Trape is a web based penetration testing tool that can track users and launch different browser attacks. The payloads are shared with the victim through social engineering tricks. Upon clicking the vulnerable link, the information about target operating system, running browser, target location, IP address, and active user sessions on different networks is exposed. Some of the supported networks include Google, Facebook, Instagram, Linkedin, Amazon, Redit, Etsy, Youtube, and Twitter. Trape can launch different browser attacks on the victim’s machine. These include replacing active web pages with desired pages, redirecting urls, showing pop-up messages, injecting Java script codes, playing voice messages in the victim’s browser, and luring victim to download files through the browser.
Trape Installation
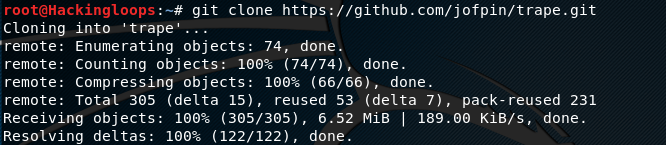
Trape can be cloned from Github using the following repository path.
git clone https://github.com/jofpin/trape.git
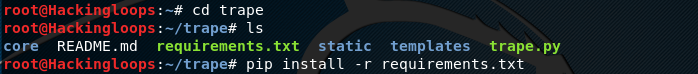
After cloning the tool, install the required packages mentioned in the requirements.txt file.
cd trape pip install –r requirements.txt
How Trape Works
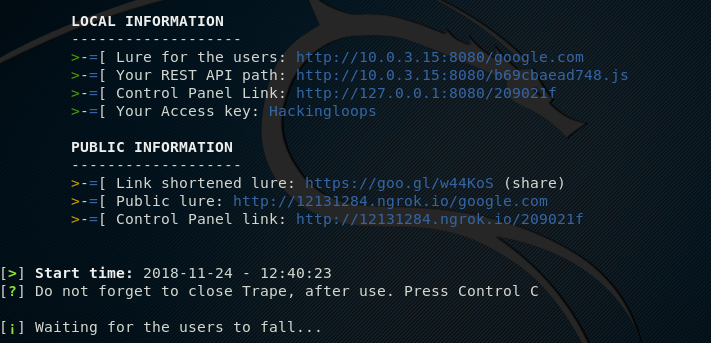
Although Trape is a web based tool, it is initiated by running the trape.py file in the terminal. The fresh installation of Trape may ask to configure ngrook and Google map API keys. These keys can be obtained by signing up on the respective sites. Following is the basic Trape command that can initiate the Trape tool and generate the required credentials.
python trape.py --url <decoy> --port <port number here> --accesskey <Optional Access Key>
The decoy is the desired url that needs to be cloned to generate the phishing link. –accesskey is optional in the command. Access key is required to access the web interface of the tool. The –accesskey allows setting custom access key in the terminal. Trape generates a random access key if –accesskey flag is ignored in the command.
Let’s assume google.com as a decoy url, 8080 as listening port, and Hackingloops as a default key to access the web interface of Trape. By defining these parameters in the terminal, the tool generates the phishing link, web control panel link, and access key as shown below.
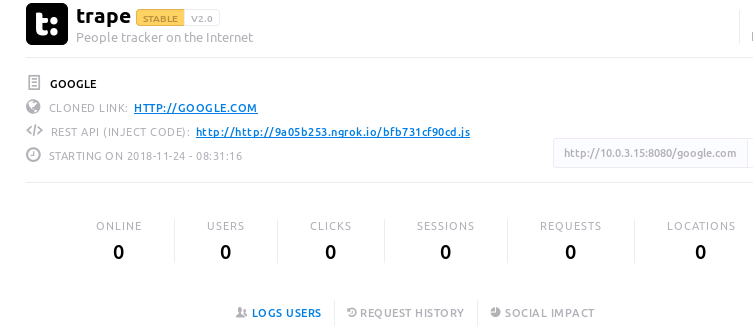
In the next step, open the Trape interface in the preferred web browser by using the control panel link and the access key. The Trape interface can be seen in the following screenshot. It contains information like total number of victims, active victims, user sessions, victim’s location, and attack vectors. The record is updated as somebody clicks on the phishing link.
