Sparta is a network reconnaissance tool that helps penetration testers during the scanning and enumeration stage. Sparta can identify the live hosts in a network, find the services running on each host, and perform bruteforce attacks to find out default credentials for the common services. The tool also enumerates the devices/services that use the same login credentials in the network.
Sparta Installation
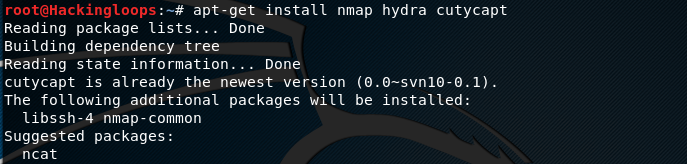
Sparta requires Nmap, Hydra, and Cutycapt tools to perform the basic functions like adding hosts to the tool, performing bruteforce attack on the services, and taking screenshots of the network hosts. In Linux OS, these tools can be installed as follows.
apt-get install nmap hydra cutycapt
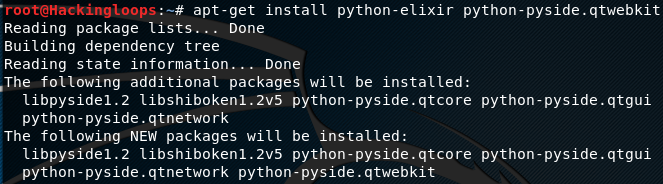
Apart from above-mentioned tools, Sparta requires some additional packages i-e python-elixir and python-pyside.qtwebkit. These packages can be installed in the following manner.
apt-get install python-elixir python-qt4 xsltproc
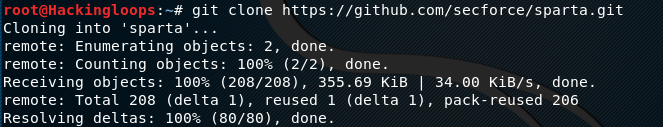
After installing the dependencies and the mentioned tools, clone Sparta from Github using the following command.
git clone https://github.com/secforce/sparta.git
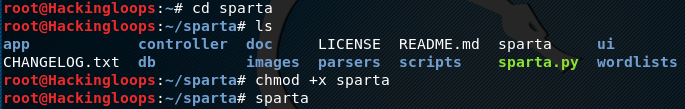
In the next step, enter into the Sparta setup directory and make the sparta file executable as shown below.
chmod +x sparta
The executable sparta file can then be used to launch the Sparta GUI application.
Sparta Interface
Sparta GUI can be launched by running the sparta file from the terminal.
sparta
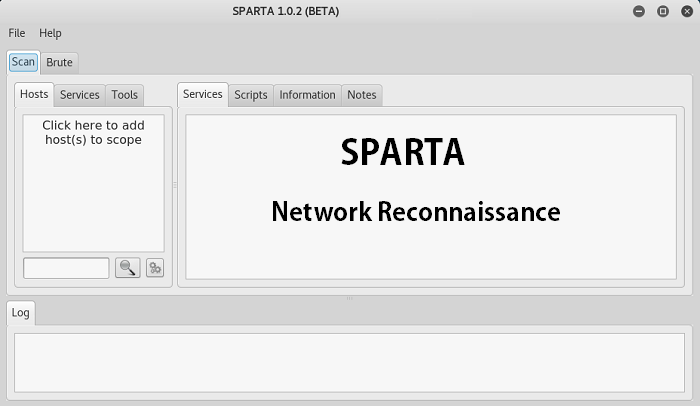
Sparta user interface can be seen in the following screenshot.
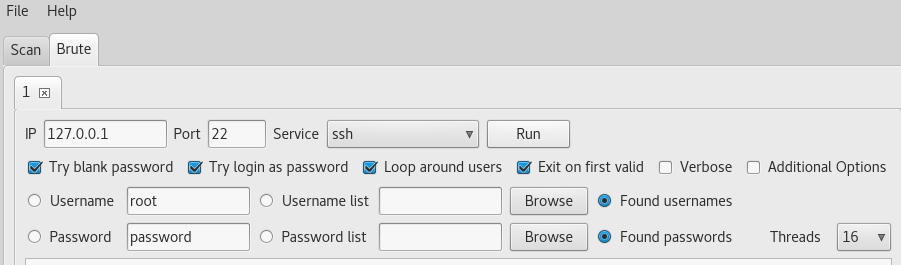
Sparta interface can be divided into three sections namely Top, Middle, and Bottom section. The top section shows two main functionalities i-e Scan and Brute. The Scan option allows scanning the network and adding hosts to the scanning process. The Brute option is used to run the bruteforce attack on the selected hosts and services. The following screenshot gives a brief overview of the options that can be configured during the brute force attack.
The Middle section shows the information gathered during the scanning process. This includes hosts information, network services, tools findings, and other useful information gathered by scanning the open ports and running services.
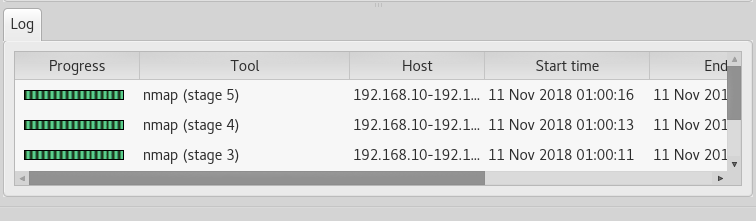
The Bottom section of Sparta tool logs all the activities carried out during the scanning process. This section also allows aborting the scanning process.
