Hacking Jupyter notebooks is easy and fun, thanks to the lack of any protections by default when you run a notebook. So … [Read More...]

Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.



Hacking Jupyter notebooks is easy and fun, thanks to the lack of any protections by default when you run a notebook. So … [Read More...]

Urbit is a peer-to-peer computing platform that reimagines the idea of an operating system from the ground up. Hacking … [Read More...]

Stegonagraphy is the art of hiding information in plain sight. Unlike crypto, which hides data by protecting it with … [Read More...]
 Loading...
Loading...
So far, in the post-compromise AD enumeration, we have been using the PowerView tool to gather information. That tool was completely CLI-based and needed commands to gather the information. As specified in the previous article, the next tool we will be using is BloodHound. BloodHound BloodHound is a single-page Javascript web application, built on top of Linkurious, compiled with Electron, with a Neo4j database fed by a C# data collector. It is an Active Directory (AD) reconnaissance tool that can reveal hidden relationships and identify attack paths within an AD environment. BloodHound uses graph … [Read More...]
This video shows you step by step how hackers write malware with ChatGPT and will show you what you need to know to defend yourself against it. … [Read More...]

In the initial attack vectors, we were able to compromise a user (Frank Castle). All this by gaining its hash through LLMNR Poisoning and then cracking the hash to get a plaintext password. Also using SMB Relay Attack to gain access to the machine along with dumping the SAM file hashes. Not only this but going through an IPv6 attack using mitm6 and ntlmrelayx, taking over DNS and capturing almost all information about the domain. Now, what can we do once we have a compromise? How can we enumerate the network using these compromises? In this article, we will talk about Post-Compromise AD Enumeration. For that, we … [Read More...]
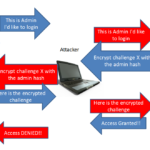
The previous article was about LLMNR Poisoning and how can we dump NTLMv2 hashes and later on crack them. Not always you will be able to crack the hashes. Well, in this situation by just having the hash, you can perform an SMB Relay attack. SMB Relay After getting the hash(es) from the responder, instead of cracking them, we can relay those hash(es) to specific machines to gain access to those machines. It is a nice way around when cracking the hash seems unfeasible. SMB Signing SMB Signing is a packet-level protocol. So, when relaying the user credentials, it checks for if the packet is signed by the … [Read More...]
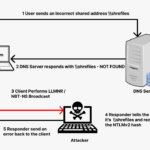
In the previous article about active directory lab setup, we set up the lab environment to perform attacks. This article will cover LLMNR Poisoning and how can we capture NTLMv2 hashes and later crack them. We will be abusing the windows features not any misconfigurations. LLMNR DNS is used for name resolution. But what happens when the DNS fails to do so? Here comes the role of LLMNR (Link-Local Multicast Name Resolution) which is a windows component that acts as a host discovery method in windows systems. LLMNR and NBT-NS (NetBios Name System) are the two alternatives for DNS and can identify the hosts in … [Read More...]