Yesterday I have explained You all that How to collect information about the Websites and organisations....Today i will continue With Footprinting and take you to some more deep level... And then tell you how to make Blueprints from them.. So read on....UNEARTHING BASIC INFORMATIONFirst of all We will focus on Unearthing the Basic Information about the site... i.e the IP and server informations..I will Show you with the help on snapshots :First go to START --> RUN --->type cmd--->then type tracert www.websitename.comHere we will use two basic commands in command Prompt(cmd): tracert … [Read More...]
Featured Articles
Editorial Picks
Latest Blog Updates
 Loading...
Loading...
Hacking Class 2 – Footprinting and How It can be HelpFul to Hack systems
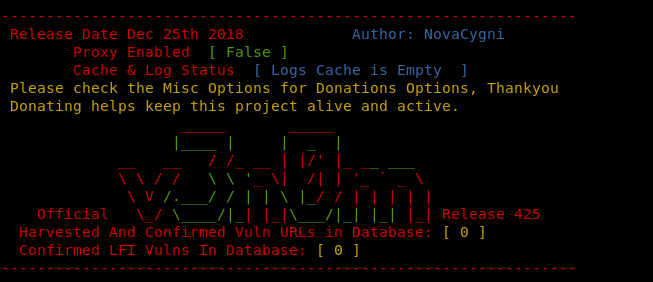
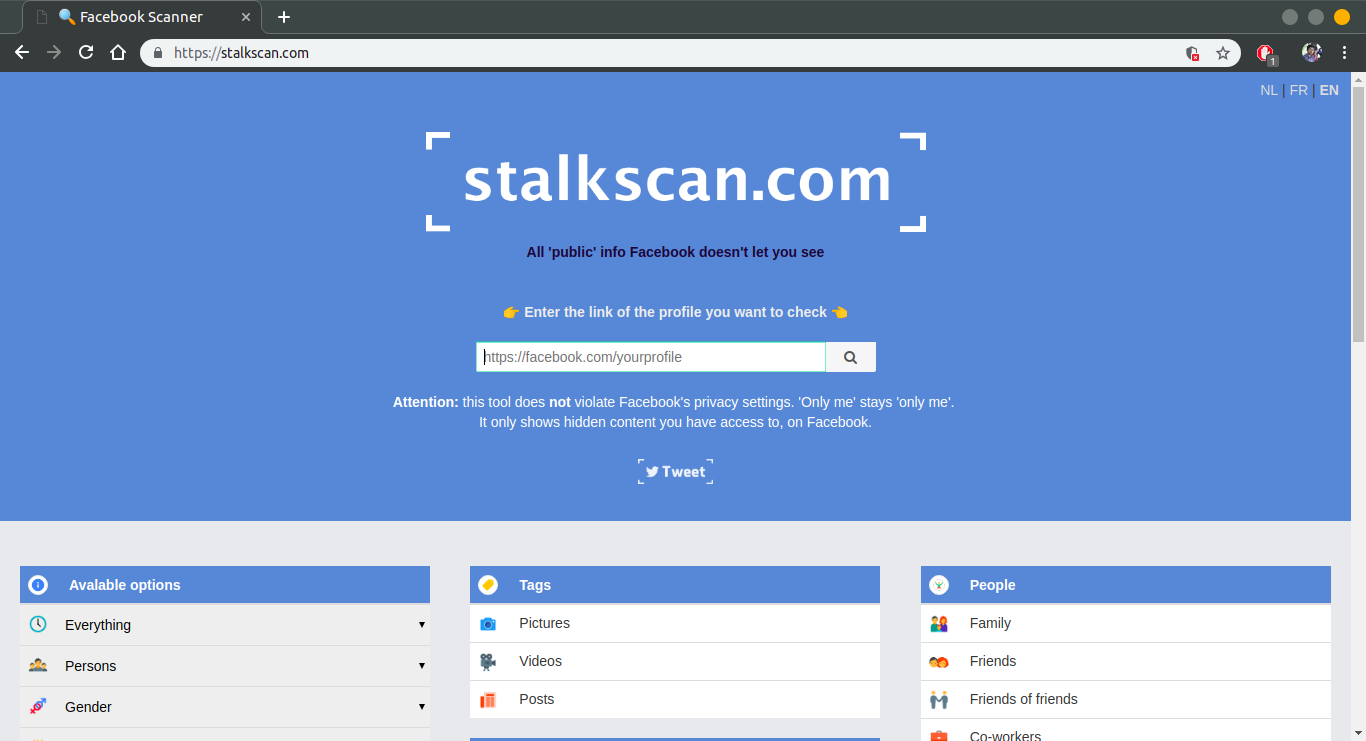
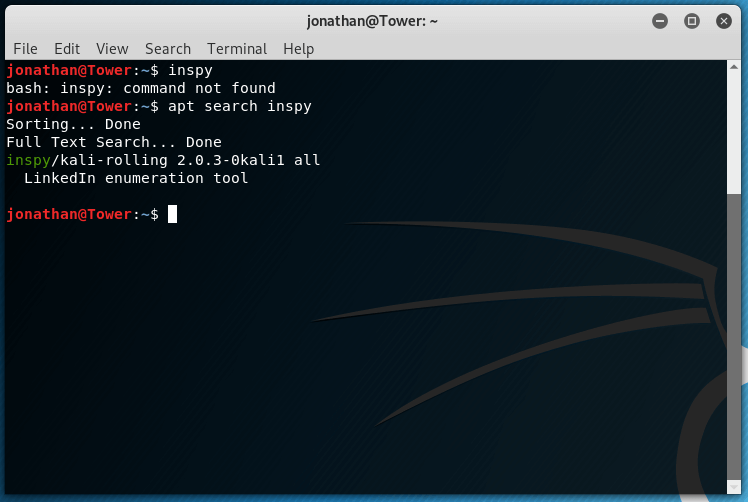
Previously We have Introduces hacking and hackers. Now In this class we will see what hackers do in pre-phases of hacking .i.e Footprinting. What Is FOOTPRINTING ?? Basically footprint is the blueprints of site/organisation/system that a hacker want to Hack i.e basic internal structure.Footprinting is the blueprint of the security profile of an organization, undertaken in a methodological manner. Footprinting is one of the three pre-attack phases. The others are scanning and enumeration. Important Thing to be Noted : An attacker will spend 90% of the time in profiling an organization … [Read More...]
Hacking Class 1 – Introduction to Hacking and Hackers
