W3af is an open source framework used for testing web applications security. The framework is capable of detecting more than 200 vulnerabilities. Some of these include SQL injection, Buffer overflow vulnerabilities, CSRF, LDAP injection, Cross Site Scripting (XSS), Xpath injection, eval () injection, OS commanding, local file inclusion, remote file inclusion, and discovery of sensitive data. W3af analyzes these vulnerabilities by using built-in plugins.
W3af Installation
All W3af versions are supported by Linux and MAC OS. However, the Windows users can only use the older versions of W3af as there is no support available for the latest W3af release. Windows users can download the framework from the following W3af official link.
http://w3af.org/download
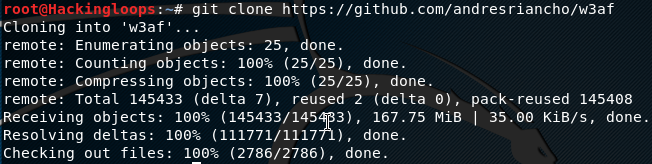
In order to install W3af on Linux system, clone W3af framework from Github using the following path.
git clone https://github.com/andresriancho/w3af
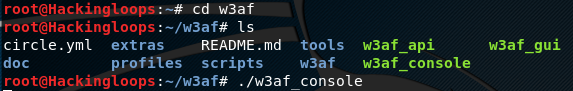
After that, move to W3af directory to install the dependencies. W3af has two types of dependencies, i-e for the console as well as for the GUI. The console dependencies can be installed as follows.
cd w3af ./w3af_console . /tmp/w3af_dependency_install.sh
In order to install the GUI dependencies, use ./w3af_gui instead of ./w3af_console.
W3af Interface
After installing W3af dependencies, W3af can be initiated by running the following command.
w3af_gui
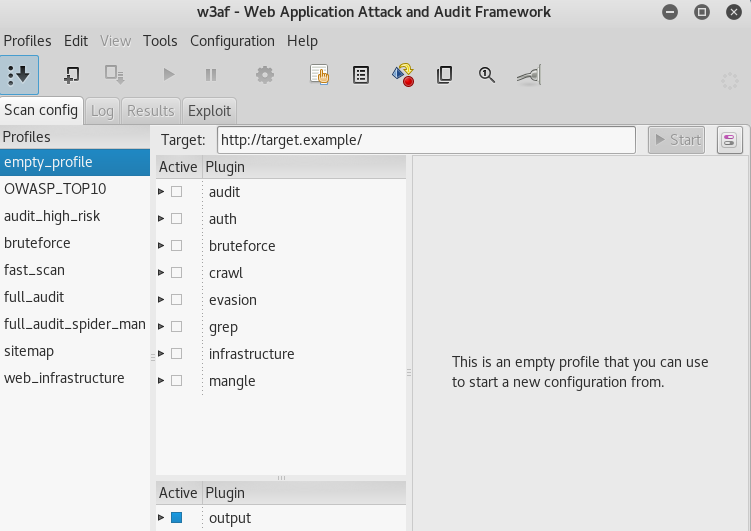
The above command opens W3af interface as shown in the following screenshot.
