Sn1per is a web penetration testing framework used for information gathering and vulnerabilities assessments. The framework has a premium and a community version. The premium version has the exploitation features as well. The community version of Sn1per framework can perform the following information gathering and vulnerabilities scanning tasks.
- Basic reconnaissance tasks like WHOIS record, DNS information, HTTP Header data etc.
- Active TCP and UDP ports enumeration.
- Sub-domain bruteforcing.
- Zone transfer vulnerability analysis.
- Sub-domain hijacking test.
- Anonymous FTP access checkup.
- Anonymous LDAP access test.
- SSL/TLS ciphers, protocols, and vulnerabilities enumeration.
- SNMP community strings, users, and services enumeration.
- SMB users and shares listing, NULL sessions and exploit MS08-067 checkup.
- Target hosts screenshots.
- Open X11 servers test.
- JBoss, Java RMI and Tomcat servers’ vulnerabilities exploitation.
Sn1per can automatically outsource the features of other tools like NMAP, Metasploit, Zenmap, WPScan, Arachni, and Nikto to perform different web scanning tasks.
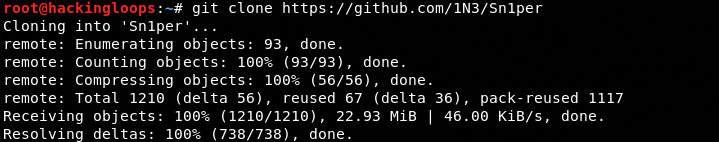
Sn1per Installation
Sn1per installation is a two-step process. First we need to clone the framework. The cloning can be done using the following command.
git clone https://github.com/1N3/Sn1per
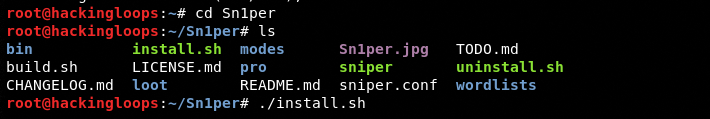
In the next step, move into the Sn1per directory and run the install.sh file using the following commands.
cd Sn1per ./install.sh
The execution of install.sh installs the framework and its dependencies. The third party scanning tools are also installed automatically during the installation of Sn1per framework. Sn1per integrates itself with these tools to use them during the scanning tasks.
How Sn1per Works
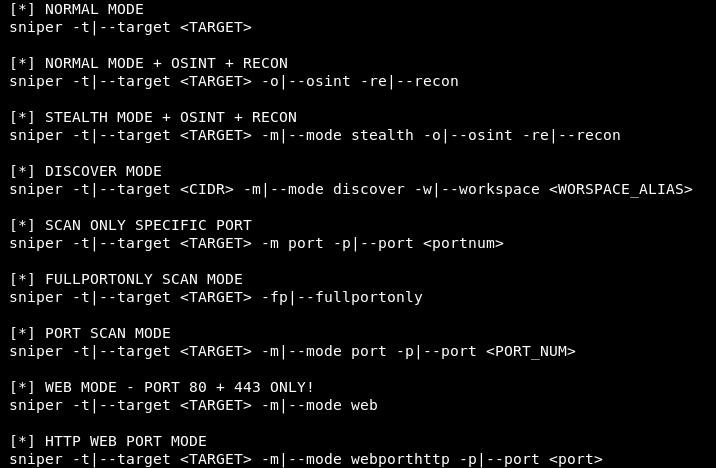
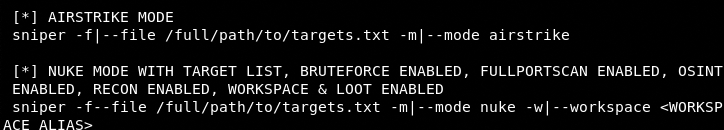
Sn1per has different scanning modes, such as normal, OSINT, reconnaissance, stealth, discovery, specific port, full port, web mode, air strike, and nuke mode. In the normal mode, Sn1per performs all the enumeration tasks listed above. The framework can be initiated in the normal mode using the following command format.
sniper –t <target url here>
All the other modes are task-specific. For instance, the specific port mode allows the scanning of the specific (selected) ports. The following screenshot shows the usage format of all the modes.
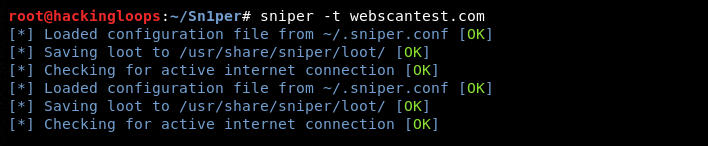
For demonstration purpose, we select the normal mode to scan a test web application (webscantest.com).
sniper –t webscantest.com
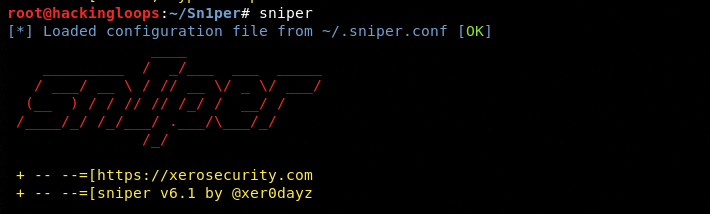
Before the scanning process begins, Sn1per loads the necessary configuration files and creates an output file to store the results.
