Sitadel is a python tool used for fingerprinting and exploiting web application vulnerabilities. The tasks are performed by fingerprinting and attack modules that come as pre-installed packages in the tool. The fingerprinting features include server, content management system (cms), frontend framework, operating system, languages, and content delivery network (cdn) information gathering tasks. The attacks performed by Sitadel can be divided into bruteforce and injection attack categories. Sitadel bruteforces target web application to find backdoors, directories, common files, log files, and admin interfaces. The injection category covers SQL injection, XSS injection, HTML injection, cross site scripting, Xpath injection, Remote File Inclusion (RFI), LDAP, and PHP injection. Cross site tracing, shellshock, strut-attacks, Crime (SPDY), and anonymous cipher vulnerabilities can also be found with the help of Sitadel tool.
Sitadel Installation
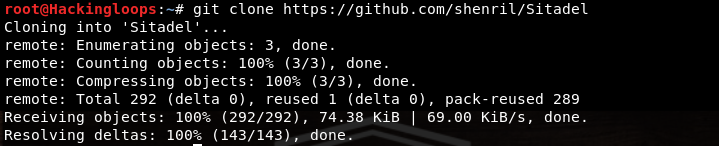
Sitadel is a python based tool that requires python version 3.4 or above to operate. The tool can be cloned from github using the following path.
git clone https://github.com/shenril/Sitadel.git
After cloning the tool, follow the Sitadel directory to run the setup file to complete the installation process.
cd Sitadel python3 setup.py install
The above command automatically installs all the dependencies required to run the tool.
Sitadel Working
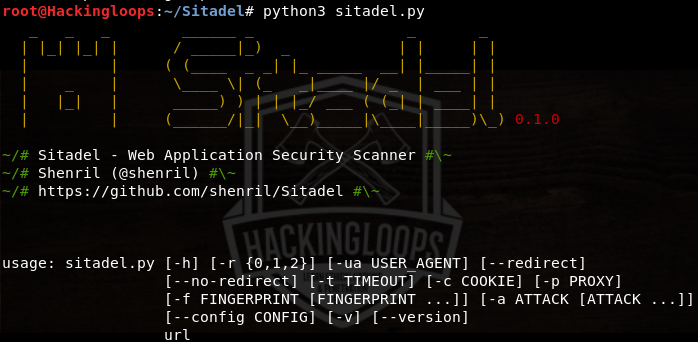
After installing Sitadel, the tool can be launched from the terminal with the help of the following command.
python3 sitadel.py
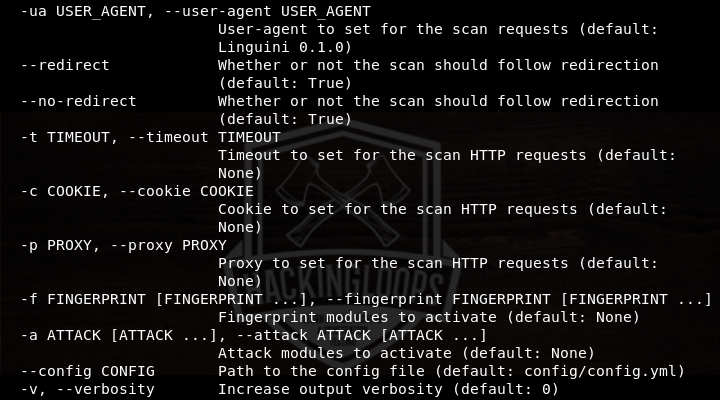
The help command shows all the mandatory and optional parameters that can be used while scanning the target application.
python3 sitadel.py –h
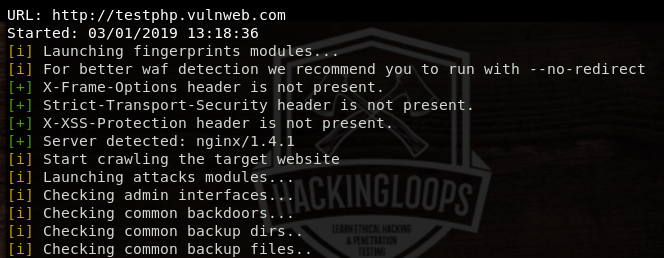
As mentioned above, Sitadel can be used for fingerprinting and attacking the target web application. The following command runs all the modules to perform fingerprinting and attack the target application.
