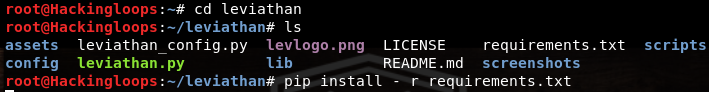
These packages can be installed by navigating to the tool’s directory and running the following pip command.
cd leviathan pip install –r requirements.txt
How Leviathan Works
The following command initiates Leviathan tool in the terminal.
python leviathan.py
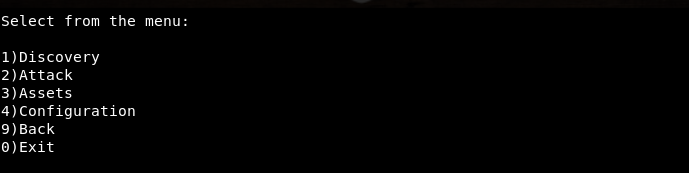
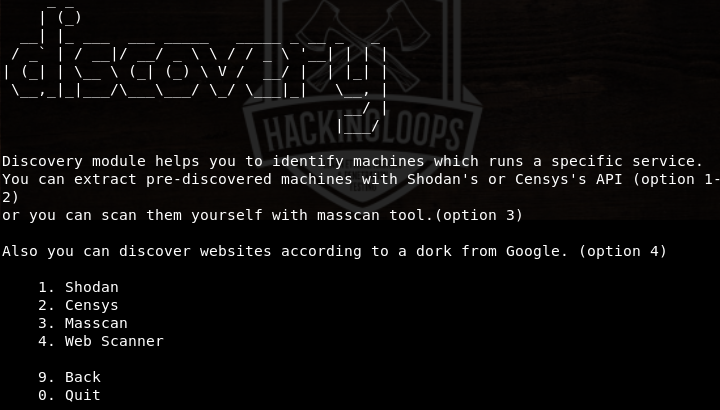
The command displays the tool’s menu shown in the following screenshot.
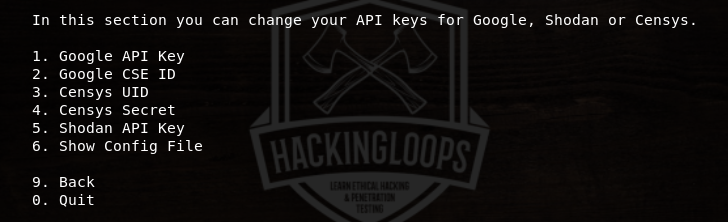
The desired penetration test can be performed by selecting its sequence number. For example, the discovery task can be performed by tying its sequence number (#1) in the command line. It is recommended to start with the Configuration option from the list (by typing #4 in the command line). Leviathan requires Google, Shodan, and Censys API keys to perform discovery tasks. The API keys can be obtained from the relevant domains. The Configuration section allows configuration of API keys and other parameters shown in the following screenshot.
After configuring the tool, select the desired scanning utility from the menu list. Each utility has specific scanning features that can be explored by entering into the desired utility section. For instance, if we the Discovery section from the list, we get the following discovery options that can be explored with the tool.
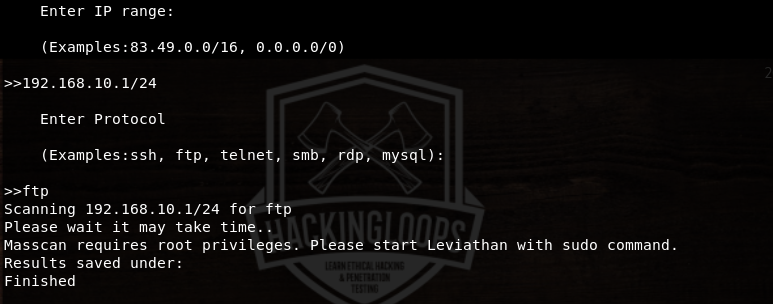
Each option can be selected by typing its sequence number. For example, we can select the Masscan option by typing its sequence number i-e #3. The Masscan option scans the network and finds out specific protocols (services) running on the available machines. The tool asks for IP range and the desired service (protocol) in the following format.
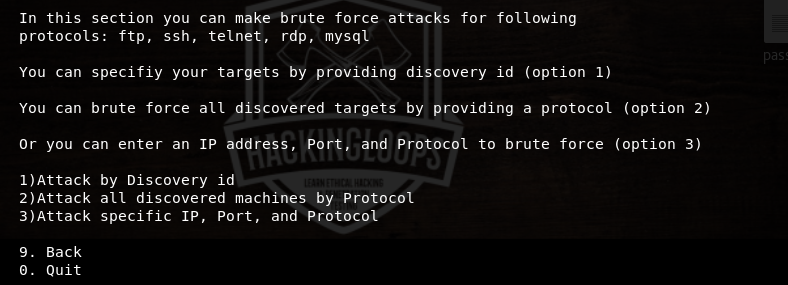
Similarly, the Attack section has the attack options shown in the following screenshot. As mentioned above, the Bruteforce option launches bruteforce attack on the network to discover the specific protocols that can be compromised by the adversary. Web (SQL Injection ) is a dork option to find out vulnerable links that can be exploited through SQL injections. The custom exploits can be used to attack the desired network machines. The remote commands can also be executed on the compromised machines using the remote command execution option from the Attack section.
If we select the Bruteforce attack option from the list, we get the following attack vectors.
1) Attack by discovery Id (The discovery id is the id number given to the discovered machines in the network.)
2) Attack all machines in the network
3) Attack specific IP, port, and service
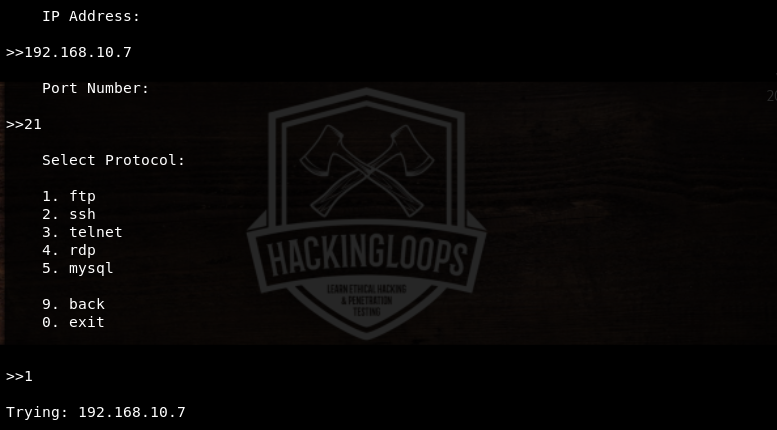
We can define the parameters in the following format for the third option in the list, i-e attacking a specific IP address, port, and service.
Conclusion
Leviathan is a handy network tool that can be used for discovering network machines that can be compromised remotely through bruteforce attacks and running custom exploits. The tool searches for the most common network protocols that are susceptible to various cyber-attacks.