How to be Anonymous Online : BlackHat Method The Anonymity over the internet has become a challenge after NSA being in the news lately for spying on the citizens . The privacy over the internet has been compromised . Everyone on Internet has a unique IP Address and if someone wants to track you down or research you on the internet , then this IP address reveals a lot of valuable information about you . Though there are many programs and software available on the internet that claim to provide you 100% anonymity over the internet , but being a professional #Pentester for 3 years now , I believe every software / … [Read More...]
Featured Articles
Editorial Picks
Latest Blog Updates
 Loading...
Loading...Skype Resolver : Get Skype IP’s behind VPN Tutorial
Skype Resolver : Get Skype IP's behind VPN Skype is being used lot in the corporate environments as well as for personal use . Many think behind the VPN the IP and identity can be hidden . Well I came across this awesome tool that resolves your IP using your Skype name . The tool is web based and accessible for free . To use the Skype Resolver all you need is the Skype name of the Target . The Ip behind the VPN is resolved in minutes . This is very useful in certain penetration testing scenarios where the target might be sitting behind a VPN , and we desperately need the IP address . Using Skype Resolver , … [Read More...]
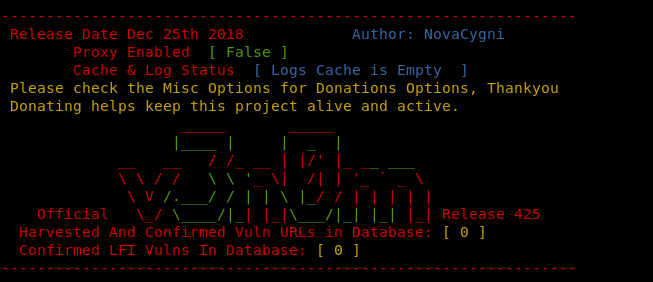
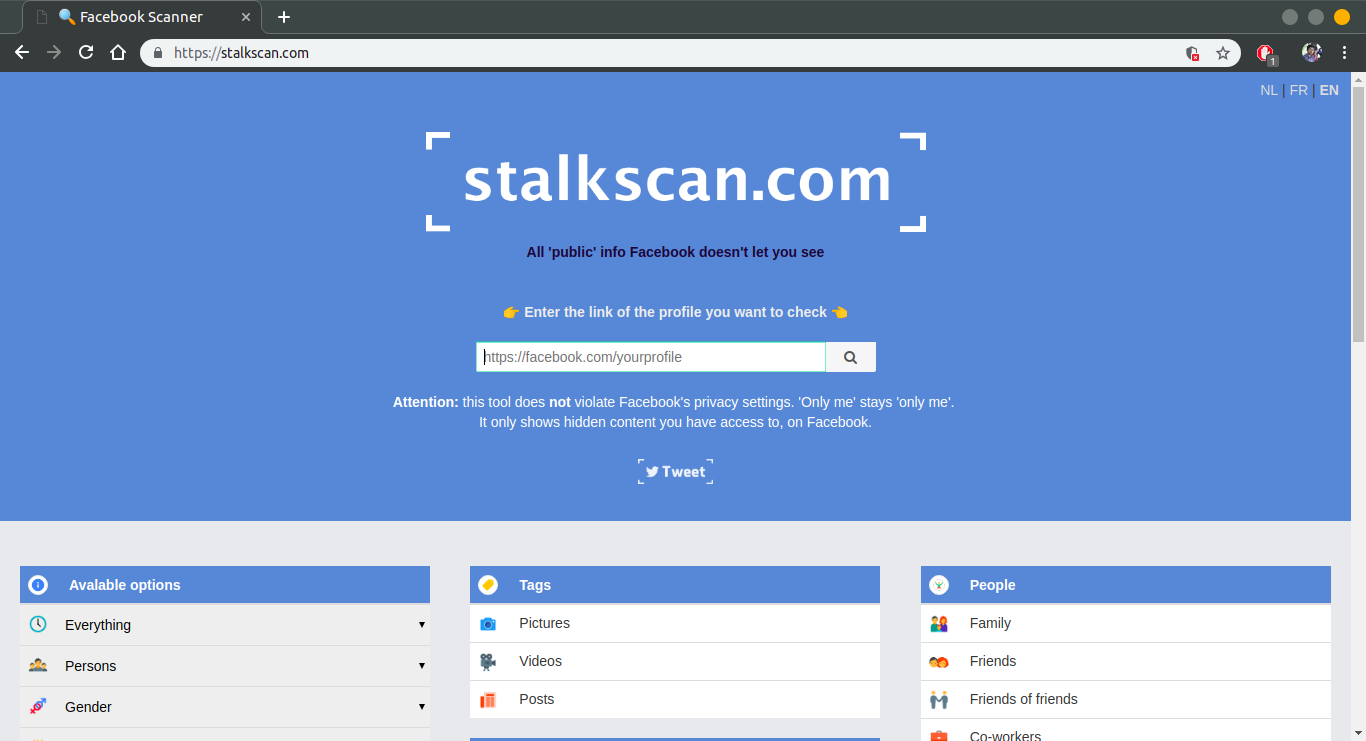
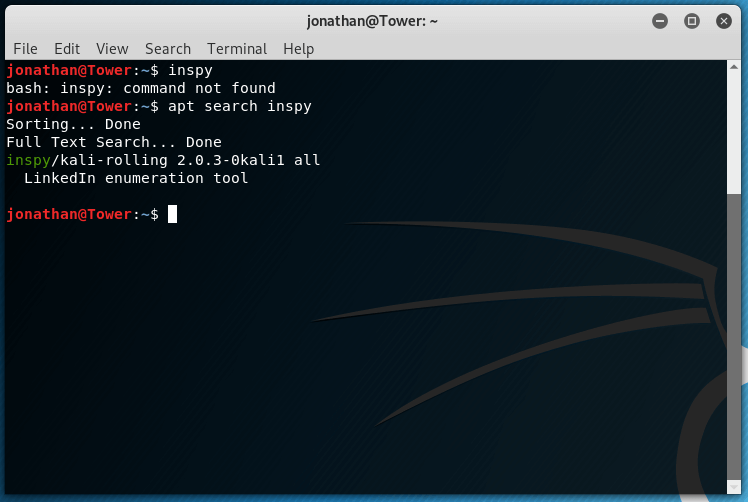
Doxing Explained : Tutorial