Python3 sitadel.py <target web application>
The tool first performs fingerprinting tasks and then launches the web attacks to find out the potential vulnerabilities in the target web application.
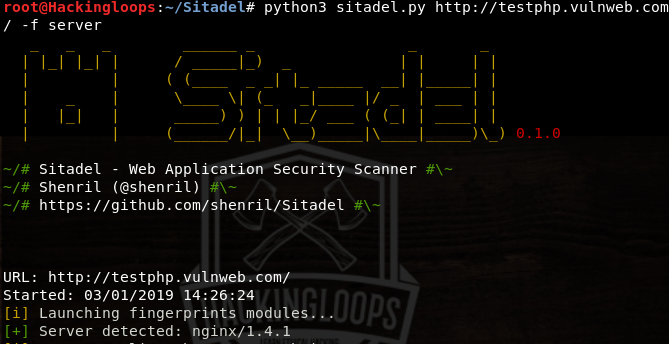
We can use Sitadel to perform specific tasks using the optional parameters. For instance, we can launch the fingerprinting modules using the following command.
python3 sitadel.py <target web application> -f <fingerprinting argument>
In the above command, -f parameter is used to launch specific fingerprinting tasks, such as header and server fingerprinting.
python3 sitadel.py http://testphp.vulnweb.com –f server
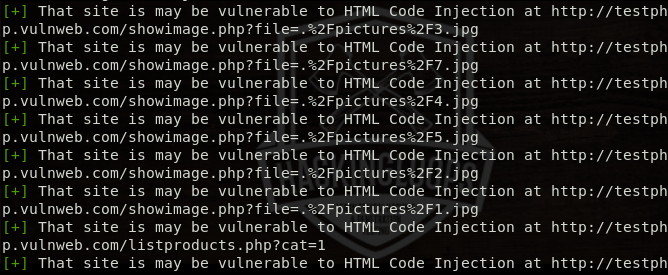
Similarly, we can launch specific Sitadel attacks by introducing the attack parameter –a in the following format.
python3 sitadel.py <target web application> -a <attack argument>
For example, we can launch the injection attacks on a target web application attack parameter and argument (injection) in the following format.
python3 sitadel.py http://testphp.vulnweb.com –a injection
The tool runs all the attack modules to find out possible injection points. If the target web application is vulnerable to any of the injection attacks, the details are shared in terminal in the following format.
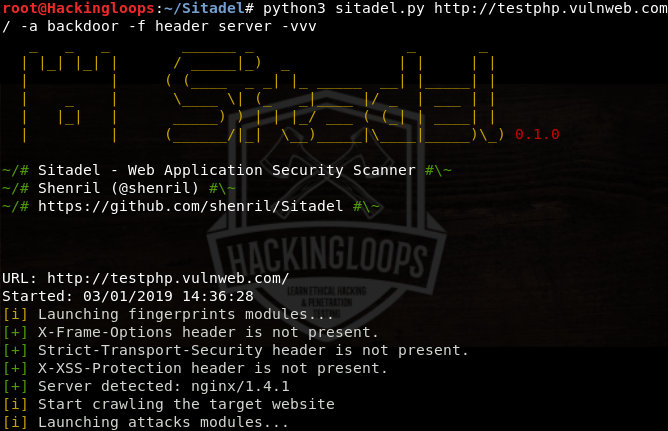
We can also combine the fingerprinting and attack parameters in the following format.
python3 sitadel.py <target web application> -f <fingerprinting argument> -a <attack argument>
For instance, we can combine backdoor (attack argument) with server and header fingerprinting arguments using the following command.
python3 sitadel.py http://testphp.vulnweb.com –a backdoor –f header server –vvv
The –vvv flags represent the verbosity mode.
Conclusion
Sitadel tool can automatically perform fingerprinting and vulnerabilities assessment tasks. The tool supports proxy settings to keep the scanning process anonymous. The tool can detect major database vulnerabilities, helping red teamers in identifying the potential vulnerabilities of the target web applications.