The previous article was about LLMNR Poisoning and how can we dump NTLMv2 hashes and later on crack them. Not always you … [Read More...]

Learn ethical hacking, penetration testing, cyber security, best security and web penetration testing techniques from best ethical hackers in security field.



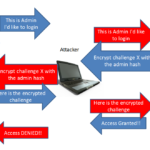
The previous article was about LLMNR Poisoning and how can we dump NTLMv2 hashes and later on crack them. Not always you … [Read More...]
In the previous article about active directory lab setup, we set up the lab environment to perform attacks. This article … [Read More...]

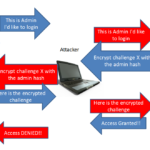
Previously, we did a full demonstration of an SMB Relay Attack. And how it is possible to exploit SMB by relaying the … [Read More...]
 Loading...
Loading...
As Russia tightens its grip over Ukraine, the world watches. All are asking what tragic news will come next. But not all only watch. While most wait, many fight. Some for money, others for patriotism, and many more under the orders of armies. A war that has split the world has also split the world's hackers. A bank, the navy, and the Kremlin have been visible targets in this battle of bullets and propaganda. We are going to unravel the forces seeking to fight Russia on the battle field of the 21st century: cyber space, where hackers are targeting Russia with malware and DDoS attacks. Let's start with the … [Read More...]
This is the story of how I made $500 from finding a simple bug. Before I show you how I won a prototype pollution bug bounty, let's start out with some technical background. The hash map is a basic, highly useful data structure. All modern coding languages support it in some way or another. In Python, you have the dictionary. In PHP, the "associative array". For use JavaScripters, we use the humble Object. This creates an issue. Think about it - the data structure we use to create hash maps is also an integral part of how the language works. Does this create security bugs? You bet it does! If we let a user … [Read More...]
Sourcegraph is an open source code search, navigation, and intelligence engine. It helps developers Increase programming productivityImprove code qualitySearching across massive codebasesComprehending unfamiliar codeFast code reviewsBatch changes and many more Many big companies are already using sourcegraph to understand, fix, and automate their entire codebases. Exploiting Sourcegraph is interesting as it gives direct RCE. Vulnerability Recently, a vulnerability in sourcegraph prior to version 3.37 is found. The vulnerability exists in the gitserver service and allows the attacker to gain remote … [Read More...]

Web apps don't always serve the "live" version of every page to save CPU cycles. Some parts of a site, like CSS files, don't tend to change all that much. So the dev can teach the backend to load these files directly from memory if requested often. This is to prevent slow disk reads. Web cache poisoning occurs when you trick the server into caching a resource containing content supplied by the user and serving that to others, even though it's not how the page should look. Of course, caching hacks are nothing new. Like in 1999, when a DNS cache poisoning attack let hackers deface Hillary Clinton's website. … [Read More...]

Delivery is an easy level box that is beginner friendly with assigned IP of 10.10.10.222. It requires creative thinking to solve it. It presents a helpdesk and a Mattermost instance. Creating ticket on helpdesk, mail is received to update the ticket that can be used to create Mattermost account. The Mattermost contains the important conversation disclosing SSH creds. These creds will be used to access the box and then privilege escalation will be done with some cool stuff. nmap scan First run nmap scan with following command nmap -sV -sC -A -T4 -p- -oA nmap_scan 10.10.10.222 Delivery Website Go … [Read More...]