Pentesting is a huge field, and security audits often require massive investments of time and effort. Performing a complete security audit would be impossible to do competently if it weren’t for the many tools that offensive security teams rely on to do their work. Popular windows penetration testing tools automate entire swaths of work, such as password cracking, networking mapping, phishing simulations, and much more. Imagine if you had to write software to do all of those tasks, everytime you needed to begin a new security audit?
In this article, we’ll introduce a cast of powerful tools to help you on your hacking journey. For each tool, we’ll do three things.
- Introduce you to the tool.
- Explain what it does & how it works.
- Give a brief example of its usage.
Well, we’ve got a lot of tools to cover. So let’s get started with our hacking tools, starting with the most popular and powerful of them all.
Metasploit – king of popular pentesting tools
More than just a tool, Metasploit is an entire hacking framework. Yes, Metasploit is a Windows Penetration Testing Tool in addition to linux. Its It gives you built-in exploits and scripts for automatically pwning boxes. But that’s just the beginning. Metasploit can help you hide your payloads to bypass antivirus, search for known exploits of a given software, and much more.
To download Metasploit Framework, paste these commands into your terminal.
$ curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb > msfinstall && \
chmod 755 msfinstall && \
./msfinstall
$ /opt/metasploit-framework/bin/msfconsoleAt this point, Metasploit should begin walking you through a text based setup. Once you’re ready, you should see a screen that looks like this:
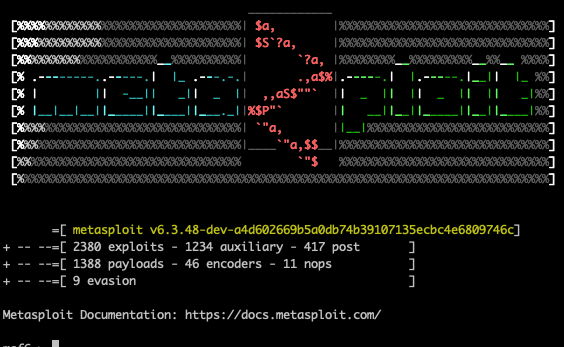
Now you’re ready to begin hacking with Metasploit! As a simple example, let’s imagine you’re playing a CTF and need to create a reverse shell. Metasploit makes this as easy as running a few commands.
$ use exploit/windows/smb/ms08_067_netapi
$ set payload windows/meterpreter/reverse_tcpThe precise syntax may vary based on your system. But you can continue learning about Metasploit via our guide: The most important Metasploit commands you’ll need.
Burp Suite
Often, when testing an app, you’ll spend a great deal of time reverse engineering the API. By playing with different values sent in web requests, you can see what values cause the app to behave in surprising ways. Burp Suite helps with this by letting you intercept requests and modify them in transit.
Here’s an example of what it looks like when you intercept a form submission using Burp.
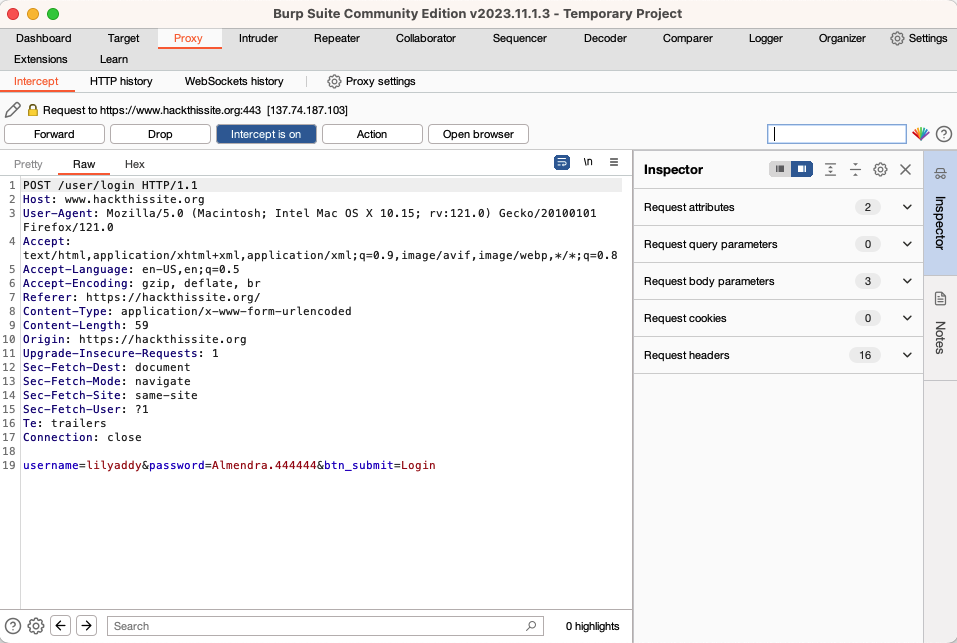
Maybe this looks like Greek to you. If so, you’re actually in luck. PortSwigger, the company behind Burp, writes some of the best tech docs on the internet. Get started here: https://portswigger.net/burp.