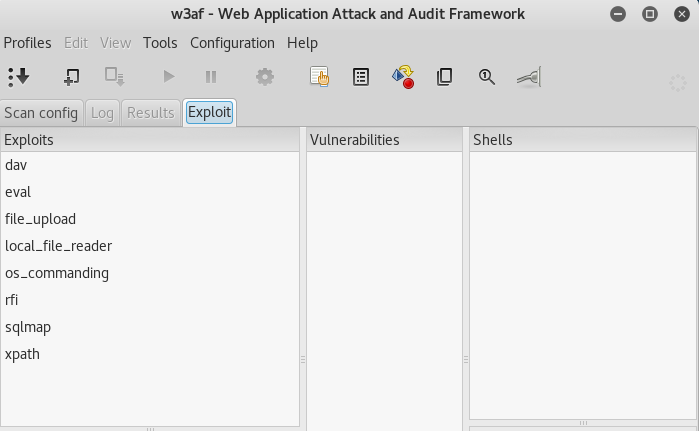
W3af interface has four main sections namely Scanning configuration, Logs, Results, and Exploits. The Scanning configuration (Scan config) section contains profiles and plugins. Profiles are the names given to the pre-built scanning models in the framework. There is an empty profile option that allows the users to design a custom scanning strategy. There are currently eight plugins namely Audit, Auth, Bruteforce, Crawl, Evasion, Grep, Infrastructure, and Mangle. Each plugin scans the target web applications for specific set of vulnerabilities. For example, the Audit plugin scans the most critical vulnerabilities, such as SQL injections, XSS scripts, RFI, LFI etc. The Crawl plugin is designed in such a way that it uses search engines and directories to find and match the information disclosure vulnerabilities. The other important sections of W3af console are Log, Results, and Exploits. The Log section logs any vulnerability or misconfiguration found during the real time scanning process. The Results section contains the final results. The Exploit section contains the tools that can be used to exploit the vulnerabilities found during the scanning process.
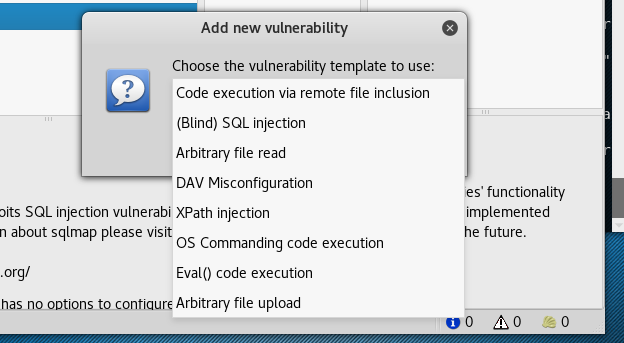
There are pre-selected tools to exploit the opportunities. However, there is an option to add new tools as shown in the following screenshot.
W3af Scanning
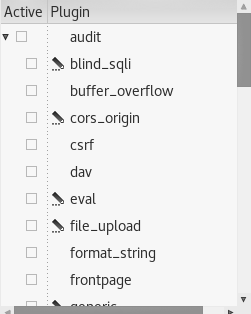
In order to scan the web application, enter the web address in the target field. Select a pre-defined scanning profile or start over by building a new scanning profile using the empty profile option. Select the desired vulnerabilities tests to be performed from the plugins. Each plugin offers selecting all or specific number of vulnerability tests as shown in the following example screenshot.
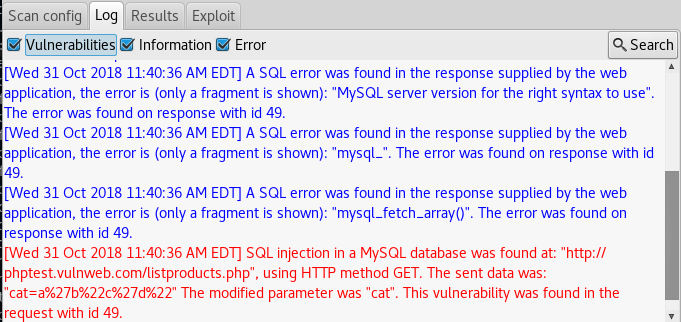
Once configured, hit the start button of the interface to run the desired vulnerabilities scanning tests. Open the log section to see the scanning progress as shown below.
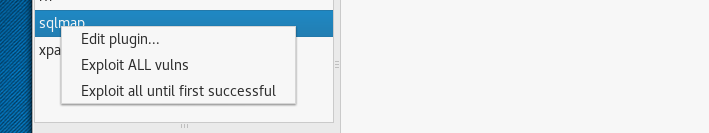
In order to exploit the found vulnerabilities, right click on the desired exploitation tool in the Exploit section and select the required exploitation function as shown in the following screenshot.
Summary
W3af is a web auditing framework that exposes low, medium, and high level vulnerabilities in target web applications during the penetration testing process. The graphics interface of the framework makes it really easy to use. The overall performance of W3af is quite decent.