Uniscan is a free penetration testing tool that can be used to test web application vulnerabilities including SQL injections, Cross Site Scripting (XSS), PHP injection, Remote File Inclusion (RFI), Local File Inclusion (LFI), remote command execution, web shell vulnerabilities, and backup files on the target web application. The tool uses built-in plugins and modules to perform the scanning. Moreover, Uniscan can be used for information gathering tasks, such as web fingerprinting, server fingerprinting, and search engine Dorking including Google and Bing Dorking. Dorking is an advanced searching technique used to find out information that does not appear during the normal search results.
Uniscan Installation
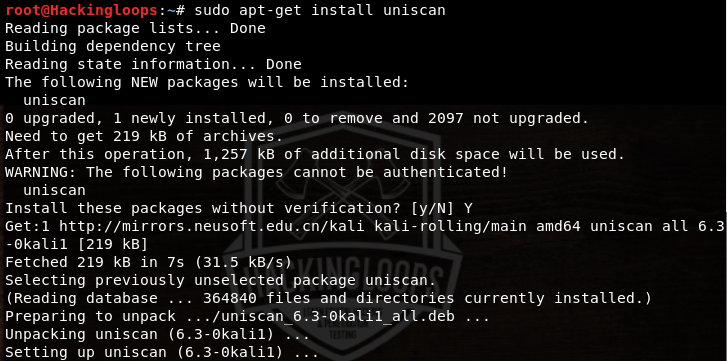
Uniscan is a Perl tool that can be installed on the Linux systems using the following command.
sudo apt-get install uniscan
The above command automatically installs the modules required by the tool. The other way to get Uniscan is to download the source code from Github using the following command.
git clone https://github.com/poerschke/Uniscan
This method requires the manual installation of modules required by the tool. Navigate to the Uniscan directory and change permission for the modules file (install-modules.sh) to make it executable. Finally run the file to install the Uniscan modules.
cd Uniscan chmod +x install-modules.sh ./install-modules.sh
How Uniscan Works
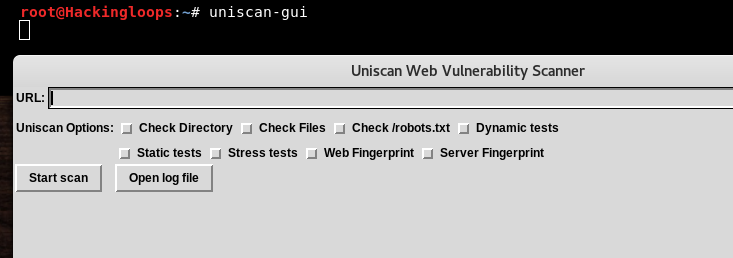
Uniscan has command line as well as GU interface. The GUI version can be loaded using the following command.
uniscan-gui
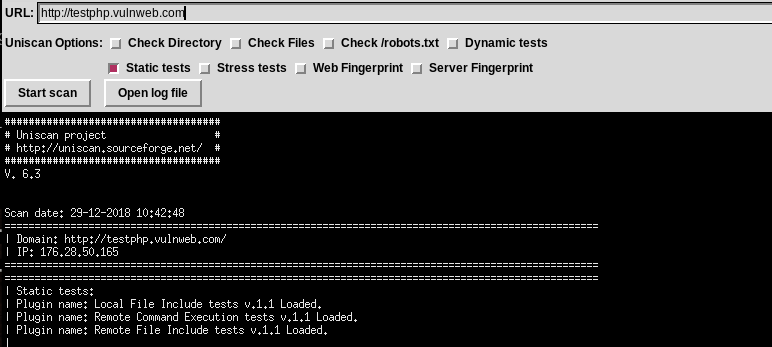
The following screenshot shows the GUI version of the tool.
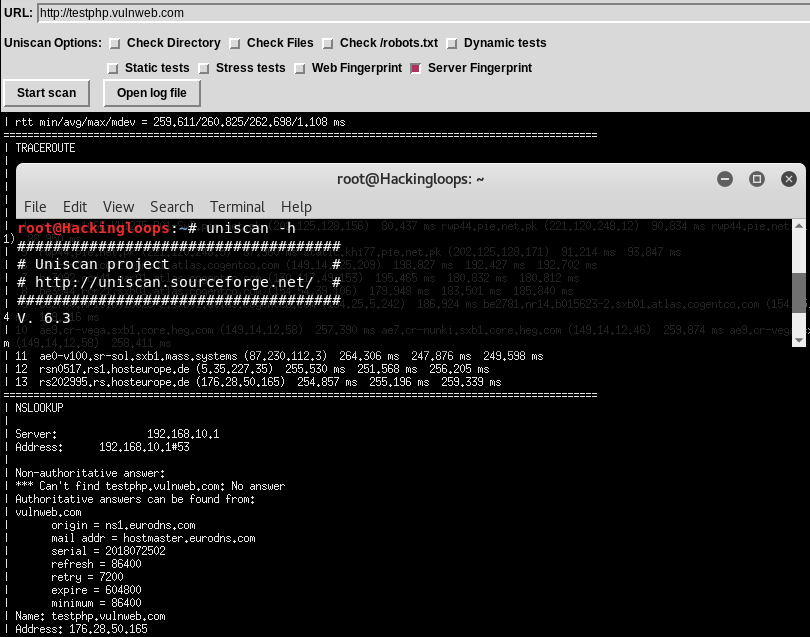
The GU interface has a target address field and a set of scanning options including directory check, file check, robots.txt file check, web fingerprinting, server fingerprinting, dynamic test option, static test option, and stress test. Moreover, there is a scan log tab that logs the scanning activities. Enter the desired web application path in the address field and select the desired scanning option from the available list to perform information gathering or vulnerabilities assessments. For instance, select the server fingerprinting task to get all the available server information for the the target web application (http://testphp.vulnweb.com). Uniscan also logs the trace route results while performing the server fingerprinting. The results are shown in the following format.
