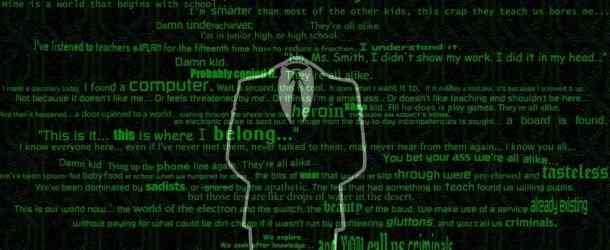
So you want to become a Hacker! I will make you an expert hacker and I will do it for free. I can give you a 100% assurance that if you are willing to become a hacker, I can make you the best one. I will teach you everything I know. No one can be perfect, but experts always exist. Most people have aspirations to become a hacker but don't know where to start, or don't know the difference between what is good and what is bad. The media typically portrays hacking as negative, but it can be used for good, and I will you teach how. Note: YOU are the catalyst, I am just your guide. Disclaimer: It's up to every … [Read More...]




 Loading...
Loading...