By the way, Burp can also help you pentest mobile apps. Check out our guide on that particular topic, Intercepting HTTP and HTTPS / SSL Mоbile traffic using Burp Suite.
Gophish
According to a report from Techopedia, “phishing attacks account for 36% of all US data breaches.” In other words, phishing belongs in any comprehensive security audit. As a pentester, you need to have the phishing skills to help companies figure out how they’d perform under a realistic phishing attack.
Gophish is a fully featured phishing framework that lets you easily set up fake login pages, send phishing emails throughout the company, and track who clicks on phishing content and tries to log in. And all of those cool features work inside of an easy to use web based interface, that looks like this.
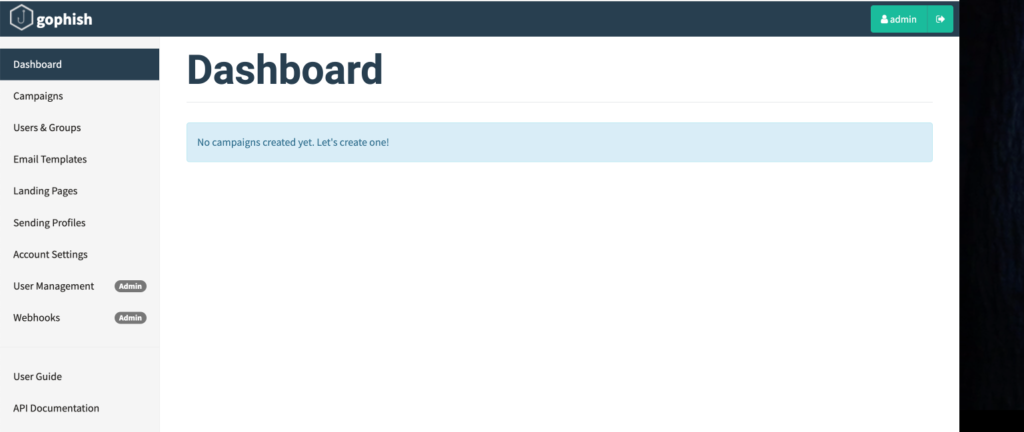
Gophish empowers you to launch a phishing campaign without spending hours coding realistic phishing pages, or dealing with DMARC all day long.
Nmap
Nmap is a simple tool. Given a host, or range of IP addresses, you scan them all to see what’s running. You can try to detect their operating system, software versions, and even automatically run exploits on vulnerable versions.
It’s as easy running the nmap command, followed by the host you wish to scan.
➜ ~ nmap 94chan.org
Starting Nmap 7.94 ( https://nmap.org ) at 2024-01-15 20:50 CST
Other addresses for 94chan.org (not scanned): 2606:4700:3033::ac43:9ff4 2606:4700:3032::6815:292c 104.21.41.44
Not shown: 996 filtered tcp ports (no-response)
PORT STATE SERVICE
80/tcp open http
443/tcp open https
8080/tcp open http-proxy
8443/tcp open https-alt
Nmap done: 1 IP address (1 host up) scanned in 67.09 secondsIf you want to find out what a remote machine is running so you can hack into it, nmap should be your go-to tool. To learn more about tools like nmap, check out our guide to networking for hackers: https://www.hackingloops.com/networking-basics-for-hackers.
Oh, a fun fact: nmap famously appears along with a few other networking tools in this famous scene from The Matrix.
A classic from the era of cheesy hacker movies that took themselves way too seriously! Still, there’s a lesson to be learned from this moment in cinema history. As techies, we constantly hear about how tech changes so quickly, and you always need to learn the newest tools. But this scene shows us that many skills and tools have been the same for quite some time.
Hashcat
Hashcat is a powerful password-cracking tool. It utilizes various attack methods, such as brute-force and dictionary attacks, to crack hashed passwords. It’s simple to use via the command line. We can attack an unsalted MD5 password with just one command, like so.
hashcat -m 0 -a 0 -o cracked.txt hashed_password.txt password_list.txtFor a more advanced example of Hashcat, check out this attack against salted passwords: https://robinverton.de/blog/cracking-salted-md5-with-hashcat.
It’s quite impressive what this tool can do, compared to simpler password-cracking tools like John The Ripper. However, keep in mind that Hashcat is not a panacea. Cracking hashes with rainbow tables is one thing, but salted passwords are often quite secure, and some are practically uncrackable.
More popular windows penetration testing tools
As we’ve seen, the market for security software is replete with powerful tools to make your job easier. In fact, the tools discussed in this article are just the tip of the iceberg. We haven’t even touched mobile application pentesting or top AI tools for ethical hacking yet either.
Of course, a real pentester doesn’t just learn tools. Rather, you should always aim to master the fundamentals of the technology your working with. Never rely on tools you don’t really understand. A tool is only as good as your understanding of it.
Nevertheless, even the highest level of theoretical mastery of underlying computer science and infosec concepts is nearly useless if you don’t spend a little bit of time learning your tools. So take some time making your life easier and make sure you know how to use the tools of modern pentesting.