The dynamic and static scanning options are used to test the security of the target web applications. The static test covers LFI, RFI, and remote command execution vulnerabilities analysis.
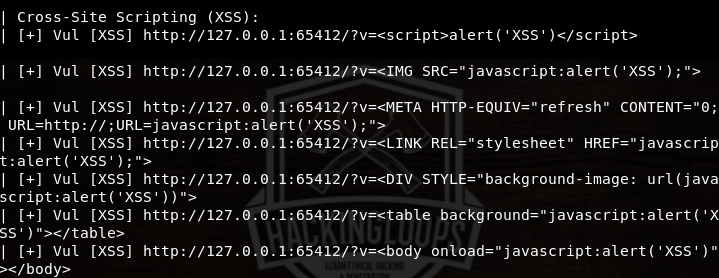
Similarly, the dynamic test covers all the remaining vulnerabilities assessments, such as SQL injections, XSS, PHP injection, and backup files check. The tool loads all the available plugins to test the target web application.
The same tasks can be performed using the command line interface of the tool. Following is the default command used to scan the target web application.
uniscan –u <target web application>
We can customize the scanning process by defining the parameters in the command
uniscan –u <target web application> <-optional parameters>
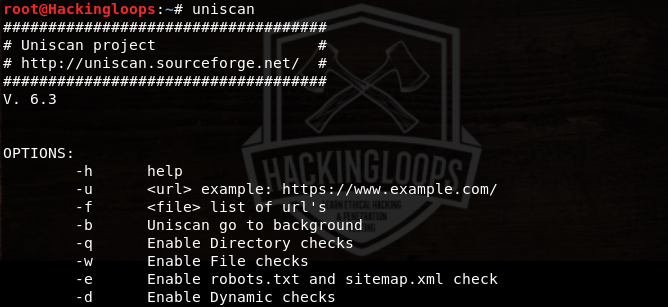
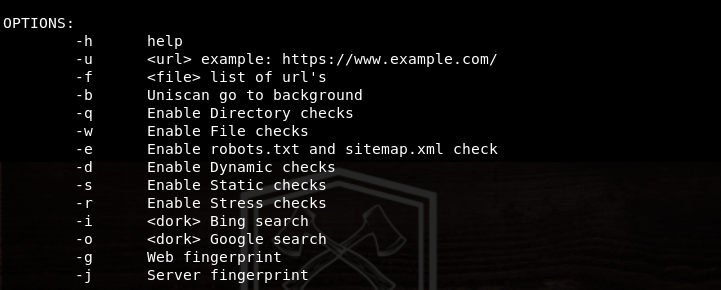
Parameters are the options that can be used to customize the scanning process. The following help command shows all the available parameters that can be used in the command to refine the scanning. Uniscan ignores all the other parameters and scans the target web application for the defined parameters only.
uniscan –h
For example, we can enable the directory check, file check, static, and dynamic tests in the following way to refine the scanning process.
unican –u http:127.0.0.1:65412 –qwds
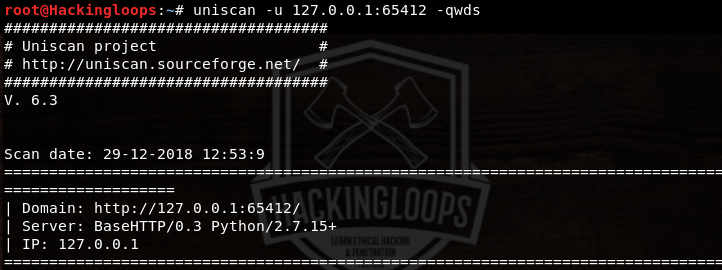
The above command explores the directories and files of the target web application for potential vulnerabilities. Any vulnerability found during the scanning process is displayed on the screen along with the vulnerability path.
Conclusion
Unican is a lightweight web application scanner that can perform deep scanning to find out potential vulnerabilities in the target web applications. The GUI version of the tool automates the scanning while the CLI version allows the customization of the scanning process.