Cybersecurity is an in-demand skillset. At the same time, the market is competitive. One of the best ways to set … [Read More...]


Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.




Cybersecurity is an in-demand skillset. At the same time, the market is competitive. One of the best ways to set … [Read More...]

Cybersecurity is becoming as one of the hottest job paths in tech. Demand is ever-increasing, but so is competition, as … [Read More...]

React offers strong protections against XSS. However, it's far from perfect, and a variety of workarounds exist to make … [Read More...]
 Loading...
Loading...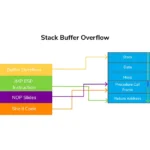
This is the follow-up article to the previous one in which we did Spiking and Fuzzing. In this article, we will perform the next Buffer Overflow Steps which include Finding the OffsetOverwriting the EIPFinding Bad Characters Recap After completing the Spiking and Fuzzing, we know that TRUN is the vulnerable command and the program crashes at around 20500 bytes when the buffer fills. But it did not overwrite the EIP. Since we want to control EIP, we need to know its address. Buffer Overflow Step 3 Finding the Offset For finding the offset, we will use pattern_create tool from Metasploit to create … [Read More...]

The previous blog explains the Stack-Based Buffer Overflow Attack and its steps. In this article, we will understand and perform the first 2 steps, Spiking & Fuzzing in detail. Before proceeding, disable Defender's Real Time Protection so we don't face issues during the process. Buffer Overflow Steps The steps for performing BOF are as follows and we will discuss the first 2 of them in this article SpikingFuzzingFinding OffsetOverwriting the EIPFinding Bad CharactersFinding Right ModuleGenerating Shellcode Setting up environment The very first step is spiking which is the method of finding … [Read More...]

Buffer Overflow Attack is one that most beginners find challenging to understand and perform. This is because it involves a combination of programming, computer architecture, memory, and software security concepts. So, by exploiting this, an attacker can gain unauthorized access to the systems. It is one of the known vulnerabilities and was common a few years ago but still, we can find it in various applications. This BOF article series is inspired by the PEH course by TCM. Buffer Before diving into the attack itself, it is important to understand the terms. A buffer is a memory storage region that … [Read More...]

The most important task for an attacker, after gaining access to a target system or infrastructure, is maintaining access. And later, using persistence to pivot through the internal network and explore more attack surfaces. Persistence and pivoting are integral parts of any attack chain to get the most out of the hack. After gaining access, attackers focus mostly on making persistence to maintain access for a longer period of time. The attackers then utilize persistence to make the compromised host a pivot point and further discover the internal network. Persistence An attacker spends a lot of time finding … [Read More...]

The previous article was about how can we dump the credentials using the super amazing open-source and free tool Mimikatz. We can utilize those dumped NTLM hashes in multiple attacks and further movement. But, one of the cool attacks is the famous Golden Ticket Attack. This attack is famous for its nature which allows the attacker to have complete access to the entire domain. The attacker just needs to have the Golden Ticket. Golden Ticket You must be wondering what is a Golden Ticket. But before that, let's have a bit of background details. Active Directory uses Kerberos as the authentication protocol to … [Read More...]