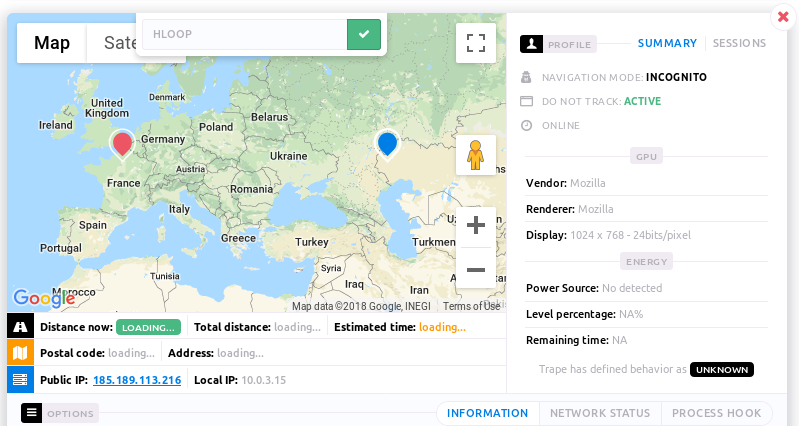
Share the link with the target through any social engineering technique. We can use url shortener service like bitly to give cover to the payload (link). Once user opens the vulnerable link, Trape captures user data, such as user IP, location, browser technology, and information about active sessions if any. If the victim is logged into any network shown in the following screenshot, the credentials can be harvested by clicking the attack button appearing under the networks.
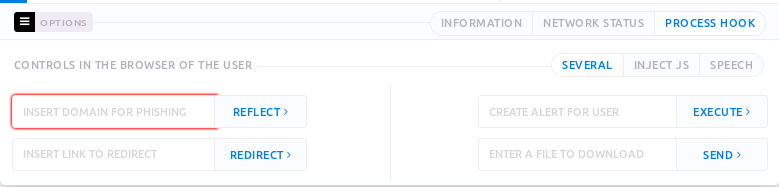
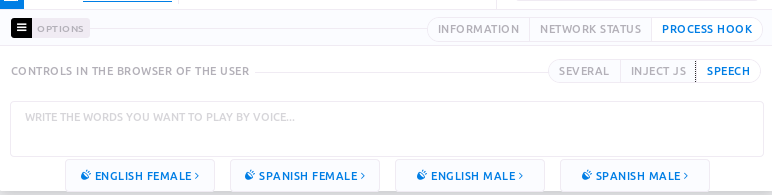
Besides tracking, Trape can launch browser attacks on the victim machine. The details about attack vectors can be seen in the Process Hook section as shown in the following screenshot.
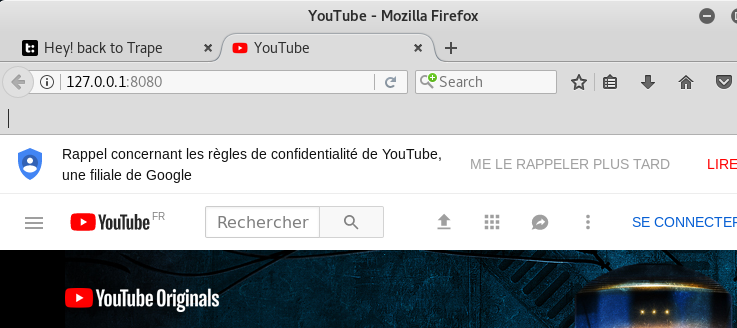
The Process Hook section is divided into three attack vectors namely Several, Inject JS, and Speech. The Inject JS option allows Java script injections in the victim’s browser. The Several tab contains attacking options like replacing the active web page on the target machine with the desired (e.g phishing) page, generating alerts in the victim’s browser, and sending downloadable files to the victim. For instance, by entering the youtube link in the Reflect field mentioned in the Several tab and clicking the Reflect button, the active web page in the victim’s browser is replaced with the declared youtube link.
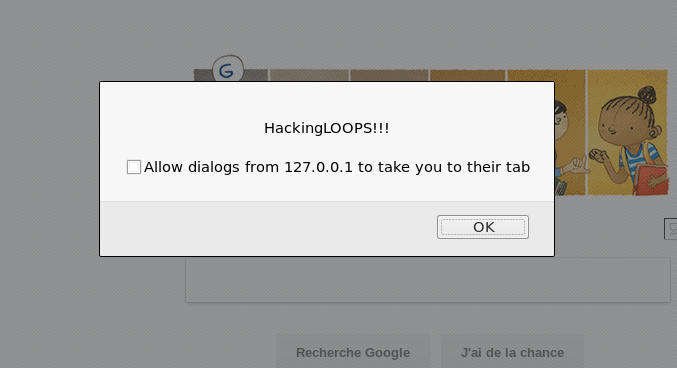
We can generate a pop up message (e.g HackingLOOPS!!!) in the victim’s browser by using the alert field. The alert message appears on the victim’s screen in the following format.
Similarly, we can play voice message in the victim’s browser by typing text in the Speech section shown below.
Conclusion
Trape is a nice tool that can track distance between the target and host machines in a graphical format. Penetration testers can use Trape to test the browser’s security against different attacks like phishing, url redirection, pop-ups, Java script code injection, and suspicious downloads.