Doxing Explained : Tutorial Information gathering is one of the Initial steps of any penetration testing project . Information gathering deals with gathering all the information you can gather about your target . This information might be gathered by doing online searches , phone calls , emails or other social engineering . Doxing is a more comprehensive term that explains guidlines on how this information can be gathered about your target . What is Doxing? Doxing is about to get an information about someone ! Simply it deals with the profiling of your target . Whatever information you get by researching … [Read More...]
Hacking Wifi via Android Phones Easy : Secure your Networks !
Hacking Wifi via Android Phones Easy : Secure your Networks ! Secure your Networks ! War Driving is when a hacker travels to any vicinity to hack a wifi network . earlier this was limited due to the baggage of carrying the laptops .... Now with Android Smartphones becoming more computational and powerful , War Driving is easier than ever . Now all you need is an Android phone to just hack the Wifi networks anywhere you go . War Driving At Rise , the need of securing our Wifi networks is even more . Once an attacker is on your network , all sorts of internal attacks are possible , such as MITM , ARP Poisoning , … [Read More...]
Word / Excel Exploits using Metasploit During Penetration Testing
Word / Excel Exploits using Metasploit During Penetration Testing Metasploit is the favorite exploitation framework among the penetration testers . Metasploit can be used in a variety of penetration testing scenarios . One of the easiest way of spreading the exploit code through an exe file . But the major drawback in this technique is that the Antiviruses might catch the EXE as malicious as the AV engines more cautious for the PE files . So are the Targets now . The Good News : Metasploit comes with Exploits for the Word and Excel Too . This means that you can create malicious word / excel documents that can … [Read More...]