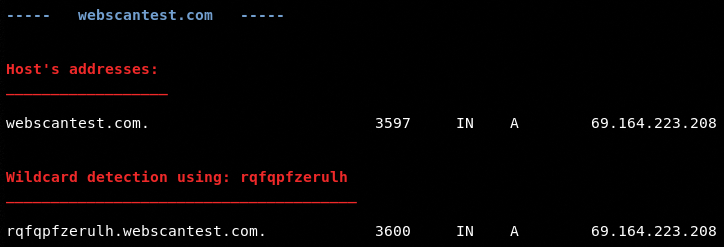
In the next step, Sn1per performs all the aforementioned scanning tasks. For example, Sn1per performs the reverse IP lookup task to fetch the IP address record of the target host.
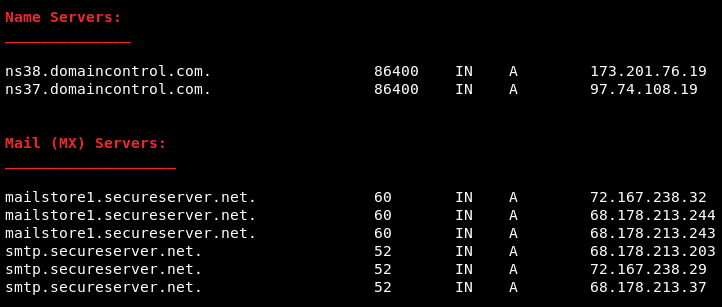
In the next step, Sn1per gathers the nameservers and Mail (MX) servers record as shown in the following screenshot.
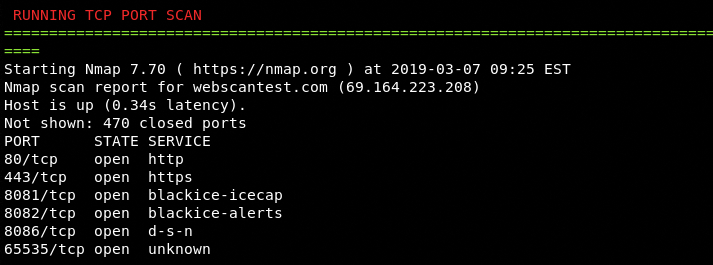
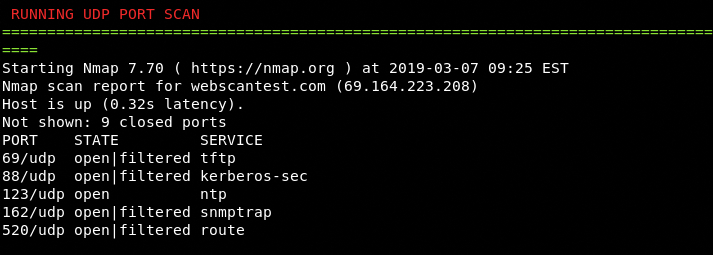
Sn1per makes use of NMAP scripts to scan the open ports and running services. The framework not only scans the TCP port but also finds the open UDP ports along with the active services.
TCP Ports
UDP Ports
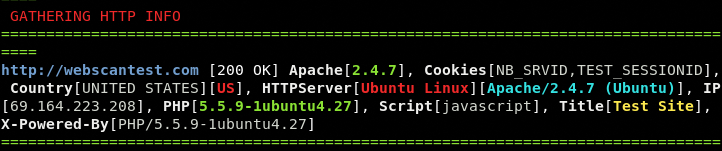
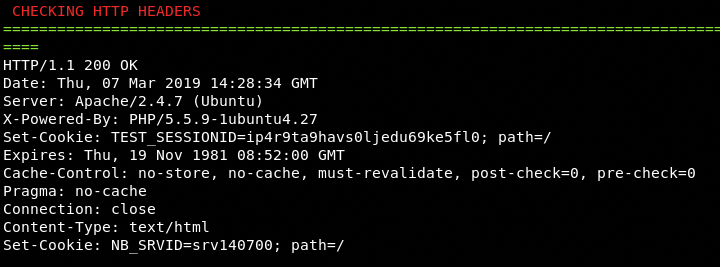
The HTTP header and server information gathered by Sn1per reveals a lot of useful information about the target host.
The vulnerabilities found by the Sn1per are displayed on the screen in a similar fashion. The premium version of the framework also offers takeover features to exploit the discovered vulnerabilities.
Conclusion
Sn1per is a handy information gathering and vulnerability analysis framework. Since Sn1per outsources the services of third party scanning tools, some scanning tasks are repeatedly performed by the framework. Although the repetition of the tasks increases the overall scanning time, the comparison of results from different tools reduces the chances of false positives.