This is the Very First Tutorial Of Hacking . In this tutorial we will discuss what is hacking.. ethical hacking security...who are hackers...why we do hacking...and Introduction to some basic terms...First of all I will try Explain what the Hacking really is....What Is Hacking??Everyone Here thinks that hacking is just stealing of data and information illegally but this perception is absolutely wrong. The below is definition from Wikipedia.... Itz clearly showing hacking as a negative thing..."Hacking is unauthorized use of computer and network resources. (The term "hacker" originally meant a very … [Read More...]
Trojan And Backdoors – A simple Introduction and Functioning
A Trojan horse is an unauthorized program contained within a legitimate program. This unauthorized program performs functions unknown (and probably unwanted) by the user.It is a legitimate program that has been altered by the placement of unauthorized code within it; this code performs functions unknown (and probably unwanted) by the user.Any program that appears to perform a desirable and necessary function but that (because of unauthorized code within it that is unknown to the user) performs functions unknown (and definitely unwanted) by the user.Working of … [Read More...]
How To Protect Your Orkut Account From Being Hacked ? Almost All Hacking Techniques Covered
Hello Guys In this Tutorial First I will tell the Hacking Method and then I will Tell the Solution that How To Protect Yourself from Being hacked... So Read On..Its a Pity Interesting topic to discuss...How To Hack Orkut ??? In this Tutorial I will Try to Explain All the Methods that Any Hacker Can Use To Hack your Orkut account along with Their Prevention Measures.. So Read It Carefully .. Its really a Worth Article and Also very Informative .So Enjoy Reading....Google uses a 4 Level Orkut login which makes it difficult to hack Orkut using brute force attack.First Level - Security-SSL or … [Read More...]