How Sparta Works
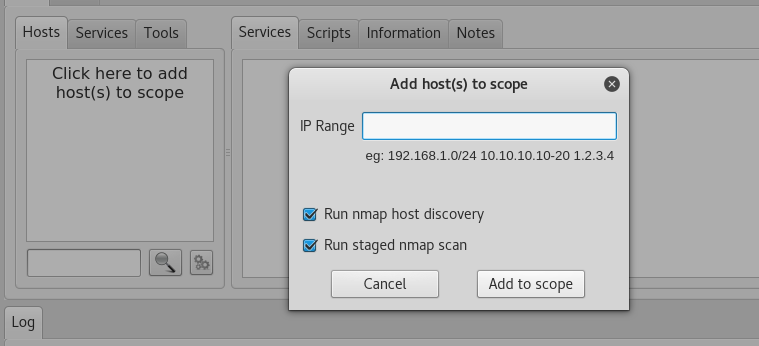
Let’s assume a network ranging between 192.168.10.1-192.168.10.255. In order to find out live hosts in this range, add the IP addresses to Sparta scanning utility in the format shown in the following screenshot.
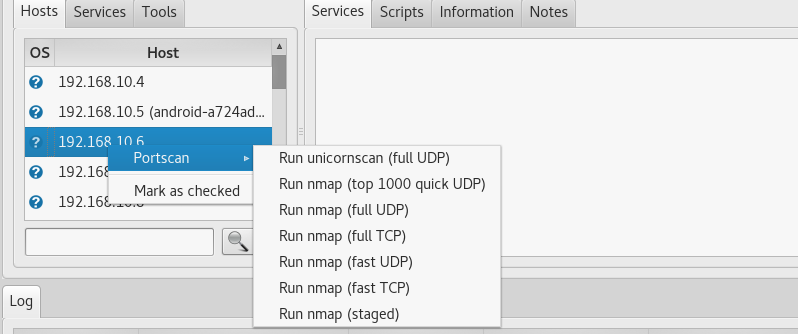
By clicking the “Add to Scope” option, Sparta loads network IPs to the Hosts section. If the nmap services are selected, the tool scans all the live hosts and the associated services in the given IP range. Otherwise, this process can be performed manually by selecting each host IP individually and running the desired scan option as shown below.
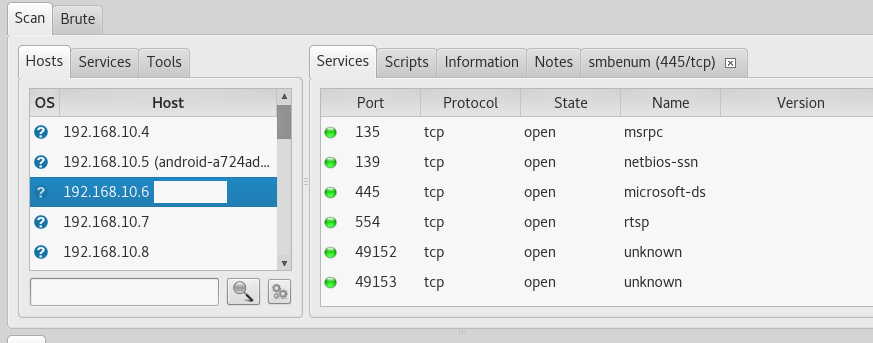
For instance, by running the fast tcp scan on 192.168.10.6, we have found the host name and the associated services. The services tab shows the services running on specific ports along with the protocols (tcp/udp). The open ports and services information is very vital in ‘’gaining access’’ phase.
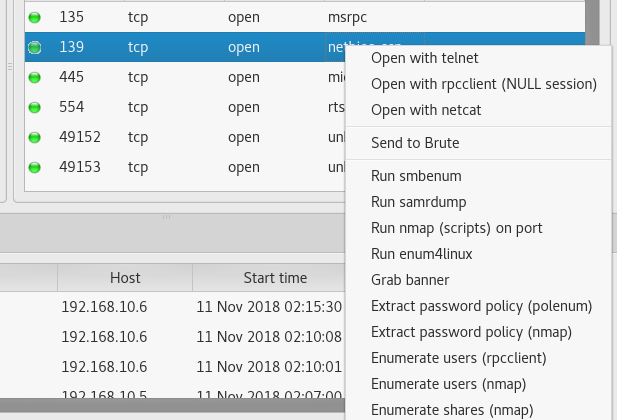
We can also perform the secondary tests on the discovered services. The secondary tests options vary according the services. The following screenshot shows the list of tests that can be performed on Netbios service discovered during the scanning process. The Netbios service allows the hosts applications to communicate with each other. The attackers look for Netbios flaws to exploit the networks.
Apart from scanning hosts and running services, Sparta can find default credentials through bruteforce attack. The tool also looks for the credentials that are used more than once in the target network.
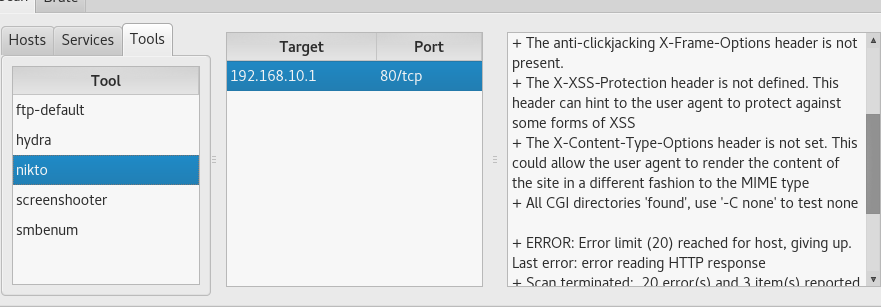
Sparta uses Nikto tool to find different header options in the target hosts as shown below. The tool also shows the associated vulnerabilities for the discovered header issues.
Conclusion
Sparta makes the network scanning and enumeration process fast. The GUI feature allows the user to get clear insight of network hosts, services, and other information like ports, IP addresses, default credentials, and banner information.